Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Crypto Money Grabber 2025
In the evolving landscape of cybercrime, Crypto Money Grabber 2025 tools designed to steal cryptocurrency have become a significant threat. Among these, specialized malware known as “crypto money grabbers” has emerged as a preferred weapon for attackers targeting digital wallets and exchanges. These tools exploit vulnerabilities in both individual users and systems to siphon funds, […]
Echelon Stealer-v5
Information stealers have become one of the most pervasive threats in today’s cyber landscape, with sophisticated variants like this Echelon Stealer-v5 playing a significant role in credential theft and financial fraud. Unlike ransomware that announces its presence, these stealthy threats operate silently, harvesting sensitive data that fuels further criminal activity. This particular stealer has gained […]
Mirai Eye Rat 2025 Cracked
Mirai Eye Rat 2025 has emerged as a dangerous Remote Access Trojan (RAT) frequently deployed in targeted cyberattacks, particularly in espionage and data theft campaigns. Unlike generic malware, Mirai Eye is designed for stealth and persistence, allowing attackers to maintain long-term access to compromised systems. It is commonly used against high-value targets, including government agencies, […]
Gold Alduin Botnet 2025
Gold Alduin Botnet 2025 remain one of the most potent threats in cybersecurity, enabling large-scale attacks through networks of compromised devices. One such example is a sophisticated modular botnet frequently used in credential theft, cryptocurrency mining, and distributed denial-of-service (DDoS) attacks. Its ability to evade detection while maintaining persistent control over infected machines makes it […]
Dangerous Rat-v5 Cracked
Remote Access Trojans (RATs) are among the most dangerous tools in a cybercriminal’s arsenal, enabling stealthy, long-term control over compromised systems. Unlike traditional malware that may simply corrupt files or display ransomware messages, Dangerous Rat-v5 allow attackers to operate undetected, performing espionage, data theft, and even lateral movement across networks. They are frequently used in […]
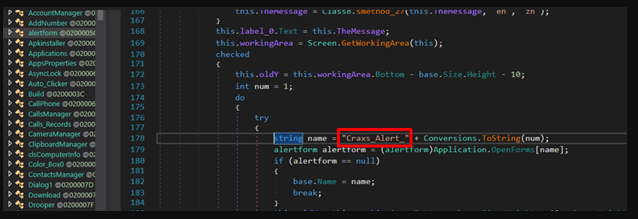
Agent tesla builder-3-2-5-5 cracked
In the ever-evolving world of cyber threats, agent-tesla-builder has become a significant concern for security professionals. These tools allow attackers to create customized malware strains with minimal effort, enabling widespread espionage, data theft, and system compromise. One such example is a well-known Remote Access Trojan (RAT) builder, frequently distributed on underground forums and used in […]
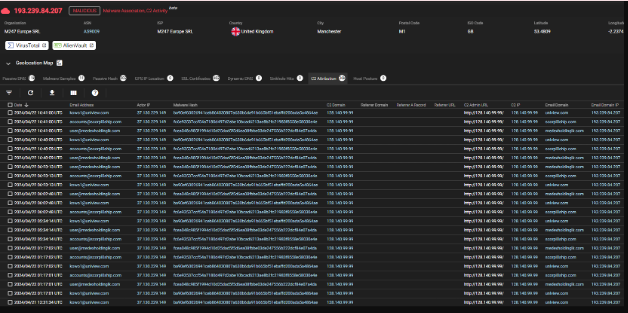
Azorult Stealer v3.4 Cracked
In the ever-evolving landscape of cybercrime, information-stealing malware has become one of the most pervasive threats to both individuals and organizations. Among these threats, a particularly dangerous strain has emerged as a favorite among cybercriminals due to its versatility and effectiveness. This Azorult Stealer v3.4 Cracked, often distributed through phishing campaigns and exploit kits, specializes […]
Trillium-security-multisploit-tool-v4-private-edition
In today’s evolving threat landscape, advanced exploitation frameworks have become a critical tool for both security professionals and malicious actors. One such tool, often referenced in penetration testing and cyberattack simulations, is a Trillium-security-multisploit designed to automate and streamline the exploitation of multiple vulnerabilities. These tools play a dual role—helping ethical hackers assess security defenses while […]