Smtp Checker 2025
Email remains one of the most critical communication channels for both individuals and organizations, making email infrastructure a prime target for cybercriminals. In 2025, specialized tools designed to test and exploit Smtp Checker 2025 (Simple Mail Transfer Protocol) servers have become increasingly sophisticated, playing a pivotal role in modern cyberattacks. These tools enable threat actors to identify vulnerable email servers, verify legitimate email addresses, and ultimately launch large-scale spam campaigns, phishing attacks, and credential-stuffing operations. By systematically probing SMTP servers, attackers can gather valuable intelligence about an organization’s email infrastructure, paving the way for more targeted and effective attacks. The widespread availability of these tools on underground forums has lowered the barrier to entry, allowing even less technically skilled attackers to conduct sophisticated email-based attacks.
Download Link 1
Download Link 2
Download Link 3
Download Link 4
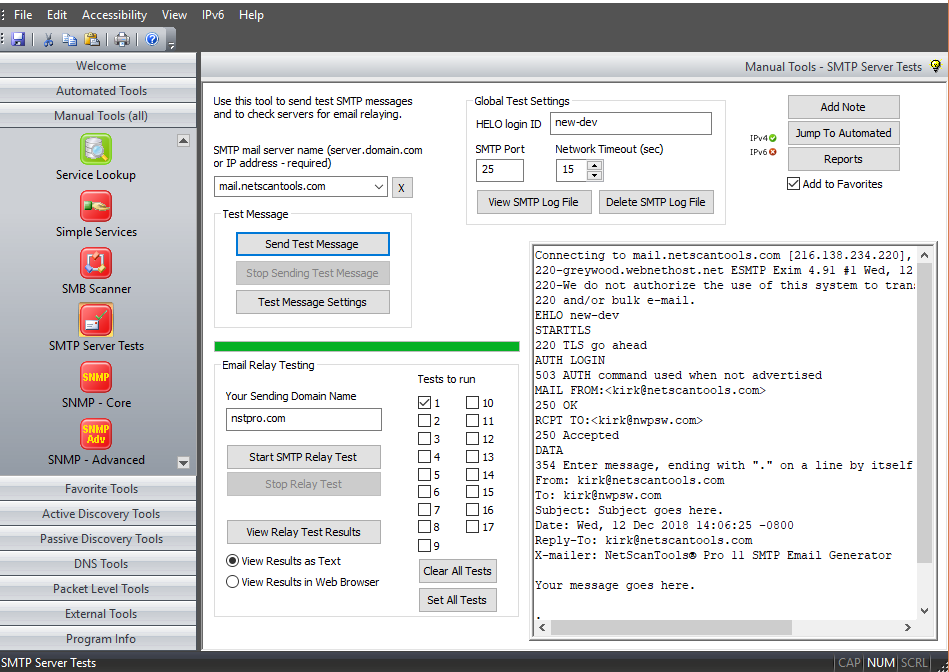
This software is a specialized SMTP validation tool designed to test and analyze email servers for vulnerabilities and verify the existence of email addresses. It automates the process of connecting to SMTP servers and executing various commands to determine server configurations, identify security weaknesses, and validate email addresses. While legitimate security professionals might use similar tools for penetration testing and vulnerability assessments, malicious actors typically deploy this software to build targeted email lists for spam campaigns, phishing attacks, or brute-force attempts. The tool’s effectiveness lies in its ability to bypass common security measures and accurately distinguish between valid and invalid email addresses, making it a valuable asset for email-based attacks.
Key Features
| Feature | Description |
| SMTP Server Scanning | Identifies open SMTP servers and tests their configurations |
| Email Address Validation | Verifies the existence of email addresses through SMTP protocols |
| Bulk Processing | Handles large lists of email addresses or domains for mass validation |
| Proxy Support | Routes connections through proxies to avoid IP blocking |
| Security Bypass | Implements techniques to circumvent rate limiting and other protections |
| Detailed Reporting | Generates comprehensive logs of valid emails and server vulnerabilities |
| Custom Scripting | Allows users to create custom attack scripts for specific scenarios |
| Integration Capabilities | Works with other tools to feed validated emails into spam or phishing campaigns |
How Smtp Checker 2025 Works
The software operates through a series of carefully orchestrated steps designed to maximize efficiency while minimizing detection:
1. Target Acquisition and Input
- Accepts input in various formats (individual emails, domain lists, or IP ranges)
- Parses and normalizes data to ensure compatibility with SMTP standards
- Optional enrichment with common username patterns
2. SMTP Server Discovery
- For domain-based inputs, performs MX (Mail Exchange) record lookups to identify SMTP servers
- For IP-based inputs, scans specified ranges for open SMTP ports (typically port 25, 465, or 587)
- Tests server responsiveness and compatibility with various SMTP commands
3. Email Validation Process
- Initiates SMTP conversations using standard protocols (EHLO/HELO, MAIL FROM, RCPT TO)
- Analyzes server responses to determine email validity:
- Acceptance: Indicates a valid email address
- Rejection: Suggests the address does not exist
- Ambiguous responses: May require additional probing or alternative techniques
- Handles various SMTP implementations and error conditions gracefully
4. Advanced Validation Techniques
- EXPN and VRFY Exploitation: Attempts to use SMTP commands (if available) to expand mailing lists or verify users
- Greylisting Bypass: Implements retry mechanisms to overcome temporary rejections
- Tarpit Evasion: Detects and avoids slow-responding servers designed to stall attacks
5. Evasion and Anti-Detection
- Rotates IP addresses using proxy lists or VPNs to avoid blacklisting
- Randomizes request timing to mimic legitimate traffic patterns
- Spoofs HELO/EHLO identifiers to appear as legitimate mail servers
- Adapts to server-specific quirks and limitations to maintain access
6. Post-Validation Processing
- Categorizes results by:
- Valid vs. invalid addresses
- Server configurations and vulnerabilities
- Domain-specific patterns
- Formats output for various malicious use cases:
- Targeted phishing campaigns
- Credential-stuffing attacks
- Spam distribution lists
- Optionally feeds validated addresses into other attack tools


