Hacking WEP/WPA/WPA2 WiFi Networks
Hacking WEP/WPA/WPA2 networks, particularly targeting WEP, WPA, and WPA2 security protocols, remains a significant threat in cybersecurity due to the widespread use of wireless networks. Weak encryption, poor password practices, and protocol vulnerabilities make these networks prime targets for attackers seeking unauthorized access, data interception, or network infiltration. While WEP is now largely obsolete due to its well-known flaws, WPA and WPA2, despite being more secure, can still be compromised through techniques like brute-force attacks, dictionary attacks, or exploiting implementation weaknesses. Such attacks can lead to credential theft, man-in-the-middle attacks, or broader network breaches, emphasizing the need for robust security measures like WPA3 and strong authentication mechanisms.
Specialized software tools are often used to assess and exploit vulnerabilities in WiFi networks, primarily for penetration testing, security research, or malicious purposes. These tools automate the process of capturing network handshakes, cracking encryption keys, and launching attacks against access points. While ethical hackers use them to identify and fix security flaws, attackers leverage them to gain unauthorized access. The software typically operates by monitoring wireless traffic, injecting packets, and employing cryptographic attacks to recover passwords. Its effectiveness depends on factors like encryption strength, password complexity, and network configuration.
Key Features of Hacking WEP/WPA/WPA2
| Feature | Description |
| Packet Capture | Monitors and records wireless traffic to analyze encryption handshakes. |
| Brute-Force Attack | Systematically tests all possible password combinations to crack keys. |
| Dictionary Attack | Utilises precomputed wordlists to guess passwords efficiently. |
| Handshake Capture | Extracts authentication handshakes for offline cracking. |
| Packet Injection | Sends forged packets to disrupt or manipulate network communication. |
| GPU Acceleration | Leverages GPU power to speed up password cracking. |
| Multiple Protocol Support | Targets WEP, WPA, WPA2, and sometimes WPA3 (if vulnerable). |
| User-Friendly Interface | Provides CLI or GUI options for ease of use. |
How the Hacking WEP/WPA/WPA2 Works: Techniques and Functionality
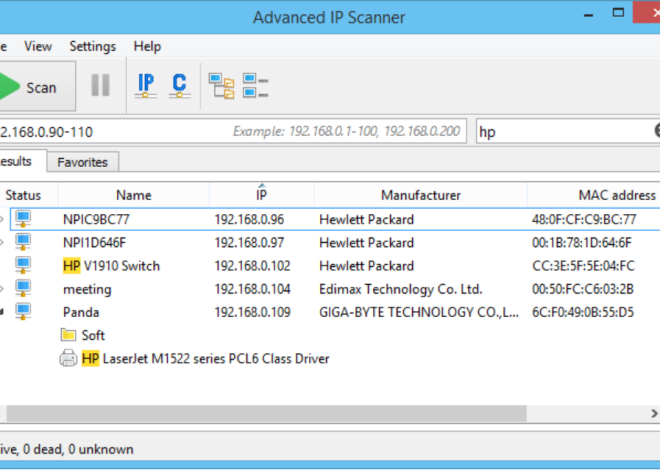
Network Discovery and Monitoring
The software scans for nearby WiFi networks using the wireless adapter in monitor mode, which enables it to detect all available access points (APS) and connected clients. It collects essential details, such as the BSSID (Access Point MAC address), signal strength, encryption type, and channel frequency.
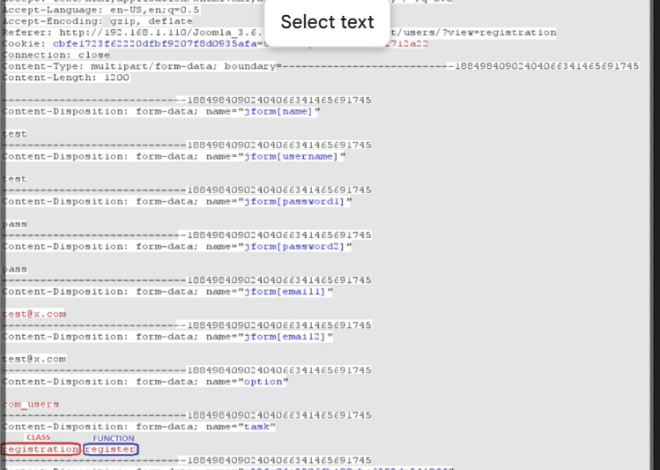
Handshake Capture
For WPA/WPA2 networks, the software waits for a client to authenticate with the access point (AP). It captures the four-way EAPOL handshake, which contains the encrypted password hash. If no clients are active, the tool may deauthenticate connected devices (via packet injection) to force a reconnection, triggering the handshake.
Offline Cracking
The captured handshake is saved for offline analysis. The software then attempts to crack the password using:
- Dictionary Attacks: Compares the handshake against a predefined list of common passwords.
- Brute-Force Attacks: Tests every possible combination of characters (computationally intensive).
- Rainbow Tables: Uses precomputed hash tables for faster cracking (less common for WPA/WPA2 due to salting).
Exploiting WEP Weaknesses
For WEP networks, the software exploits the flawed RC4 encryption by capturing a large number of IVS (Initialization Vectors) to deduce the key statistically. Tools may use ARP replay attacks to generate more traffic and accelerate IV collection.