Mail Brute Engine 2024
In today’s threat-prone digital environment, email remains a primary target for attackers. To combat this, ethical hackers and penetration testers rely on powerful, intelligent tools like Mail Brute Engine 2024—a next-generation brute-force engine built specifically for email account security testing. With support for multiple protocols and AI-enhanced attacks, this tool helps uncover vulnerabilities in email […]
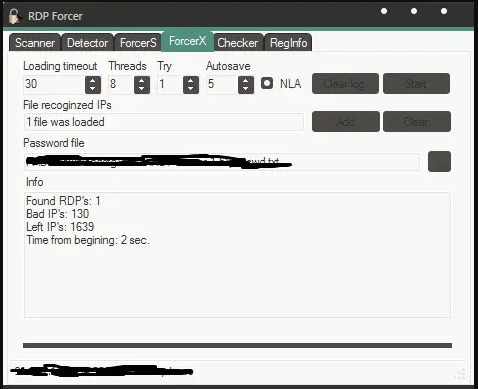
RDP ForcerX 1.5
In the age of remote work and cloud-based infrastructure, securing Remote Desktop Protocol (RDP) services is critical. RDP ForcerX 1.5 is a high-performance penetration testing tool designed to evaluate the strength of RDP login credentials. Whether you’re conducting internal audits or authorized penetration tests, this tool provides a controlled and efficient way to detect weak […]
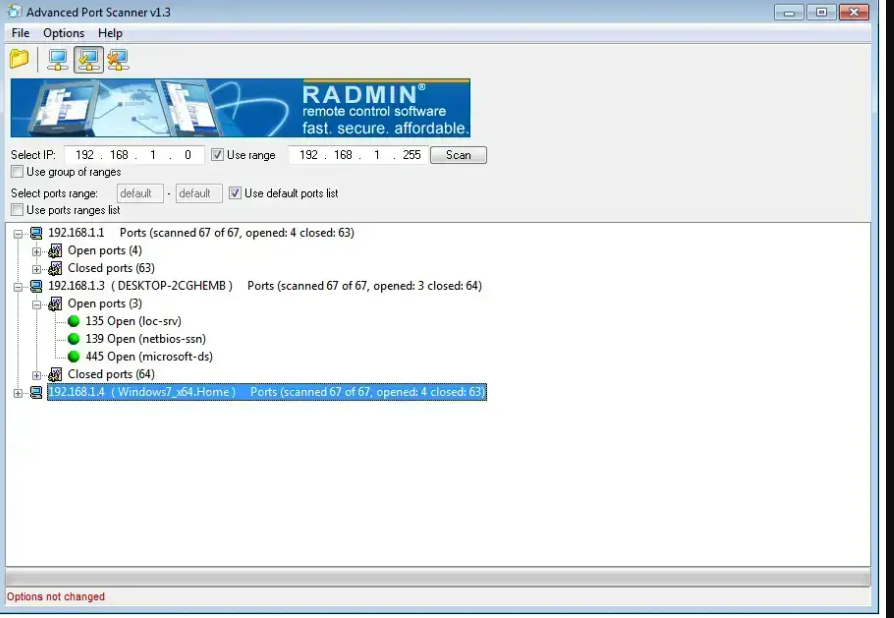
Advanced PortScanner 2024
In the evolving landscape of cybersecurity, proactive network analysis is key to defending against cyber threats. Advanced PortScanner 2024 is a next-generation port scanning utility built for ethical hackers, IT professionals, and network administrators to identify, analyze, and secure open ports and services across any network. Powered by AI and stealth scanning technology, it provides […]
Hooker Keylogger 2024
In an era where digital security and surveillance are paramount, Hooker Keylogger 2024 emerges as a powerful tool designed for discreet monitoring. Whether for parental control, employee oversight, or personal security, this advanced keylogger offers unmatched stealth and functionality. What Is Hooker Keylogger 2024? Hooker Keylogger is a cutting-edge surveillance software that records keystrokes, captures […]
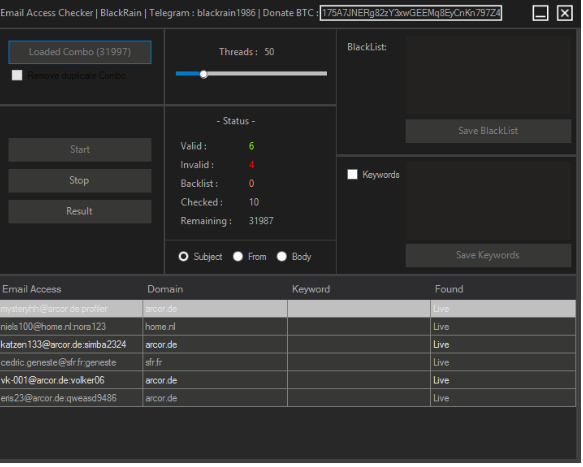
Email Access Checker 2023
In an era of rising cyber threats, email security is more critical than ever. Email Access Checker 2023 is a robust, cross-platform solution designed to monitor, detect, and respond to unauthorized access across your email accounts. Whether you’re an individual concerned about privacy or a business protecting sensitive communications, this tool ensures proactive defense with […]
ARES RAT v1.2.1 Cracked
ARES RAT (Remote Access Trojan) is a powerful surveillance and control malware used for remote system administration—often exploited for unauthorized access. The cracked v1.2.1 version circulates in underground forums, allowing hackers to bypass licensing restrictions. While originally marketed as a legitimate remote tool, its misuse poses severe cybersecurity threats, making it essential for security professionals to understand […]
DaRKDDoSeR 5.6c Cracked
DaRKDDoSeR 5.6c Cracked is a modified version of a network stress-testing tool that simulates DDoS (Distributed Denial of Service) attacks. While the original software was designed for legitimate penetration testing, cracked versions often circulate in underground forums, posing significant risks. This article examines its technical aspects, ethical concerns, and defensive applications for cybersecurity professionals. Download Link 1 Download Link 2 […]
Top Powerfull DDOs attack tools 2024
Distributed Denial-of-Service (DDoS) attacks remain one of the most disruptive threats to online services, overwhelming networks with malicious traffic. While ethical hackers and cybersecurity professionals use these tools for stress testing and defense simulations, malicious hackers exploit them to take down websites and services. This article explores the most powerful DDoS tools in 2024, their […]
Combat SMS Bomber 2024 with source
In today’s digital age, cybersecurity and ethical hacking tools are gaining prominence. One such tool is Combat SMS Bomber 2024, designed for testing phone number vulnerabilities by sending multiple SMS messages. While it has legitimate uses in penetration testing, it can also be misused for harassment. This article explores its features, purpose, and ethical implications. […]
WordPress XML-RPC + WP-LOGIN Bruteforce [10 Macros] v2.11
WordPress XML-RPC + WP-LOGIN Bruteforce [10 Macros] v2.11 is a specialized security assessment tool designed to test the resilience of WordPress websites against brute-force attacks. By targeting both the traditional wp-login.php and XML-RPC endpoints, it helps identify weak credentials and misconfigurations that could lead to unauthorized access. This tool is strictly intended for ethical hacking […]
















![WordPress XML-RPC + WP-LOGIN Bruteforce [10 Macros] v2.11](https://blackhatus.com/wp-content/uploads/2025/07/WordPress-XML-RPC-WP-LOGIN-Bruteforce-10-macros-v.2.11.png)