Eagle Monitor RAT Reborn 2025
In 2025, the resurgence of advanced Remote Access Trojans (RATs) has introduced a new wave of sophisticated cyber threats, with modern variants demonstrating unprecedented stealth and functionality. These evolved surveillance tools have become weapons of choice for both cybercriminals and state-sponsored actors, enabling complete device takeover while evading traditional security measures. Eagle Monitor RAT Reborn […]
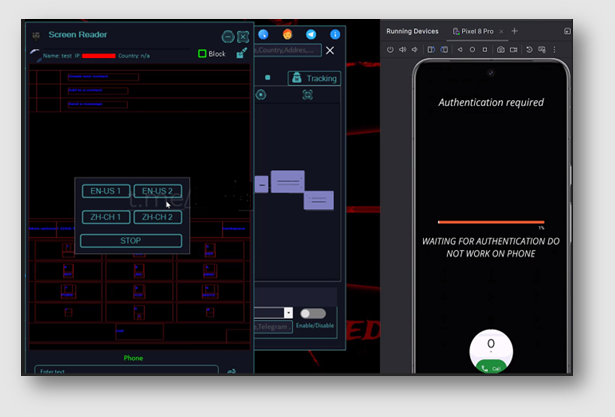
CERBERUS V4 Cracked
The Android banking malware landscape has become increasingly dangerous with the emergence of CERBERUS V4 Cracked, a sophisticated variant that demonstrates how cybercriminals are adapting commercial malware tools for widespread attacks. This advanced banking trojan has been actively used in campaigns targeting financial institutions and their customers worldwide, showcasing its ability to bypass modern security […]
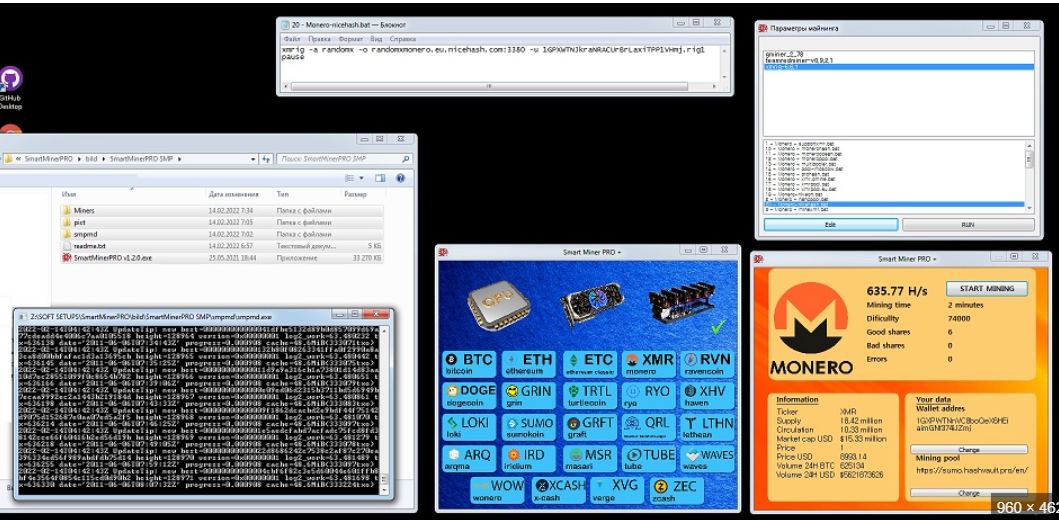
Silent Crypto Miner V 2.0.2
In the evolving landscape of cyber threats, cryptojacking has emerged as a lucrative and stealthy attack vector. One such tool, often referred to as Silent Crypto Miner V 2.0.2, exemplifies the growing sophistication of malicious mining software. Unlike traditional malware, which disrupts systems or steals data, this tool operates covertly, hijacking computing resources to mine […]
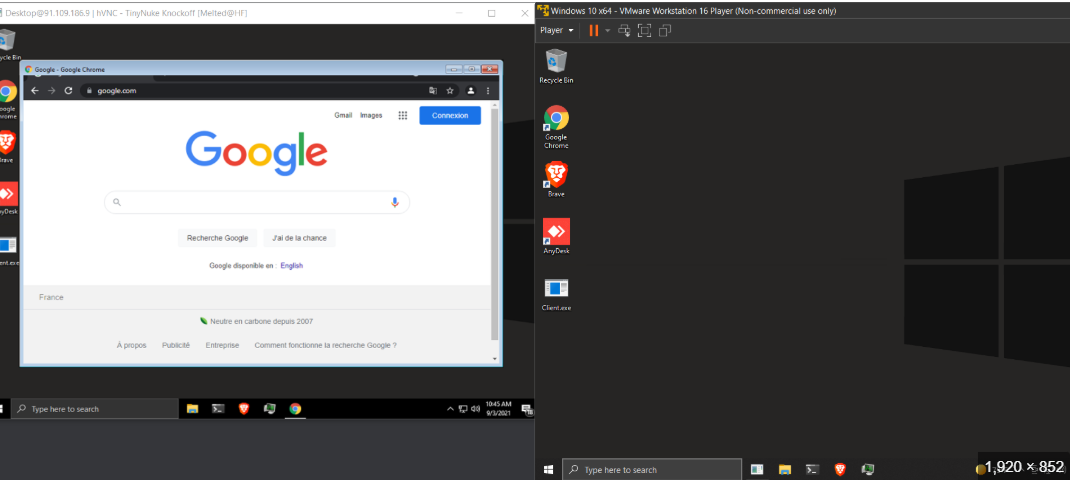
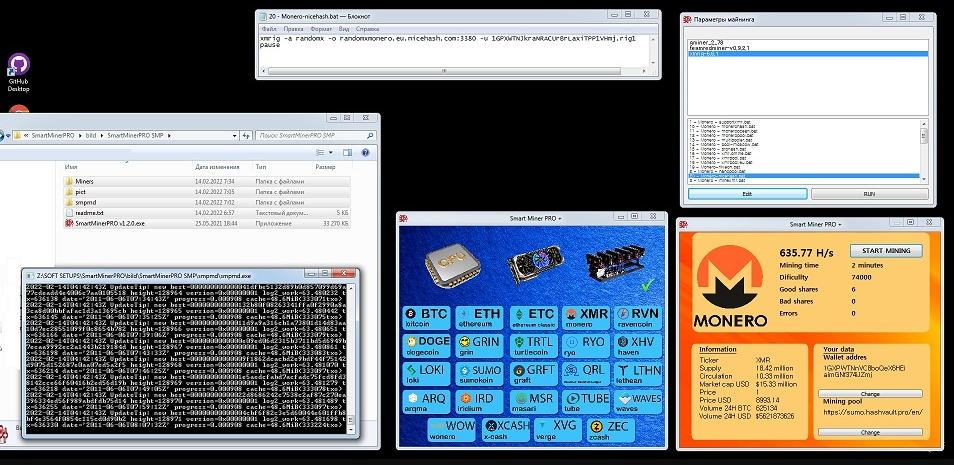
HVNC Tinynuke 2024
In the evolving landscape of cyber threats, remote access tools—both legitimate and malicious—play a significant role in modern attacks. One such tool, often referred to in cybersecurity circles, is the “HVNC Tinynuke 2024,” a sophisticated piece of malware designed to provide attackers with stealthy, persistent control over compromised systems. Unlike traditional Remote Access Trojans (RATS), […]
Alien Android Banking Botnet 2025 Cracked
The mobile banking threat landscape has reached alarming sophistication with Alien Android Banking Botnet 2025 Cracked, a powerful malware suite that combines banking trojan capabilities with botnet functionality. This advanced threat demonstrates how cybercriminals are weaponizing cracked versions of commercial malware to create large-scale attack networks. Alien Android Banking Botnet 2025 Cracked has been implicated […]
Miner CPUGPU Builder v1.0.1
In the evolving landscape of cyber threats, malicious tools designed to exploit system resources have become increasingly sophisticated. One such tool, a cryptojacking utility, leverages a combination of CPU and GPU processing power to mine cryptocurrencies without the victim’s knowledge. These tools are often deployed silently as part of larger malware campaigns, enabling attackers to […]
Freya Bitcoin Clipper Builder 2025
Cybercriminals are constantly refining their tools to exploit financial transactions, and one of the most insidious threats in this space is cryptocurrency stealers. These malicious programs target digital wallets by silently altering transaction details and redirecting funds to attackers. Often distributed through phishing campaigns or malware-laden downloads, these tools bypass user awareness by operating discreetly […]
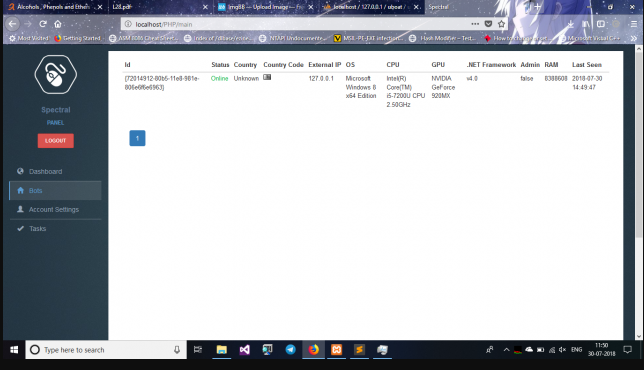
CosaNostra v1.2 HTTP Botnet Cracked with Tutorial
The cybercrime underground continues to evolve with increasingly sophisticated botnet tools, and CosaNostra v1.2 HTTP BotNet with Tutorial has emerged as a particularly dangerous threat in modern network attacks. This advanced botnet framework demonstrates how cybercriminals are making powerful attack tools more accessible through comprehensive tutorials and user-friendly interfaces. CosaNostra v1.2 HTTP BotNet with Tutorial […]
Golden Eye RAT 2025 Cracked
The cybersecurity landscape faces an escalating threat from sophisticated remote access trojans (RATs), with Golden Eye Rat 2025 Cracked emerging as a particularly dangerous tool in modern cyberattacks. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial surveillance tools to conduct espionage and data theft. Golden Eye Rat 2025 Cracked has […]
Doenerium Stealer 2024
Information stealers have become one of the most pervasive threats in the cybercrime landscape, enabling attackers to harvest sensitive data for financial gain or further exploitation. Among these, a particularly aggressive strain of credential-stealing malware has emerged, designed to target a wide range of data, including login credentials, cryptocurrency wallets, and browser-stored information. Often distributed […]