Infected Zone OS v1.1.0.1
In the ever-evolving landscape of cyber threats, malicious actors continuously develop and deploy specialized tools to exploit vulnerabilities and maintain control over compromised systems. Among these tools is a custom operating system tailored for cybercriminal activities, often referred to in underground communities as an “Infected Zone OS v1.1.0.1.” This platform is designed to facilitate large-scale […]
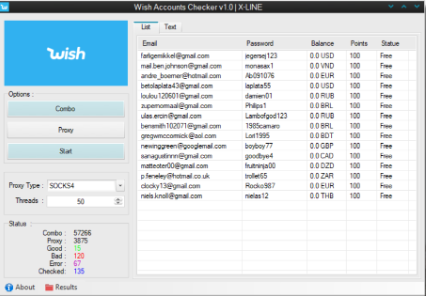
WISH ACCOUNT CHECKER 2025
The rise of e-commerce platforms has led to a corresponding surge in cybercriminal tools designed to exploit these digital marketplaces. Among these threats, automated WISH ACCOUNT CHECKER 2025 have become particularly prevalent in 2025, allowing attackers to systematically test stolen credentials against retail platforms. These tools serve as the first stage in sophisticated fraud chains, allowing […]
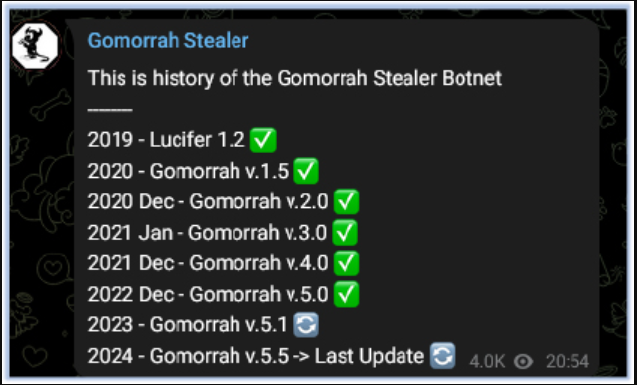
Gomorrah Stealr 4.0 Cracked
Information stealers have become one of the most pervasive threats in the cybercrime landscape, enabling attackers to harvest sensitive data for financial gain or further exploitation. Cracked or pirated versions of such malware, often distributed through underground forums, lower the barrier to entry for aspiring cybercriminals. The latest iteration of Gomorrah Stealr 4.0 demonstrates improved […]
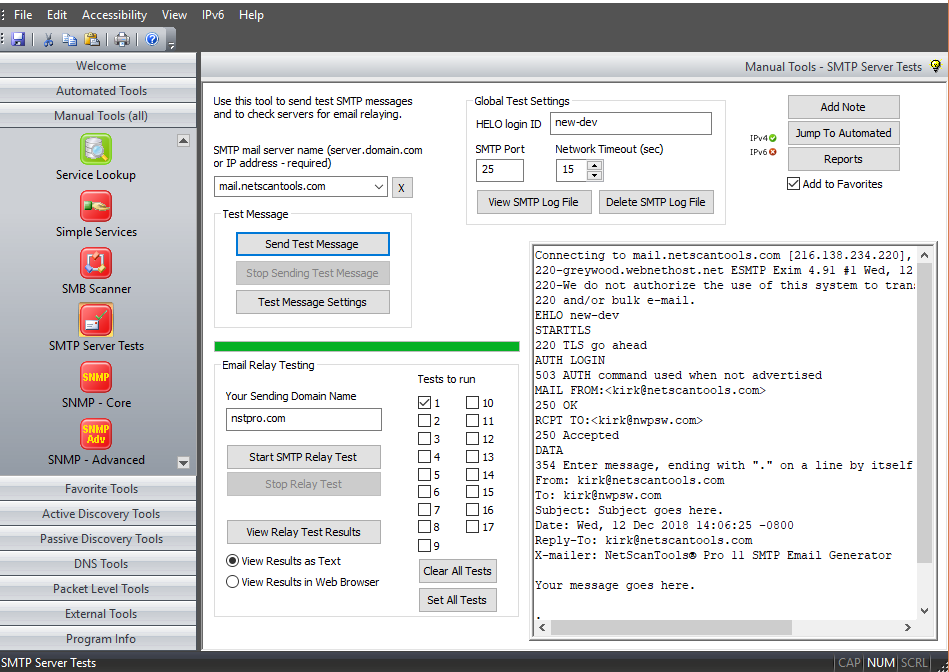
Smtp Checker 2025
Email remains one of the most critical communication channels for both individuals and organizations, making email infrastructure a prime target for cybercriminals. In 2025, specialized tools designed to test and exploit Smtp Checker 2025 (Simple Mail Transfer Protocol) servers have become increasingly sophisticated, playing a pivotal role in modern cyberattacks. These tools enable threat actors […]
CEH V11 EC-COUNCIL CERTIFIED ETHICAL HACKER
The CEH v11 (Certified Ethical Hacker) certification by EC-Council is a globally recognized program designed to train cybersecurity professionals in identifying and mitigating vulnerabilities in modern systems. As cyberattacks become increasingly sophisticated, ethical hacking tools and methodologies—often covered in resources like the EC-Council Certified Ethical Hacker (CEH V11)— play a crucial role in both offensive […]
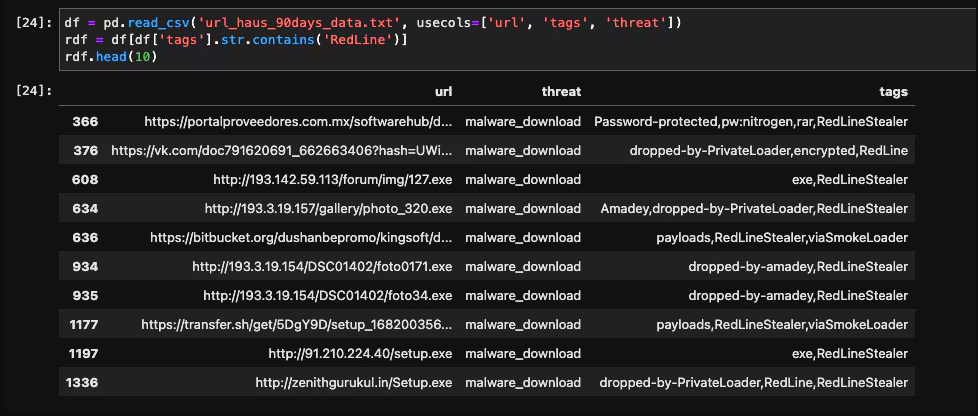
RedLine Stealer 2025 Cracked
The cybercrime landscape continues to evolve with increasingly sophisticated data theft tools, and Redline Stealer 2025 Cracked has emerged as one of the most dangerous information stealers in modern cyberattacks. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful attack tools at minimal cost. Redline Stealer 2025 […]
Hacking WEP/WPA/WPA2 WiFi Networks
Hacking WEP/WPA/WPA2 networks, particularly targeting WEP, WPA, and WPA2 security protocols, remains a significant threat in cybersecurity due to the widespread use of wireless networks. Weak encryption, poor password practices, and protocol vulnerabilities make these networks prime targets for attackers seeking unauthorized access, data interception, or network infiltration. While WEP is now largely obsolete due […]
Black Binder 2025
Cybercriminals are increasingly relying on sophisticated binding tools to conceal malicious payloads within seemingly legitimate files, creating a significant challenge for modern cybersecurity defenses. These advanced Black Binder 2025 applications have become a critical component in the malware delivery chain, enabling attackers to bypass traditional security measures by exploiting the trust users place in common […]
HiveRAT Cracked 2025
In the underground cybercrime ecosystem, cracked versions of legitimate remote administration tools have become a growing threat when weaponized for malicious purposes. One such modified HiveRAT Cracked 2025 variant has gained notoriety among threat actors for its enhanced stealth capabilities and affordability on dark web markets. This repurposed software exemplifies how cybercriminals are leveraging cracked […]
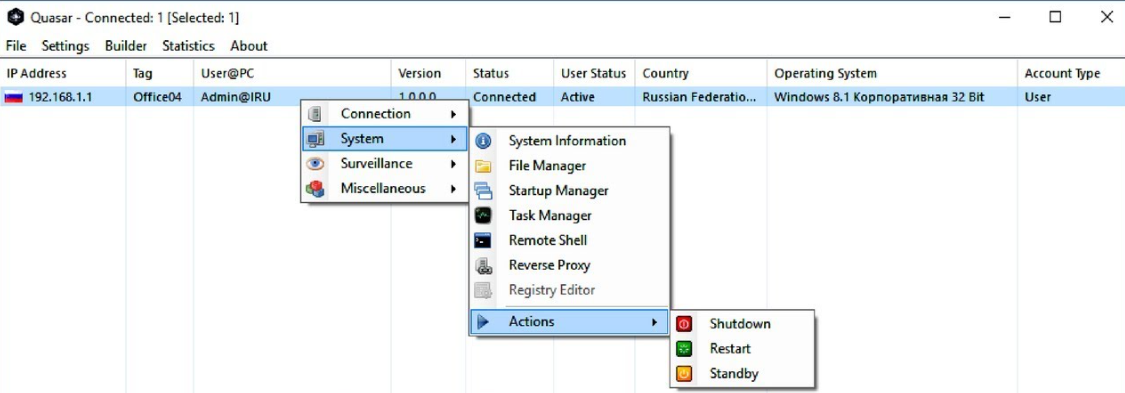
Quasar RAT v1.4.0 Cracked
In the realm of cyber threats, Remote Access Trojans (RATs) have become one of the most dangerous tools in a hacker’s arsenal, enabling complete control over compromised systems. Among these, a particularly notorious Quasar RAT v1.4.0 has gained widespread popularity in cybercriminal circles due to its powerful features and ease of customization. This malware has […]