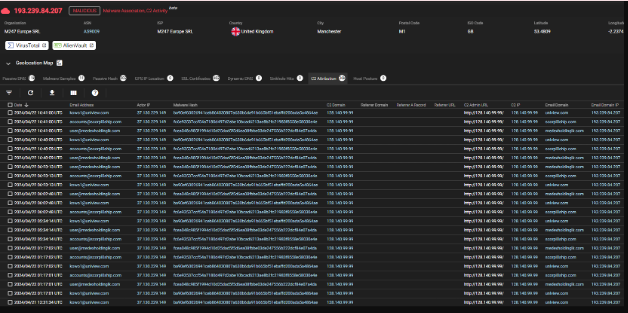
Gold Alduin Botnet 2025
Gold Alduin Botnet 2025 remain one of the most potent threats in cybersecurity, enabling large-scale attacks through networks of compromised devices. One such example is a sophisticated modular botnet frequently used in credential theft, cryptocurrency mining, and distributed denial-of-service (DDoS) attacks. Its ability to evade detection while maintaining persistent control over infected machines makes it […]
Dangerous Rat-v5 Cracked
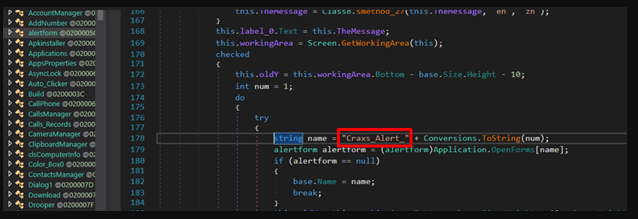
Remote Access Trojans (RATs) are among the most dangerous tools in a cybercriminal’s arsenal, enabling stealthy, long-term control over compromised systems. Unlike traditional malware that may simply corrupt files or display ransomware messages, Dangerous Rat-v5 allow attackers to operate undetected, performing espionage, data theft, and even lateral movement across networks. They are frequently used in […]
Proton Crypter V 2.0
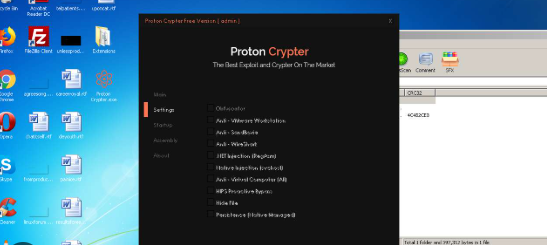
In the evolving landscape of cybersecurity threats, Proton Crypter V 2.0 has emerged as a critical tool for attackers who aim to evade detection and deploy malicious payloads. These programs are specifically designed to obfuscate and encrypt harmful code, thereby making it extremely difficult for traditional antivirus solutions to identify and block them. Consequently, modern […]
Visual Protector 0.5
In modern cyberattacks, tools like Visual Protector 0.5 play a significant role in bypassing security measures and delivering malicious payloads. These tools are often used by threat actors to evade detection, making them a persistent challenge for cybersecurity professionals. By leveraging obfuscation, encryption, and other evasion techniques, such tools enable malware to infiltrate systems undetected, […]
SQLi Dork Scanner with Dork list 2025
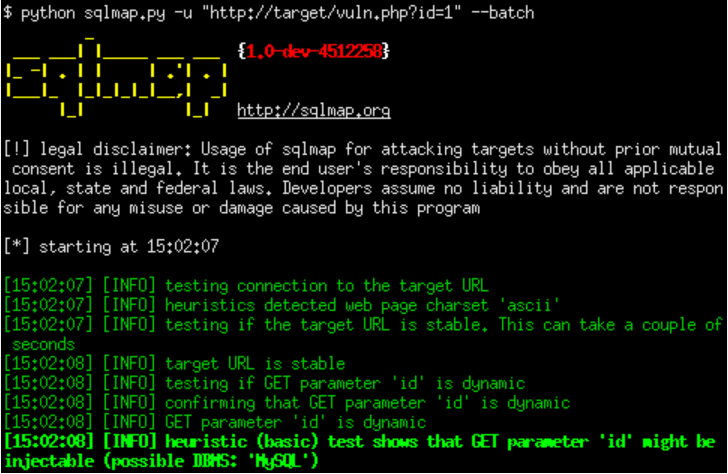
In modern cyberattacks, SQLi Dork Scanner) remains one of the most prevalent and dangerous vulnerabilities, allowing attackers to manipulate databases and extract sensitive information. Attackers often use specialized tools to automate the discovery of vulnerable websites. One such method involves leveraging search engine dorks—carefully crafted search queries that identify websites with potential security flaws. The […]
Agent tesla builder-3-2-5-5 cracked
In the ever-evolving world of cyber threats, agent-tesla-builder has become a significant concern for security professionals. These tools allow attackers to create customized malware strains with minimal effort, enabling widespread espionage, data theft, and system compromise. One such example is a well-known Remote Access Trojan (RAT) builder, frequently distributed on underground forums and used in […]
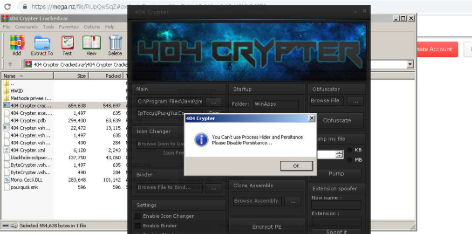
404 Crypter Cracked
In the evolving landscape of cyber threats, 404 Crypter Cracked have become indispensable tools for malicious actors seeking to evade detection. Cracked versions of these programs circulate in underground forums, democratizing access to advanced obfuscation techniques. These tools empower attackers to bypass traditional security measures, facilitating the distribution of ransomware, data stealers, and other malware. […]
Azorult Stealer v3.4 Cracked
In the ever-evolving landscape of cybercrime, information-stealing malware has become one of the most pervasive threats to both individuals and organizations. Among these threats, a particularly dangerous strain has emerged as a favorite among cybercriminals due to its versatility and effectiveness. This Azorult Stealer v3.4 Cracked, often distributed through phishing campaigns and exploit kits, specializes […]
Codelux Crypter v3.0 Cracked
Codelux Crypter v3.0 Cracked have become a critical tool for cybercriminals, enabling them to bypass security measures and deploy malware undetected. Cracked versions of such tools, often leaked or illegally distributed, lower the technical barrier for attackers, allowing even those with minimal expertise to launch sophisticated attacks. These crypters are commonly used in ransomware campaigns, […]
SQLi-DB-SQL Injection Dork Scanner v1.0
SQLi-DB-SQL Injection remains one of the most critical vulnerabilities in web applications, allowing attackers to manipulate databases and extract sensitive information. Automated tools designed to exploit these vulnerabilities play a significant role in both offensive security testing and malicious cyberattacks. Among these tools, SQLi dork scanners are widely used to identify vulnerable websites by leveraging […]