Acunetix Web Vulnerability Scanner v13.0.2
Acunetix Web Vulnerability Scanner is a leading automated web security testing solution used by cybersecurity professionals and developers worldwide. It is specifically designed to identify, assess, and remediate vulnerabilities across websites, web applications, and APIs. Acunetix offers deep scanning capabilities that help detect high-risk issues like SQL injection, XSS, and security misconfigurations, ensuring comprehensive protection […]
Venom RAT v5.6 Cracked
Venom RAT V5.6 Cracked has emerged as a formidable threat in the cybercrime landscape, representing a cracked version of a commercial remote administration tool now weaponized for malicious purposes. This sophisticated malware has been actively deployed in attacks against businesses, government agencies, and individual users, demonstrating alarming capabilities in stealth and persistence. Security analysts have […]
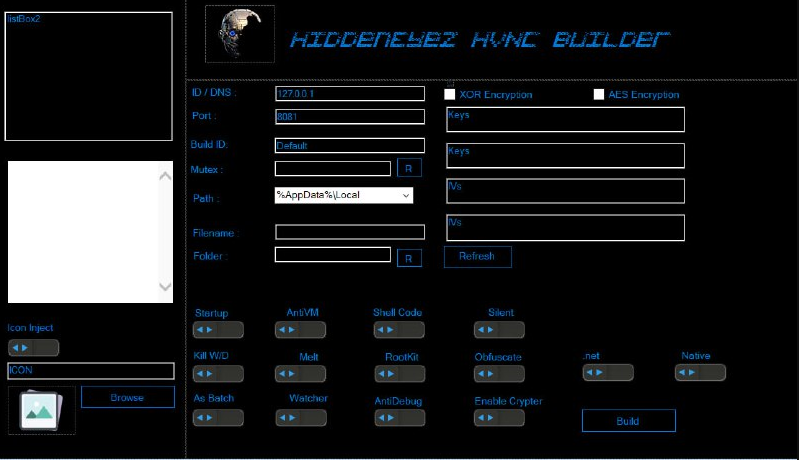
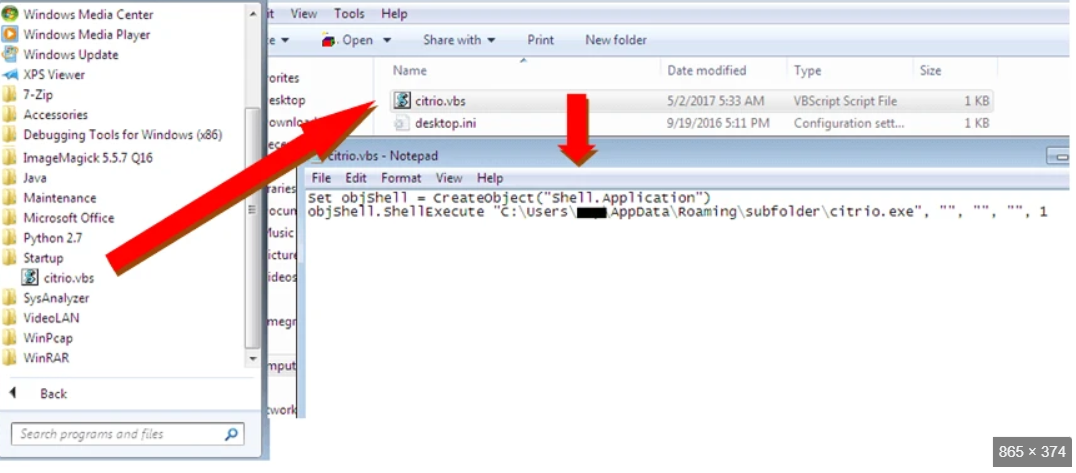
HIDDENZ HVNC TOOLS 2025
The cybersecurity landscape faces an escalating threat from advanced remote access tools designed to operate undetected on compromised systems. Among these, HIDDENZ HVNC TOOLS 2025 represents a sophisticated evolution in stealth malware technology, enabling attackers to maintain persistent, invisible access to victim machines. This toolkit leverages Hidden Virtual Network Computing (HVNC) technology to bypass traditional […]
Loki Stealer V5 Final Release
Cyber threats continue to evolve, with malicious actors leveraging advanced tools to bypass security measures and compromise systems. One such tool, often distributed through underground forums, is designed to steal sensitive information while evading detection. Loki Stealer V5 Final Software exemplifies the growing sophistication of modern cyberattacks, where stealth and functionality combine to target sensitive information, […]
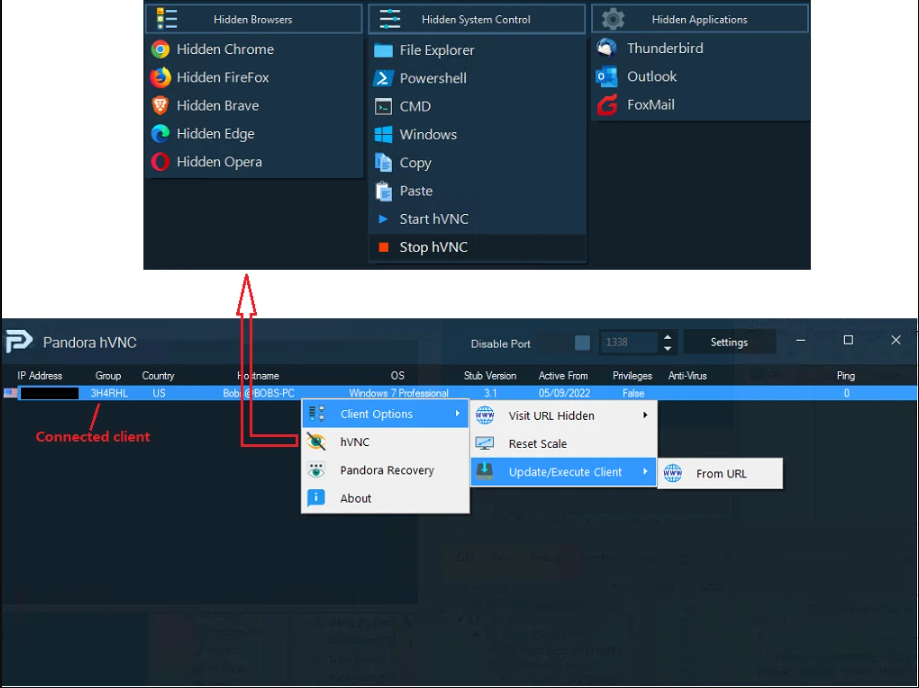
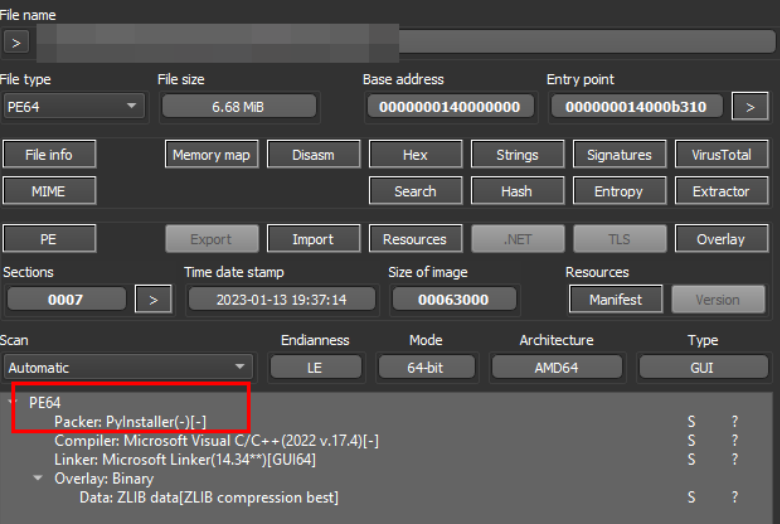
bitrat HVNC RAT 2025 Cracked with Source code
The underground cybercrime ecosystem continues to evolve with increasingly sophisticated tools becoming available to malicious actors. Among these, BitRAT HVNC RAT 2025 represents a particularly alarming development, combining advanced remote access capabilities with cutting-edge evasion techniques. This malware variant stands out due to its inclusion of Hidden Virtual Network Computing (HVNC) functionality, allowing attackers to […]
CREAL STEALER 2025
Cybercriminals are increasingly leveraging advanced information-stealing malware to compromise sensitive data, and one such prominent threat is “CREAL STEALER 2025.” This malware exemplifies the growing sophistication of modern cyberattacks, targeting credentials, financial data, and other valuable information from infected systems. Unlike generic stealers, this tool employs evasion techniques to avoid detection while efficiently exfiltrating data […]
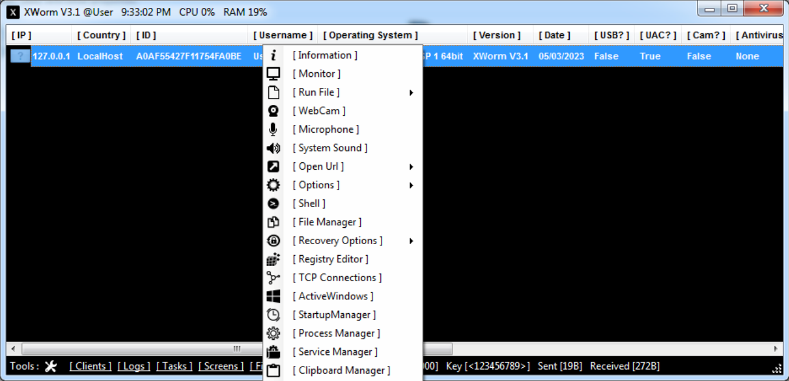
XWorm V3.1 Cracked
The cybersecurity landscape faces constant evolution as malware developers refine their tools to bypass modern defenses. Among these threats, XWorm V3.1 has emerged as a particularly dangerous remote access trojan (RAT) circulating in underground forums. This cracked version of sophisticated malware has lowered the barrier to entry for cybercriminals, enabling even novice attackers to deploy […]
Heat Clipper 2025
As cryptocurrency adoption grows, cybercriminals have developed increasingly sophisticated tools to intercept and hijack digital transactions. Among these threats, Heat Clipper 2025 has emerged as a particularly insidious form of malware that specializes in cryptocurrency theft through clipboard manipulation. Unlike traditional banking trojans that rely on keylogging or phishing, this malware operates silently in the […]
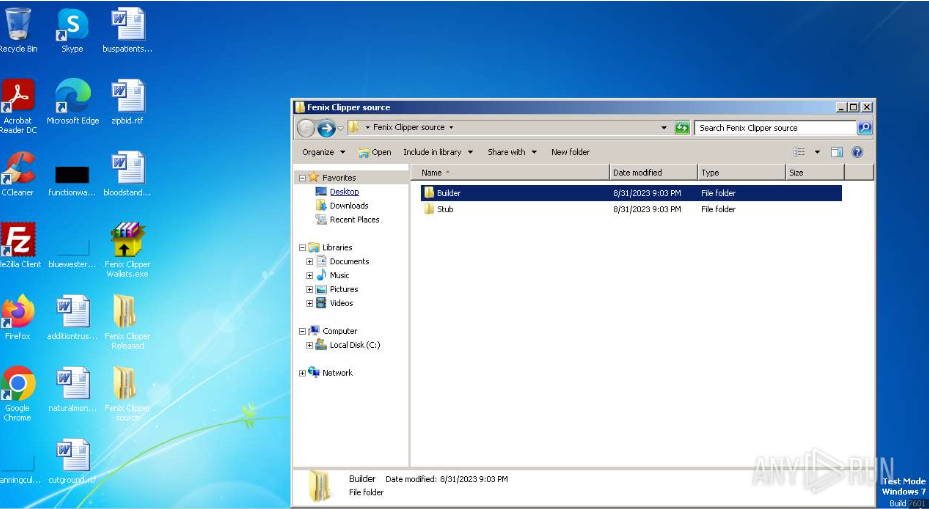
Fenix Clipper Wallets 2025
Fenix Clipper Wallets 2025 has seen an increase in the use of advanced malware tools designed to bypass security measures and steal sensitive data. Among these, a notable threat is a malicious software strain that specializes in credential theft and financial fraud. Often distributed through phishing campaigns or disguised as legitimate applications, this malware has […]
Klimt Stealer 2025
The cybercrime landscape has seen a surge in sophisticated information stealers designed to harvest valuable data with surgical precision. Among these threats, Klimt Stealer 2025 has emerged as a particularly dangerous tool, combining advanced data extraction capabilities with robust evasion techniques. This malware represents the next evolution of credential stealers, moving beyond simple password grabbing […]