cybersecurity tools
Dangerous RAT v5 Cracked 2026
Dangerous RAT v5 Cracked is a powerful remote access trojan designed for cybersecurity professionals to simulate threats and enhance network defenses. This cracked version provides unrestricted access to advanced monitoring capabilities, enabling ethical hackers to identify vulnerabilities in real-time. Its unique selling point lies in its seamless integration with penetration testing workflows, offering unparalleled control […]
Hackus Mail Checker 2.3 – HMC
Hackus Mail Checker 2.3 is a powerful cybersecurity tool designed to verify email authenticity and detect threats in real-time. Its primary purpose is to protect users and organizations from phishing, spam, and fraudulent communications, ensuring safer digital interactions. The key USP lies in its advanced AI-driven algorithms that provide instant, accurate results with minimal false […]
SMS Nuker 2026 New Version
SMS Nuker 2026 is a powerful cybersecurity tool designed for ethical hackers and penetration testers to simulate SMS flooding attacks on target systems. Its primary purpose is to test the resilience of networks and devices against overwhelming SMS traffic, helping identify vulnerabilities in mobile communication protocols. The key USP lies in its user-friendly interface and […]
Exploit Pack 2026 New Version
Hacking Scripts 2026 is a cutting-edge cybersecurity tool designed for penetration testers and ethical hackers to simulate real-world attacks and fortify defenses. It empowers professionals to identify vulnerabilities in networks, applications, and systems through automated scripting. Its unique selling point is the seamless integration of AI-driven script generation, making complex exploits accessible and efficient for […]
Red Proxy Checker 2026
Red Proxy Checker 2026 is a robust cybersecurity utility focused on thorough proxy server assessment to safeguard digital activities. Its core purpose is to empower users with insights into proxy effectiveness, reducing risks from insecure connections. The standout USP lies in its cloud-based architecture, enabling scalable checks without local resource demands. Download Link 1 Download […]
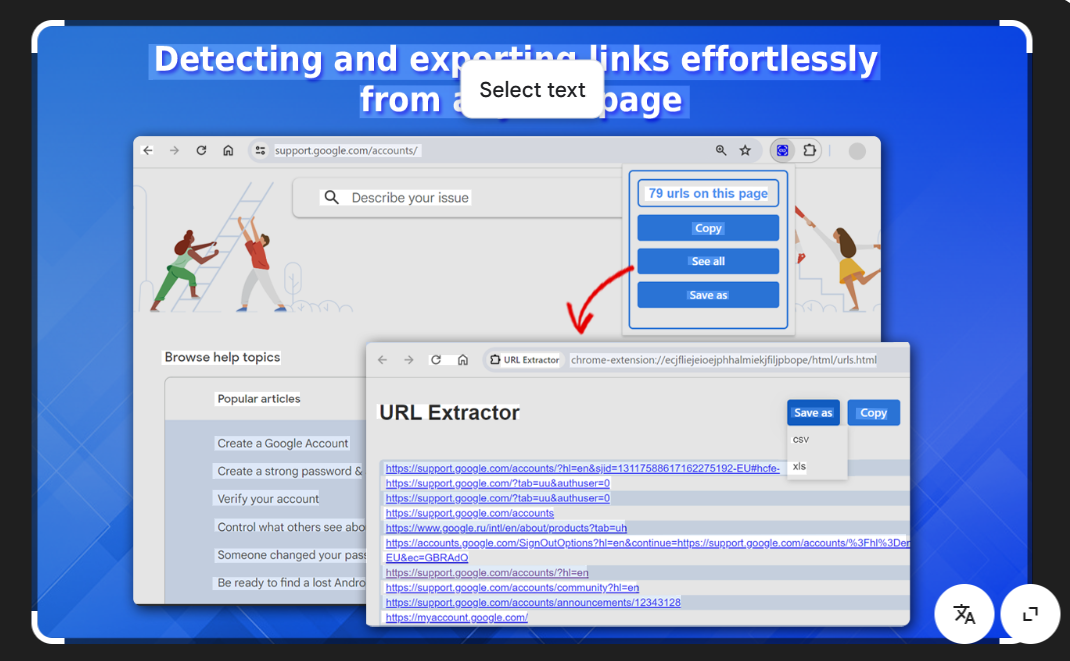
Google’s Hidden URLs with the Ultimate Cybersecurity Extraction Tool
Short Intro: Google URL Extractor 2026 is a powerful cybersecurity tool designed to scrape and extract URLs directly from Google search results for in-depth analysis. It helps security professionals and researchers identify potential threats, track malicious links, and enhance web security audits with high precision. Its unique selling point lies in its advanced AI-driven filtering, […]
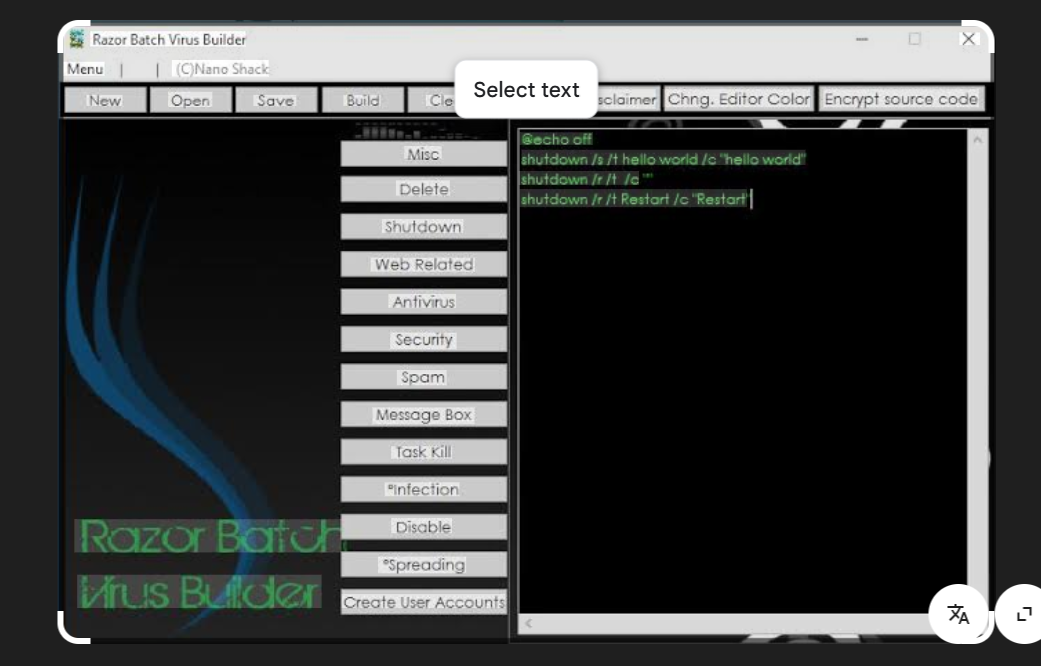
Razor Batch Virus Builder 2026 Advanced Cybersecurity Testing Tool
Short Intro: The Razor Batch Virus Builder 2026 is a cutting-edge cybersecurity tool designed for professionals to simulate and analyze malware threats in controlled environments. Its primary purpose is to enhance cybersecurity defenses by enabling ethical hackers and researchers to build, test, and dissect viruses without real-world risks. A key USP is its user-friendly batch […]
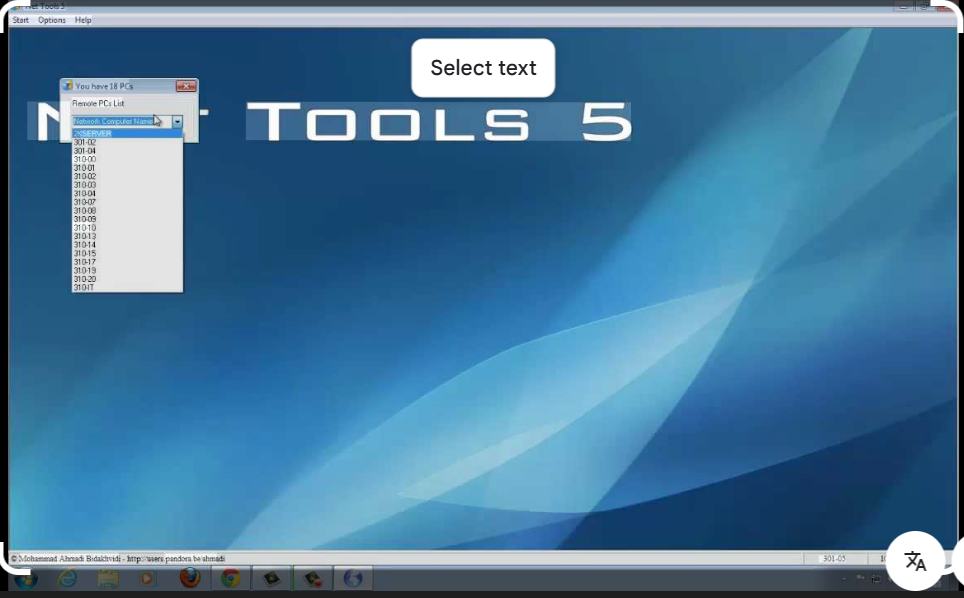
Net Tools 5.0.70 Advanced Network Suite 2026
Short Intro: Net Tools 5.0.70 is a comprehensive pro hacking toolkit designed for cybersecurity experts and ethical hackers. It empowers users to analyze networks, detect vulnerabilities, and enhance security protocols with unparalleled precision. Its standout USP is the seamless integration of automated scanning and real-time reporting, making it indispensable for modern penetration testing. Download Link […]
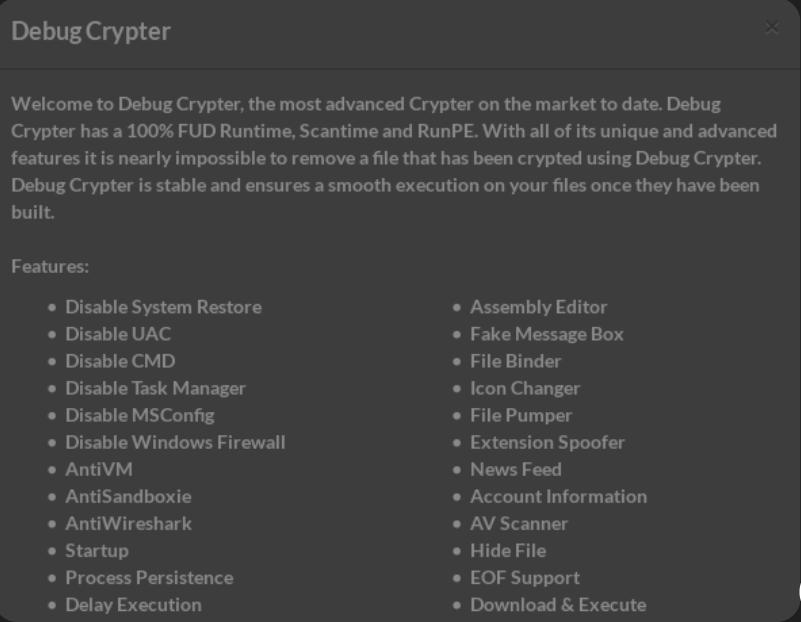
File Crypter 2026 The Leading Cybersecurity Solution for File Encryption
Short Intro: Introducing File Crypter 2026, a cutting-edge cybersecurity tool engineered to encrypt files and shield valuable information from cyber threats. It serves to bolster data integrity by converting plain files into secure, encrypted formats that only authorized users can access. Its standout USP is the integration of AI-driven algorithms that adapt to emerging threats, […]
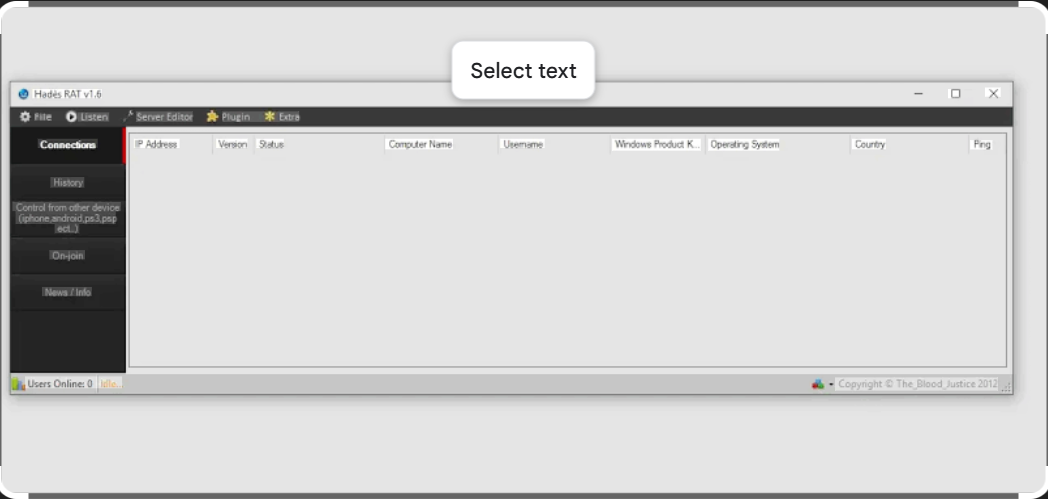
Powerful Remote Access Control with Hades RAT v1.6
Short Intro: is a cutting-edge remote access tool designed for advanced cybersecurity professionals and penetration testers. Its primary purpose is to enable secure, real-time monitoring and control of systems, making it indispensable for ethical hacking and vulnerability assessments. The key USP lies in its stealthy architecture, which evades detection while providing unparalleled efficiency in threat […]