Master Proxy Management with Python Proxy Finder 2026
Short Intro Python Proxy Finder 2026 stands out as a cutting-edge cybersecurity tool crafted in Python for efficient proxy detection and assessment. Its core purpose is to facilitate secure internet access and penetration testing by providing a steady stream of vetted proxies. The standout feature is its self-updating database that keeps pace with new proxy […]
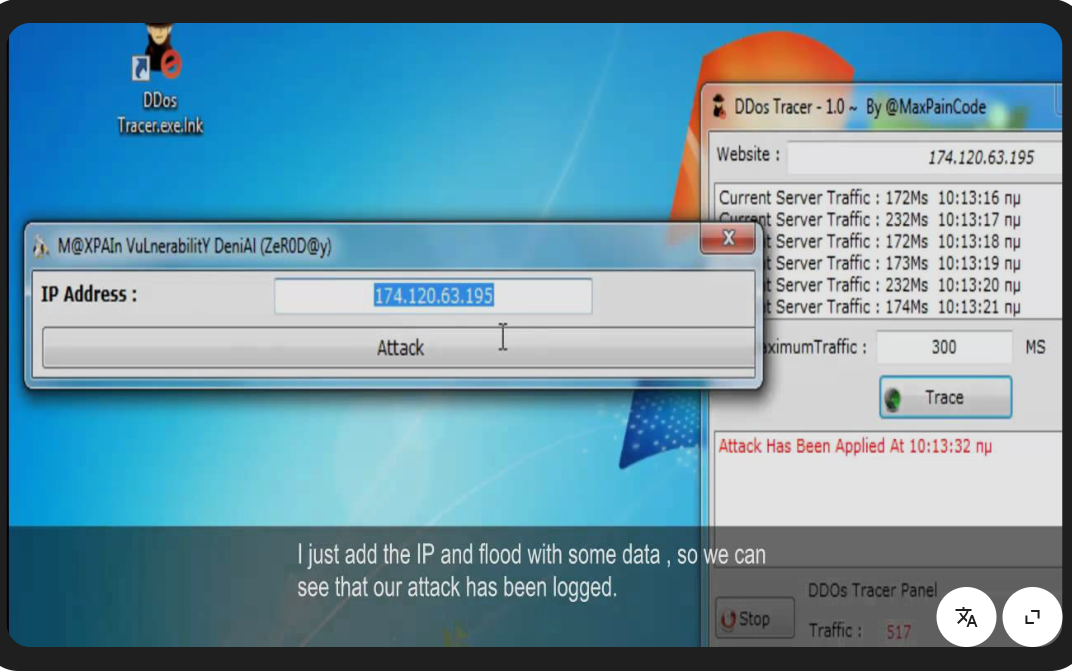
DDoS Attacks with DDoS Tracer 1.0 The Essential Cybersecurity Solution for 2026
Short Intro: Introducing DDoS Tracer 1.0, a robust cybersecurity instrument engineered to trace and neutralize DDoS attacks effectively. It serves to shield digital assets from volumetric floods and application-layer assaults. What sets it apart is its predictive analytics, forecasting threats before they strike for proactive defense. Feature Explanations: Instant Alert System: Delivers immediate notifications on […]
Elevate Cybersecurity Testing with HashKracker 2025
Short Intro: Introducing HashKracker 2025, an innovative cybersecurity solution that empowers security experts to decrypt hashed passwords swiftly and accurately. Its core purpose is to facilitate thorough vulnerability assessments, helping organizations fortify defenses against unauthorized access. What sets it apart is its user-friendly interface combined with unparalleled speed, positioning it as a must-have for cybersecurity […]
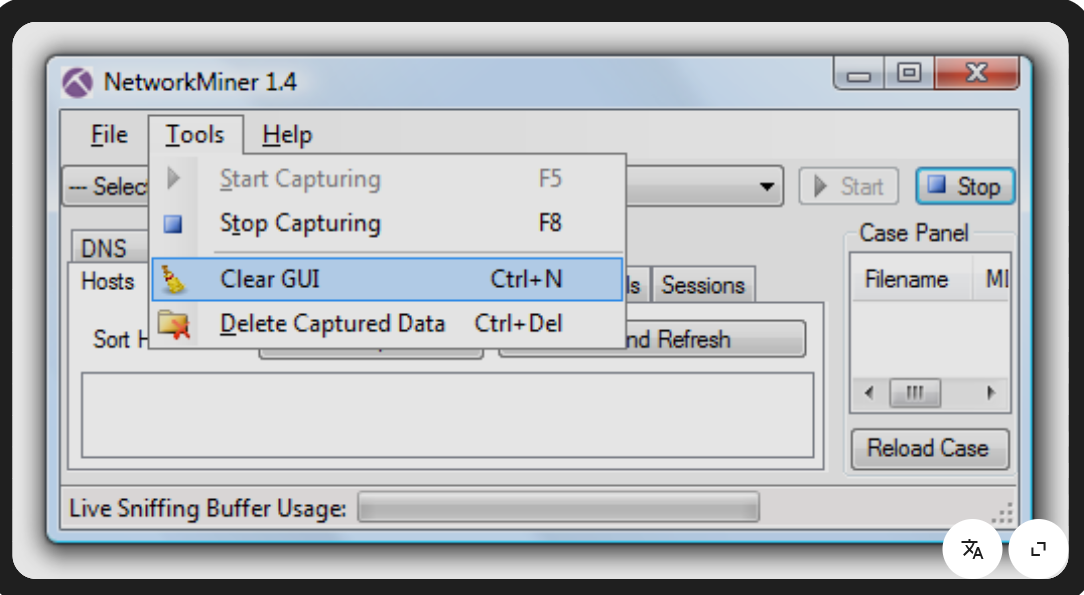
Explore NetworkMiner 1.4.1 Cutting-Edge Packet Analyzer for Network Security in 2026
Short Intro: NetworkMiner 1.4.1 stands out as a comprehensive network forensics solution that sniffs, decodes, and analyzes network packets with precision. It serves to empower IT teams in uncovering hidden threats, reconstructing data flows, and enhancing overall security posture. What sets it apart is its user-friendly interface that simplifies complex forensic tasks for both novices […]
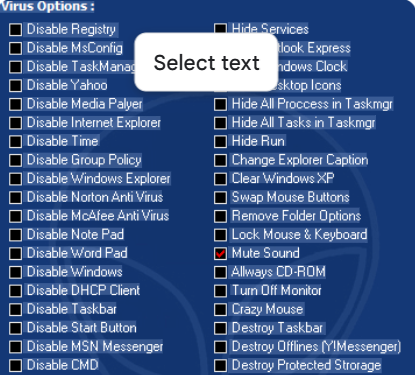
Powerful Virus Simulations Using JPS Virus Maker 2026 for Cyber Experts
Short Intro: empowers cybersecurity experts to craft and deploy simulated viruses for rigorous testing protocols. It serves the critical purpose of identifying weaknesses in systems before actual attacks occur. Its standout USP lies in automated obfuscation techniques that make the created viruses indistinguishable from real ones. Feature Explanations: Modular Virus Building: Assemble viruses using pre-built […]
Leading Browser Password Decryptor 2026 Tool for Cyber Defense
Short Intro: Introducing the Browser Password Decryptor 2026, an essential cybersecurity utility that retrieves encrypted passwords from web browsers for particular security evaluations. It serves the critical role of identifying weak spots in password storage to bolster online protection. What sets it apart is its unparalleled accuracy, delivering 99% success rates in decryption tasks. Feature […]
Anonymous Attacker Package 2026 for Secure Hacking Simulations
Short Intro: Introducing the Anonymous Attacker Package 2026, a specialized cybersecurity tool tailored for red team exercises and security audits. It empowers users to launch simulated attacks anonymously, pinpointing weak spots in digital infrastructures with precision. What sets it apart is its zero-log policy, guaranteeing that all activities remain completely untraceable during authorized use. Feature […]
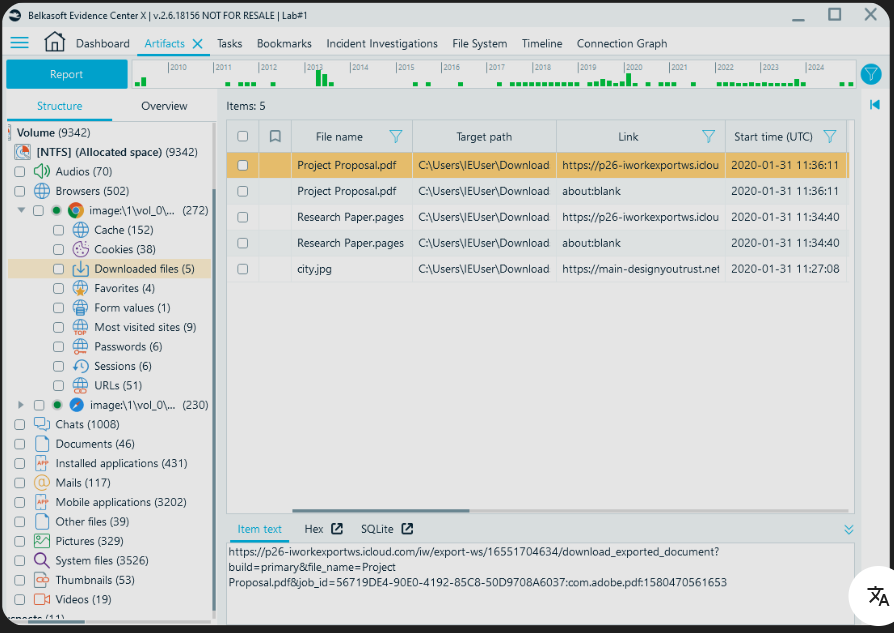
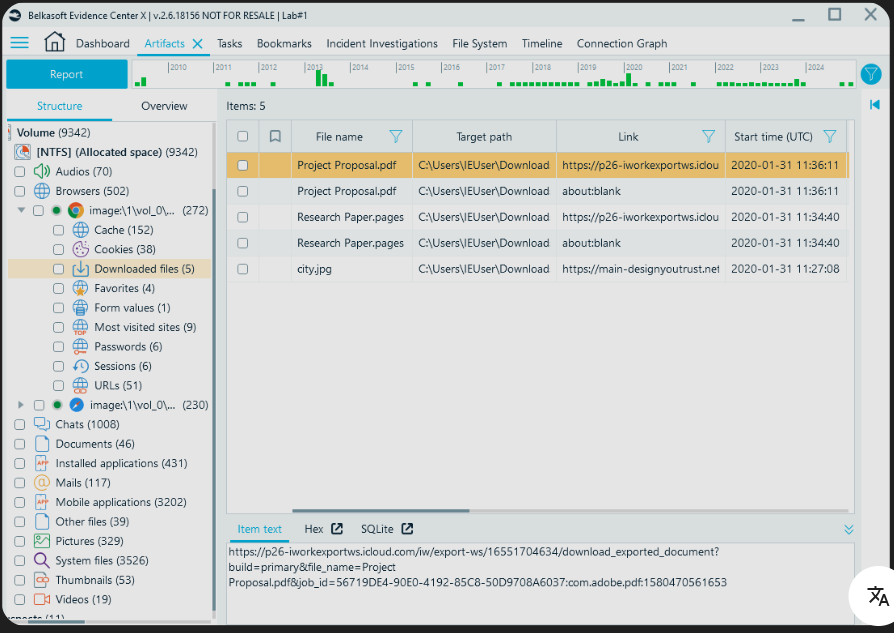
Browser Forensic Tool 2026 Revolutionize Digital Evidence Gathering
Short Intro: Introducing Browser Forensic Tool 2026, a specialized cybersecurity tool engineered for experts in digital forensics to delve deep into browser data. It serves to uncover latent evidence from online activities, streamlining investigations in high-stakes environments. Its standout USP is real-time scanning capabilities, setting new benchmarks for efficiency in 2026. Feature Explanations: Real-Time Scanning: […]
Secure Your Digital Assets with Multi Locker 3 Full Version
Short Intro: Multi Locker 3 is a cutting-edge cybersecurity tool designed to protect sensitive data through robust file locking mechanisms. Its primary purpose is to safeguard files from unauthorized access in an era of rising cyber threats in 2026. The key USP lies in its multi-layered encryption that ensures top-tier security without compromising user convenience. […]
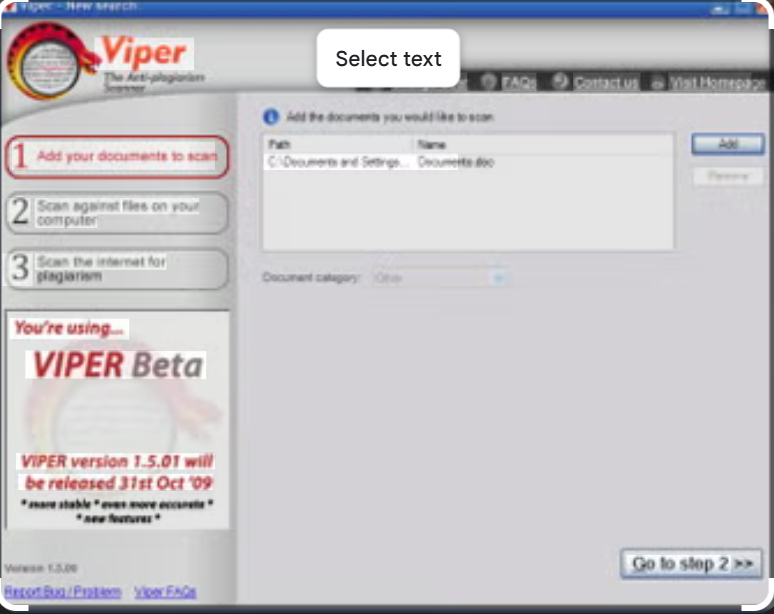
Free Download Cybersecurity with Viper Crypter 2026
Short Intro: Viper Crypter 2026 stands out as a premier cybersecurity tool focused on file encryption and obfuscation to shield digital assets from hackers. It serves developers, IT professionals, and organizations by transforming code and files into undetectable forms. What sets it apart is its AI-driven adaptive algorithms that evolve encryption patterns in real-time, staying […]