Teardroid v4
In the evolving landscape of cyber threats, remote access trojans (RATs) continue to be a persistent tool for attackers, allowing unauthorized control over compromised systems. Among these, Teardroid v4 has emerged as a notable Android-based malware, frequently employed in targeted attacks to steal sensitive data, monitor user activity, and deliver additional payloads. Its modular design and […]
Lost Door Aws 9.2
In the evolving landscape of cloud-based cyberattacks, sophisticated tools targeting AWS (Amazon Web Services) environments have become increasingly prevalent. Lost Door Aws 9.2 specialized utilities enable threat actors to exploit misconfigured cloud resources, escalate privileges, and establish persistent access to critical infrastructure. As organizations continue migrating operations to the cloud, attackers have adapted by developing […]
Subbus RAT 2025 Cracked
The cybersecurity landscape faces an escalating threat from next-generation remote access Trojans, with Subbus RAT 2025 emerging as a particularly sophisticated example of modern malware evolution. This advanced threat demonstrates how cybercriminals are leveraging cutting-edge techniques to create more resilient and feature-rich attack tools. SUBBUS RAT has been observed in high-profile attacks against financial institutions […]
PENTAGON RAT 2024
The “PENTAGON RAT 2024” is a highly advanced remote access trojan (RAT) that poses a major threat in modern cyberattacks. Unlike traditional malware, it not only evades detection but also maintains persistent access to compromised systems. Security experts have linked it to espionage, data theft, and credential harvesting. Itsmodular architecture allows attackers to deploy additional malicious payloads. As a result, it has become a versatile tool for both cybercriminals and state-sponsored […]
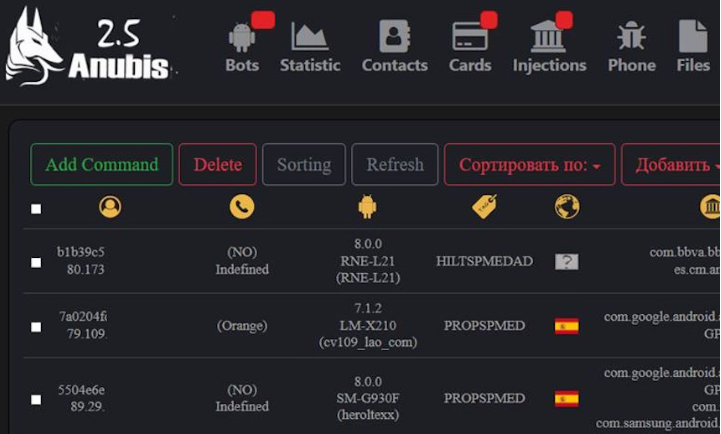
ANUBIS 7.0 ANDROID BOTNET (Panel + Builder+ Tutorial)
The rise of mobile-focused malware has introduced dangerous new threats to personal and enterprise security, with advanced botnet frameworks posing one of the most severe risks. Modern Android botnet kits now offer sophisticated infection vectors, evasion techniques, and monetization capabilities that rival traditional Windows malware. ANUBIS 7.0 ANDROID BOTNET toolkits typically include builder applications, command-and-control […]
Vulturi Stealer Cracked 2025
The underground cybercrime ecosystem continues to evolve with increasingly sophisticated data theft tools, and Vulturi Stealer has emerged as one of the most dangerous information stealers in recent years. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial malware to create powerful, low-cost attack tools. Vulturi Stealer Cracked 2025 has been actively […]
Crypto Ripper 2024
In 2024, cryptocurrency-focused malware has emerged as one of the most lucrative tools in the cybercriminal arsenal, with specialized stealers targeting both retail investors and institutional crypto platforms. Crypto Ripper 2024 sophisticated threats have evolved beyond simple wallet theft to encompass complex attacks against decentralized finance (DeFi) protocols, browser-based wallets, and even hardware wallet integrations. […]
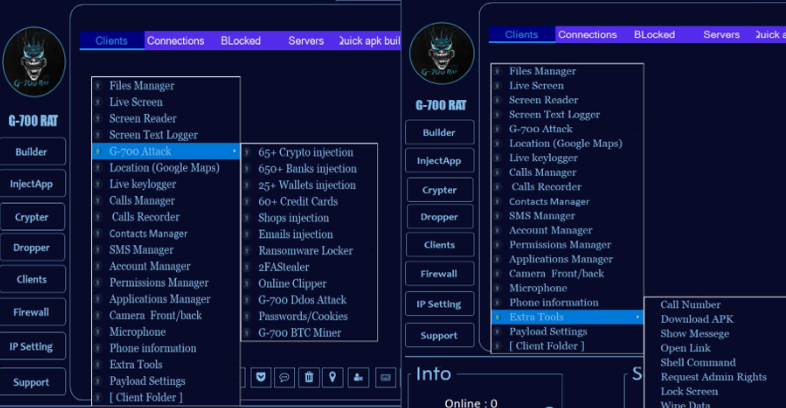
Scorpion Android Rat Cracked 2025
In 2025, cracked versions of advanced Android Remote Access Trojans (RATs) have become a growing threat in the mobile malware landscape, enabling attackers to bypass paywalls and distribute powerful spyware tools to a wider range of cybercriminals. Scorpion Android Rat Cracked 2025 illicitly modified RAT packages lower the barrier to entry for malicious actors, allowing […]
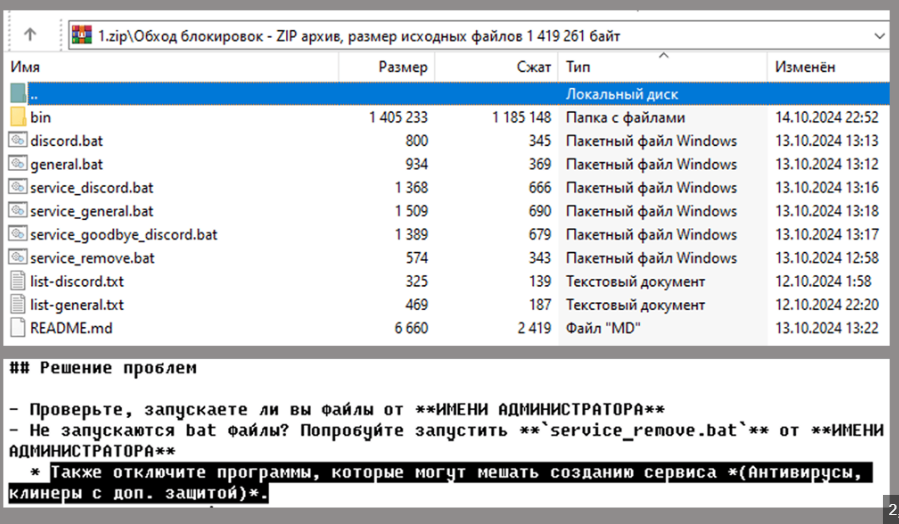
Silent Crypto Miner v2.1.0
Silent cryptocurrency miners have become a significant threat in modern cyberattacks, leveraging compromised systems to generate revenue for attackers without the victim’s knowledge or awareness. One such tool, Silent Crypto Miner v2.1.0, a widely known silent miner, exemplifies this trend by employing stealthy techniques to evade detection while maximising the theft of computational resources. These […]
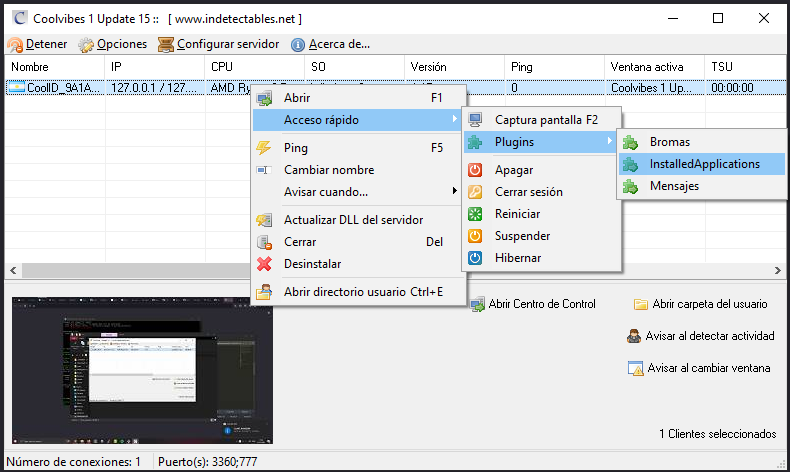
Coolvibes Rat 1.15
The evolution of Remote Access Trojans (RATs) has reached new levels of sophistication in 2024, with modern variants posing significant threats to both individual users and organizations. Coolvibes Rat 1.15 advanced malware tools have transitioned from simple backdoor access to comprehensive surveillance and control platforms, capable of bypassing even robust security measures. Particularly concerning is […]