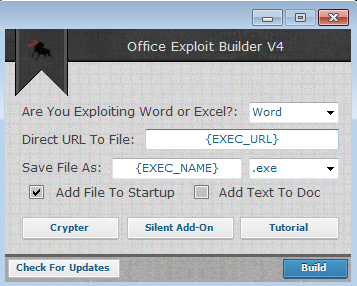
Office Exploit Builder Cracked 2025
Office Exploit Builder delivery has seen a resurgence in modern cyberattacks, with threat actors increasingly leveraging weaponized Office documents as their initial infection vector. The availability of sophisticated exploit builders has significantly simplified the process of creating malicious documents that can bypass security controls. Cracked versions of these tools circulating in underground forums have lowered […]
NJRAT Red Version Error 404
In the ever-evolving world of cyber threats, Remote Access Trojans (RATs) remain a persistent and dangerous tool for attackers. Among these, a well-known NJRAT Red Version —often referred to by its alias—has gained notoriety for its flexibility and widespread use in cyberattacks. This malware enables attackers to take full control of infected systems, steal sensitive […]
BIG EXPLOIT COLLECTION 2025
In the ever-evolving landscape of cyber threats, BIG EXPLOIT COLLECTION 2025 frameworks have become a favored weapon for both sophisticated threat actors and script kiddies alike. These Swiss Army knife-like toolkits dramatically lower the barrier to entry for cybercriminals by packaging hundreds of weaponized vulnerabilities with automated exploitation capabilities. The 2025 generation of these frameworks […]
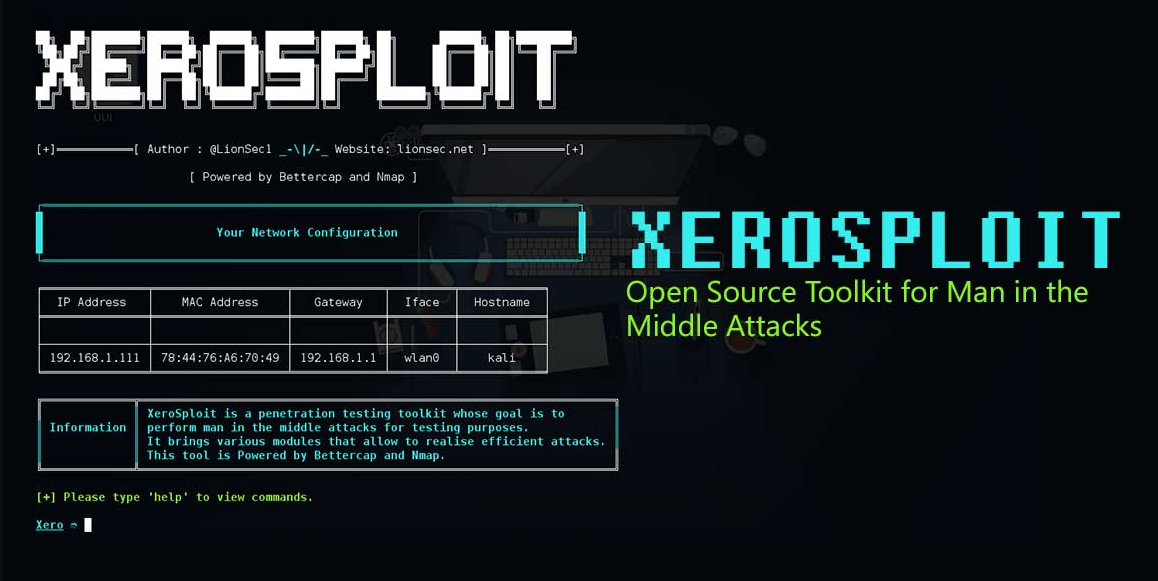
Xerosploit Toolkit 2025
Modern cyberattacks increasingly leverage sophisticated network penetration toolkits that automate man-in-the-middle (MITM) attacks and network exploitation. These frameworks have become particularly dangerous as they enable attackers to intercept, manipulate, and exploit network traffic with minimal technical expertise. When weaponised by malicious actors, Xerosploit Toolkit 2025 can facilitate credential theft, session hijacking, and malware distribution, while […]
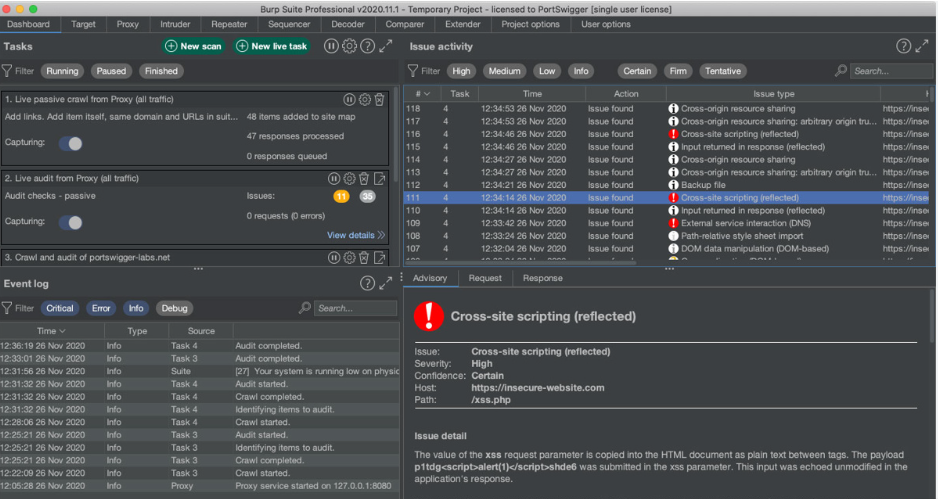
Burp Suite Professional 2022.2.2 Activated
In modern cybersecurity, tools designed for penetration testing and vulnerability assessment are often repurposed by malicious actors to exploit weaknesses in networks and applications. One such tool, Burp Suite Professional 2022.2.2, activated, has become a double-edged sword. While security professionals widely use it to identify and fix vulnerabilities, attackers leverage its capabilities to map attack […]
Trillium Security MultiSploit Tool v6.5.21 Full
The cybersecurity landscape faces growing threats from sophisticated attack frameworks that bundle multiple exploitation capabilities into a single platform. These advanced Trillium Security MultiSploit lower the barrier to entry for cybercriminals by packaging professional-grade attack vectors with user-friendly interfaces. Particularly dangerous is their ability to automate complex attack chains combining reconnaissance, vulnerability exploitation, and post-compromise […]
Crypto Money Grabber 2025
In the evolving landscape of cybercrime, Crypto Money Grabber 2025 tools designed to steal cryptocurrency have become a significant threat. Among these, specialized malware known as “crypto money grabbers” has emerged as a preferred weapon for attackers targeting digital wallets and exchanges. These tools exploit vulnerabilities in both individual users and systems to siphon funds, […]
SQLi Toolkit 2025
In today’s rapidly evolving cybersecurity landscape, automated exploitation tools have become a significant concern for defenders. Among these, SQLi Toolkit 2025 has emerged as a hazardous tool due to its ability to efficiently identify and exploit SQL injection (SQLi) vulnerabilities. SQLi remains one of the most prevalent attack vectors, enabling attackers to bypass authentication, steal […]
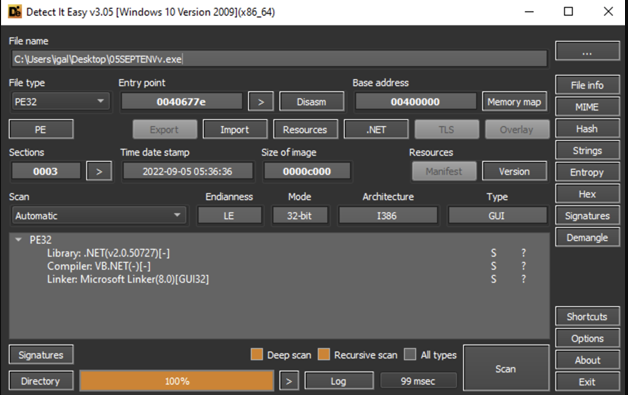
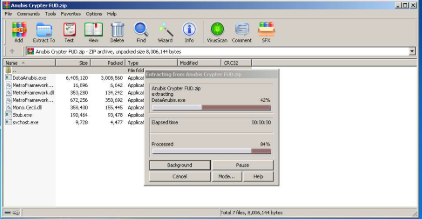
Anubis Crypter FUD 2025
In the arms race between cybercriminals and security professionals, Anubis Crypter FUD 2025 have emerged as a critical weapon for evading detection. The latest iterations of these tools employ increasingly sophisticated methods to bypass even advanced security solutions, enabling malware to operate undetected for extended periods. These evasion capabilities make crypters particularly dangerous in ransomware […]
Echelon Stealer-v5
Information stealers have become one of the most pervasive threats in today’s cyber landscape, with sophisticated variants like this Echelon Stealer-v5 playing a significant role in credential theft and financial fraud. Unlike ransomware that announces its presence, these stealthy threats operate silently, harvesting sensitive data that fuels further criminal activity. This particular stealer has gained […]