Bruter
Here are all types of bruter like Password Bruters, Hash Bruters, Wi-Fi Bruters, API/Token Bruters, ZIP/RAR Bruters, Credential Stuffing Tools.
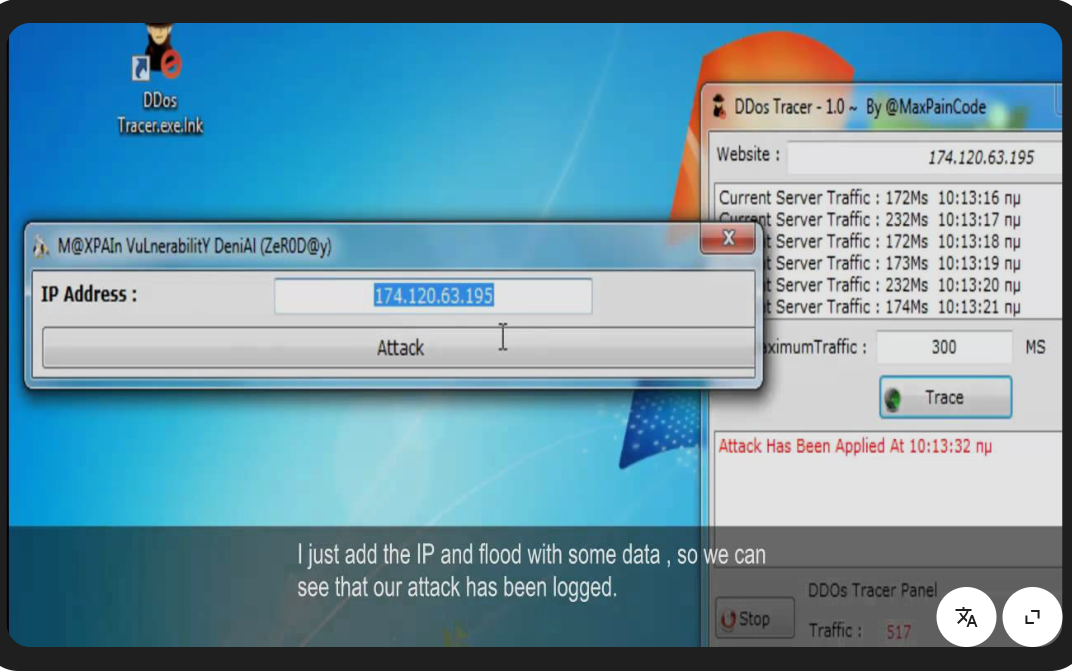
DDoS Attacks with DDoS Tracer 1.0 The Essential Cybersecurity Solution for 2026
Short Intro: Introducing DDoS Tracer 1.0, a robust cybersecurity instrument engineered to trace and neutralize DDoS attacks effectively. It serves to shield digital assets from volumetric floods and application-layer assaults. What sets it apart is its predictive analytics, forecasting threats before they strike for proactive defense. Feature Explanations: Instant Alert System: Delivers immediate notifications on […]
Elevate Cybersecurity Testing with HashKracker 2025
Short Intro: Introducing HashKracker 2025, an innovative cybersecurity solution that empowers security experts to decrypt hashed passwords swiftly and accurately. Its core purpose is to facilitate thorough vulnerability assessments, helping organizations fortify defenses against unauthorized access. What sets it apart is its user-friendly interface combined with unparalleled speed, positioning it as a must-have for cybersecurity […]
Leading Browser Password Decryptor 2026 Tool for Cyber Defense
Short Intro: Introducing the Browser Password Decryptor 2026, an essential cybersecurity utility that retrieves encrypted passwords from web browsers for particular security evaluations. It serves the critical role of identifying weak spots in password storage to bolster online protection. What sets it apart is its unparalleled accuracy, delivering 99% success rates in decryption tasks. Feature […]
Free Download Cybersecurity with Viper Crypter 2026
Short Intro: Viper Crypter 2026 stands out as a premier cybersecurity tool focused on file encryption and obfuscation to shield digital assets from hackers. It serves developers, IT professionals, and organizations by transforming code and files into undetectable forms. What sets it apart is its AI-driven adaptive algorithms that evolve encryption patterns in real-time, staying […]
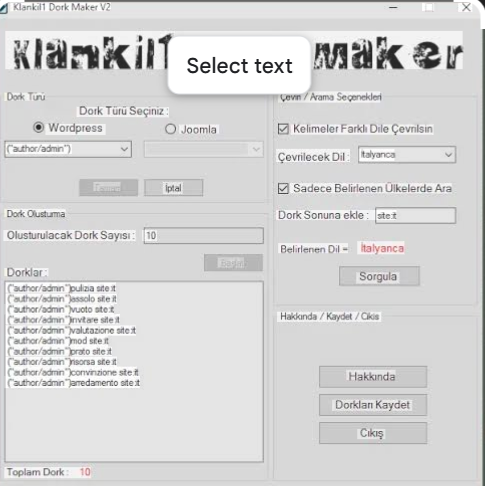
Master Google Dorks with Klankil1 Dork Maker v2
Short Intro: Klankil1 Dork Maker v2 stands as an innovative cybersecurity tool crafted to automate the creation of effective Google dorks for uncovering hidden web vulnerabilities. Its core purpose is to streamline reconnaissance tasks for security experts, enabling faster threat identification. What sets it apart is its proprietary engine that adapts dorks dynamically, achieving 50% […]
Elevate Your Cybersecurity Arsenal: Introducing Dedi Exploiter v2
Short Intro: Dedi Exploiter v2 stands out as a powerful cybersecurity solution tailored for professionals aiming to assess and fortify dedicated servers against potential threats. Built for ethical hacking, it empowers users to conduct in-depth penetration testing with minimal risk. Its standout USP is the zero-day detection capability, which identifies unheard-of vulnerabilities in dedicated infrastructures, […]
WordPress Bruter 2026 Advanced Brute Force Cybersecurity Solution for Experts
Short Intro: Introducing WordPress Bruter 2026, an essential cybersecurity tool tailored for professionals conducting brute force testing on WordPress platforms. It serves to uncover weak passwords and authentication flaws, enabling proactive security measures. The standout USP is its adaptive algorithms that learn from failed attempts, enhancing success rates in dynamic environments. Feature Explanations: Adaptive Brute […]
Enhance Joomla Defenses Using Joomla Bruner 2026 Brute-Force Solution
Short Intro: Joomla Bruner 2026 stands out as a specialized cybersecurity utility aimed at professionals conducting brute-force testing on Joomla content management systems. It serves to evaluate and strengthen website security by simulating exhaustive login trials. What sets it apart is its intelligent algorithm that optimizes attack efficiency while maintaining a focus on ethical usage. […]
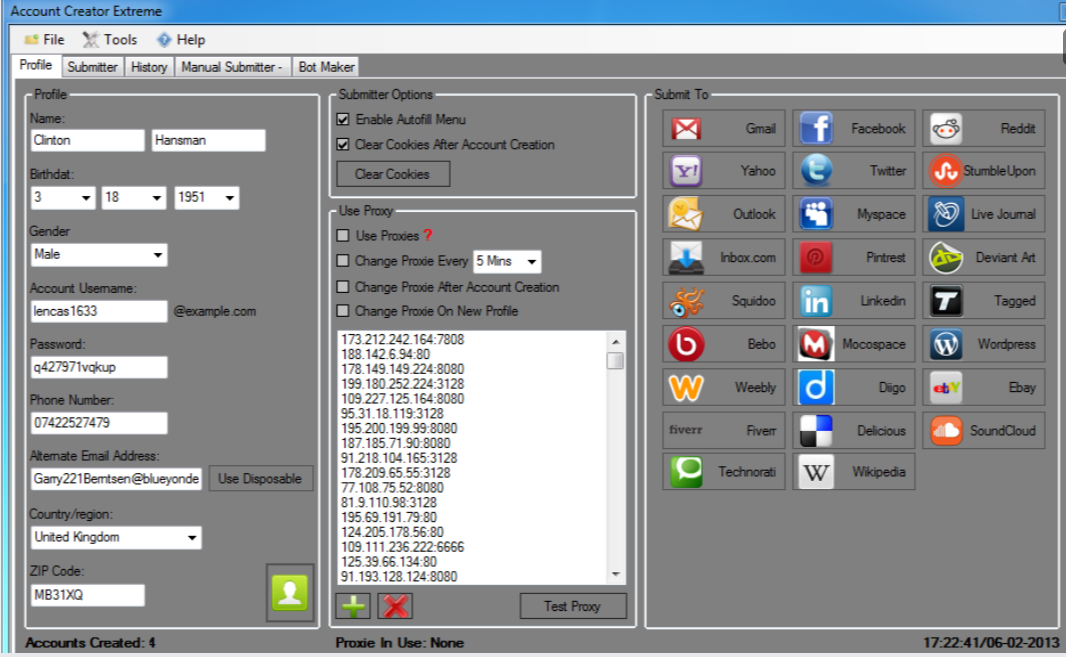
Account Creator Extreme 4.2
Short Intro: Account Creator Extreme 4.2 serves as an essential cybersecurity tool for researchers and ethical hackers aiming to simulate real-world account creation challenges. It enables rapid deployment of accounts for vulnerability assessments and security training, reducing manual effort by up to 90%. The key USP is its intelligent algorithm that adapts to evolving platform […]
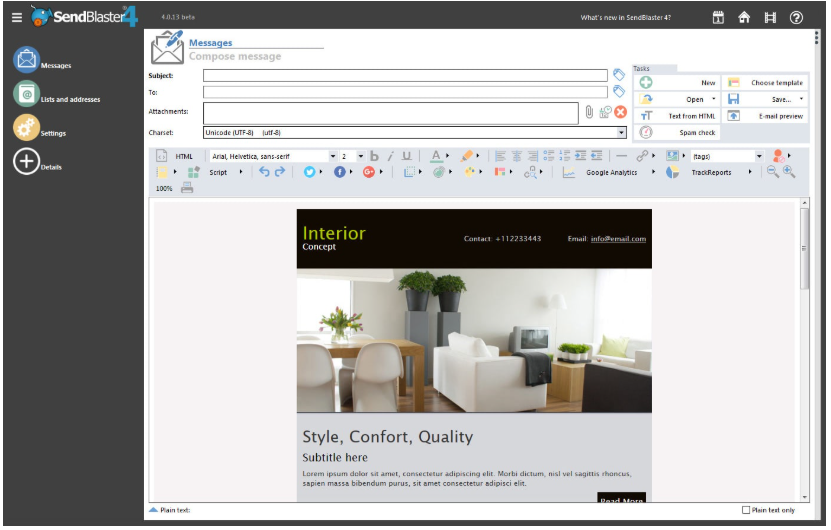
SendBlaster Pro Version 4.1.13 Activated
Discover our cutting-edge cybersecurity tool designed to protect businesses from evolving threats in 2026. This innovative solution empowers organizations with advanced threat detection and response capabilities, ensuring robust defense against cyber attacks. Its unique selling point is real-time AI-driven analysis that adapts to new vulnerabilities, keeping your network secure without disrupting operations. Feature Explanations: Advanced […]