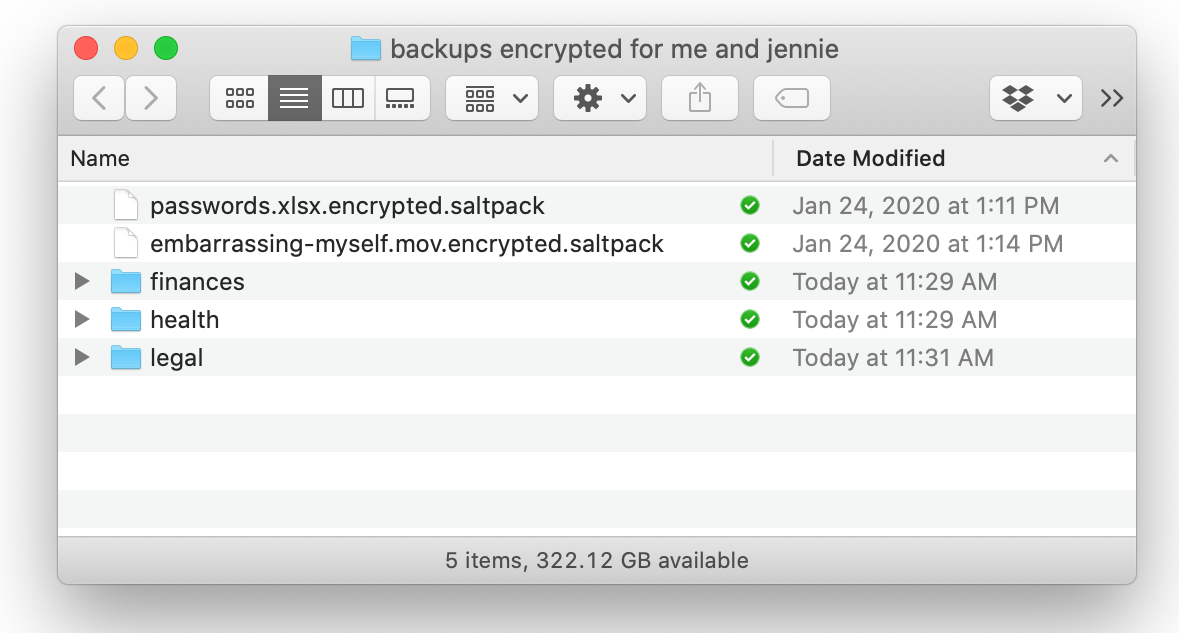
KeyBase v1.5 Beta
KeyBase v1.5 Beta represents a cutting-edge advancement in encrypted communication and identity verification, offering users a secure platform for messaging, file sharing, and cryptocurrency transactions. Designed with privacy-first principles, this beta release introduces enhanced security features while maintaining user-friendly accessibility. As digital privacy concerns grow, understanding KeyBase’s capabilities helps both security professionals and everyday users protect their […]
SMS Bomber for all over the world 2024
In today’s digital age, communication tools have evolved rapidly, and so have the methods to exploit them. One such controversial tool is the SMS Bomber, which has gained attention worldwide for its ability to flood a target phone number with multiple messages. While some use it for pranks, others exploit it for malicious purposes. This article […]
Anubis Android Banking Botnet v.2.5 with Tutorial
Anubis is a sophisticated Android banking malware that has evolved into a powerful botnet, capable of stealing sensitive financial data, logging keystrokes, and remotely controlling infected devices. Initially discovered in 2017, Anubis v2.5 represents an advanced iteration with enhanced evasion techniques and expanded attack vectors. This article explores its functionality, features, and operational mechanics for educational […]
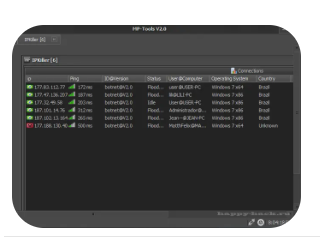
IP Killer 2
IP Killer 2 is a powerful network stress-testing tool designed to simulate high-intensity traffic floods, primarily used for penetration testing, cybersecurity research, and network hardening. While it can be misused for disruptive purposes, ethical hackers and security professionals utilize it to assess network resilience against DDoS (Distributed Denial of Service) attacks. This article explores its functionalities, legitimate applications, and […]
Booters Pack Collection 2024
The Booters Pack Collection 2024 is a compilation of powerful network stress-testing tools designed for cybersecurity professionals, penetration testers, and ethical hackers. These tools simulate DDoS (Distributed Denial of Service) attacks, allowing experts to assess network vulnerabilities, test mitigation strategies, and improve defensive measures. While they can be misused, this article focuses on their legitimate applications in security research and […]
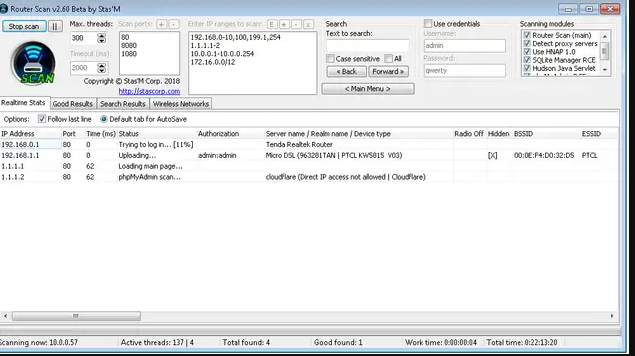
Router Scan v2.60
Router Scan v2.60 is a specialized security tool developed for penetration testers, ethical hackers, and network administrators to identify and assess vulnerabilities in routers and network devices. By automating the discovery of misconfigured routers, default credentials, and exposed services, Router Scan plays a vital role in hardening network infrastructure and preventing unauthorized access. Download Link […]
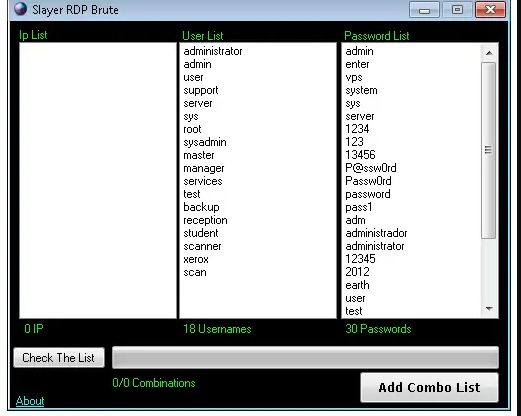
Slayer RDP Scanner and Bruter 2024
In today’s cybersecurity landscape, securing Remote Desktop Protocol (RDP) services is more critical than ever. Slayer RDP Scanner and Bruter 2024 is a powerful tool designed specifically for ethical hackers, penetration testers, and IT security professionals. It enables efficient scanning, brute-force testing, and auditing of RDP services, helping organizations detect and mitigate vulnerabilities before malicious […]
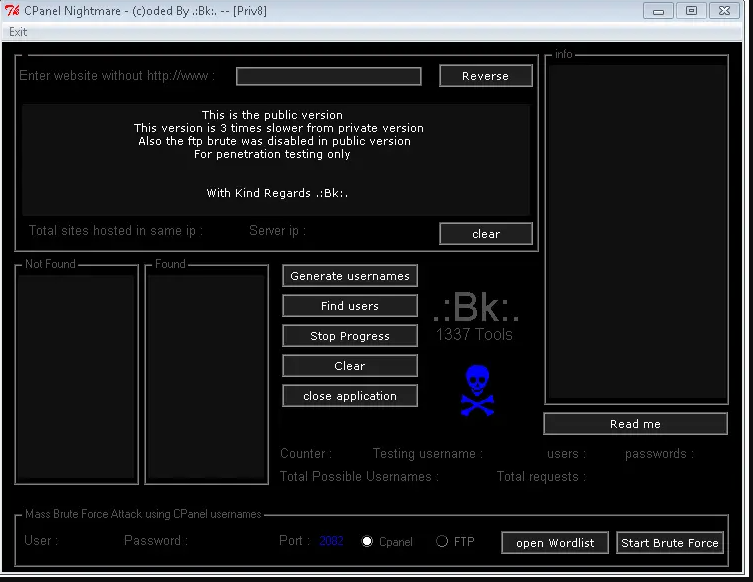
cPanel Nightmare 2024
cPanel Nightmare 2024 refers to a series of drastic updates and policy shifts introduced by cPanel that sparked significant backlash within the web hosting community. These updates included unexpected price hikes, restrictive new policies, and compatibility issues that disrupted workflows for developers, hosting providers, and system administrators. As a result, many users began exploring alternative […]
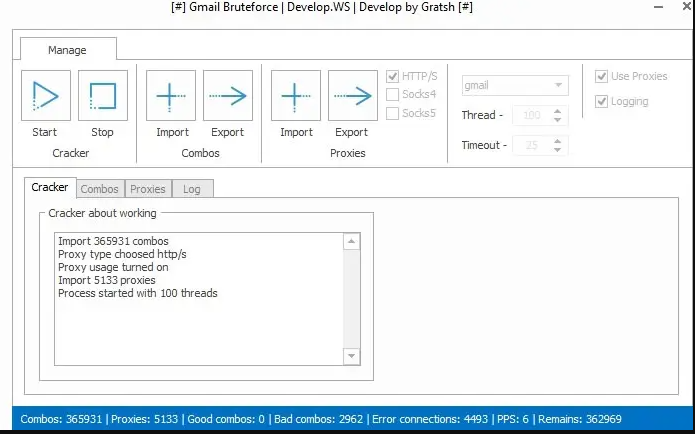
Gmail Bruteforce 2024
Gmail Bruteforce 2024 refers to sophisticated tools and techniques designed to crack Gmail passwords through automated trial-and-error methods. While these tools have legitimate use cases in cybersecurity assessments, they are also exploited by malicious actors to gain unauthorized access. This article explores how Gmail Bruteforce 2024 works, its advanced features, ethical considerations, and preventive strategies. […]
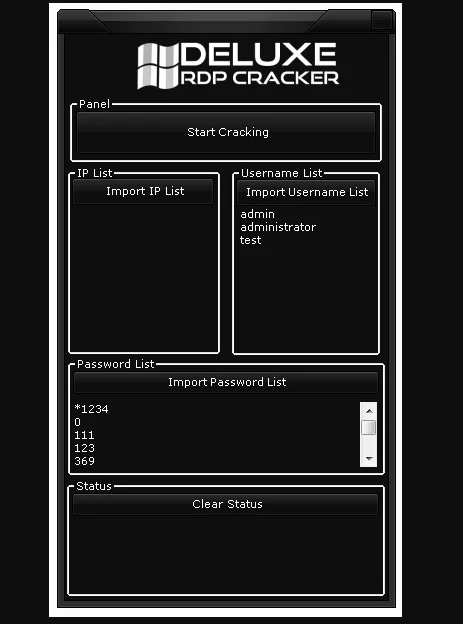
Deluxe RDP Cracker 2024
As organizations increasingly rely on Remote Desktop Protocol (RDP) for remote access and administration, the risk of unauthorized access via weak credentials also rises. Deluxe RDP Cracker 2024 is a professional-grade tool designed to assess RDP security by simulating brute-force attacks—intended solely for ethical hacking, security research, and authorized penetration testing. Download Link 1 Download […]