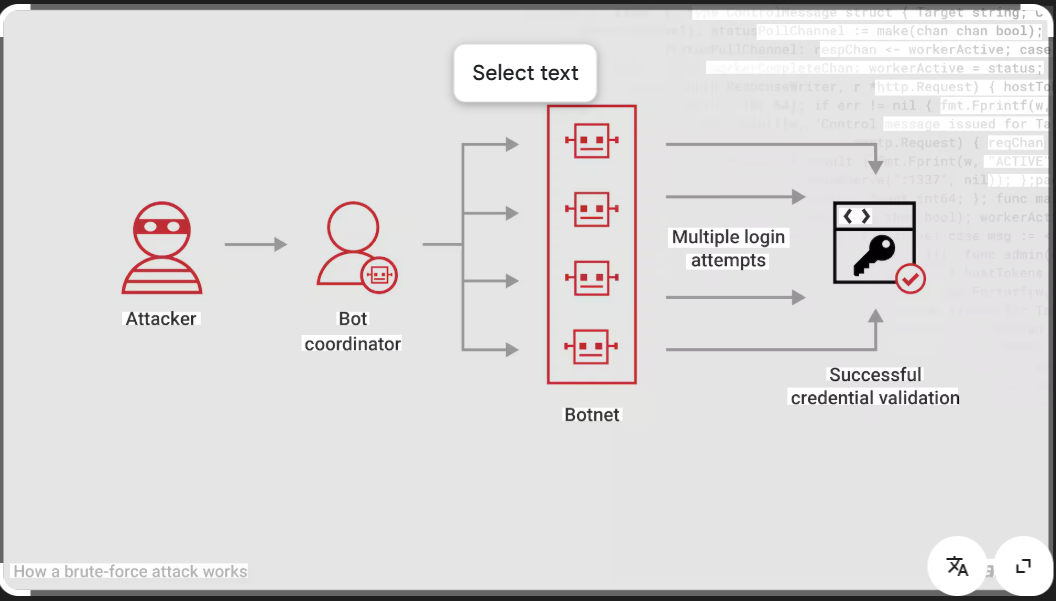
Bruter
Here are all types of bruter like Password Bruters, Hash Bruters, Wi-Fi Bruters, API/Token Bruters, ZIP/RAR Bruters, Credential Stuffing Tools.
Introducing Cyborg Version 3.9.2 – The 2026 Leader in Security Tools
Short Intro: Cyborg Version 3.9.2 stands out as a robust cybersecurity tool built for identifying and neutralizing digital risks across industries. Its core purpose is to deliver comprehensive protection through innovative features that streamline security assessments. What sets it apart is its adaptive AI capabilities, ensuring defenses evolve faster than threats in the dynamic landscape […]
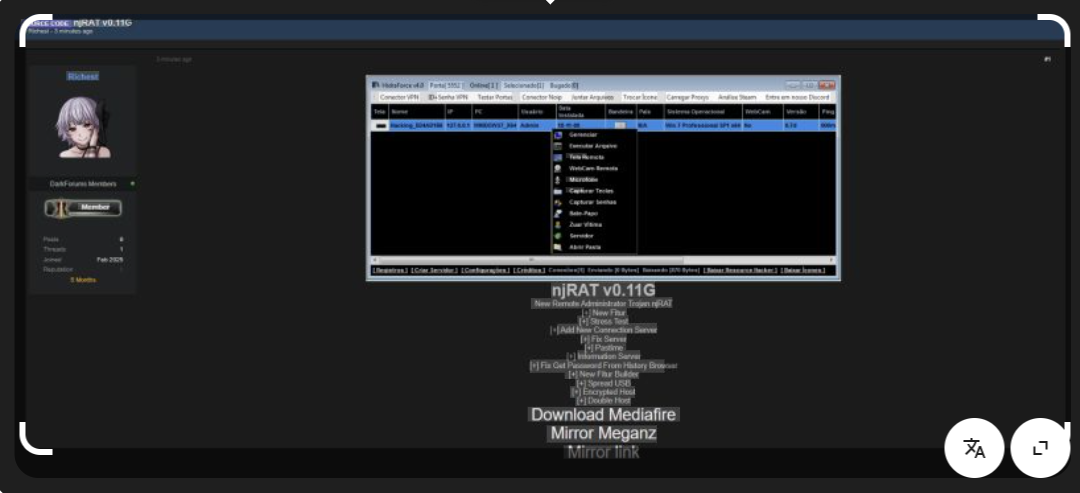
njRAT v0.11g Secure Remote Access in Cybersecurity for 2026
Short Intro: njRAT v0.11g stands out as a cutting-edge remote access tool tailored for cybersecurity experts aiming to fortify defenses through rigorous testing. It serves to emulate hacker techniques safely, identifying weaknesses before real attacks occur. What sets it apart is its user-friendly interface combined with stealthy operation, making it indispensable for professionals tackling 2026’s […]
Discover SpyGate RAT 3.2 Advanced Remote Monitoring in 2026
Short Intro: SpyGate RAT 3.2 is a powerful cybersecurity tool designed for professionals to conduct remote access and surveillance operations ethically. Its primary purpose is to enhance network security through discreet monitoring and data retrieval, ensuring organizations stay ahead of threats. The key USP is its stealthy operation mode, which minimizes detection while delivering real-time […]
Net Tools 5.0.70 Advanced Network Suite 2026
Short Intro: Net Tools 5.0.70 is a comprehensive pro hacking toolkit designed for cybersecurity experts and ethical hackers. It empowers users to analyze networks, detect vulnerabilities, and enhance security protocols with unparalleled precision. Its standout USP is the seamless integration of automated scanning and real-time reporting, making it indispensable for modern penetration testing. Download Link […]
CPanel Attacker v4 for 2026 Penetration Mastery
Short Intro: CPanel Attacker v4 stands out as a robust cybersecurity utility tailored for professionals aiming to test the resilience of CPanel-based systems. It serves to identify and exploit potential entry points in web hosting infrastructures, fostering proactive security measures. What sets it apart is its AI-enhanced targeting, which adapts to 2026’s sophisticated defenses for […]
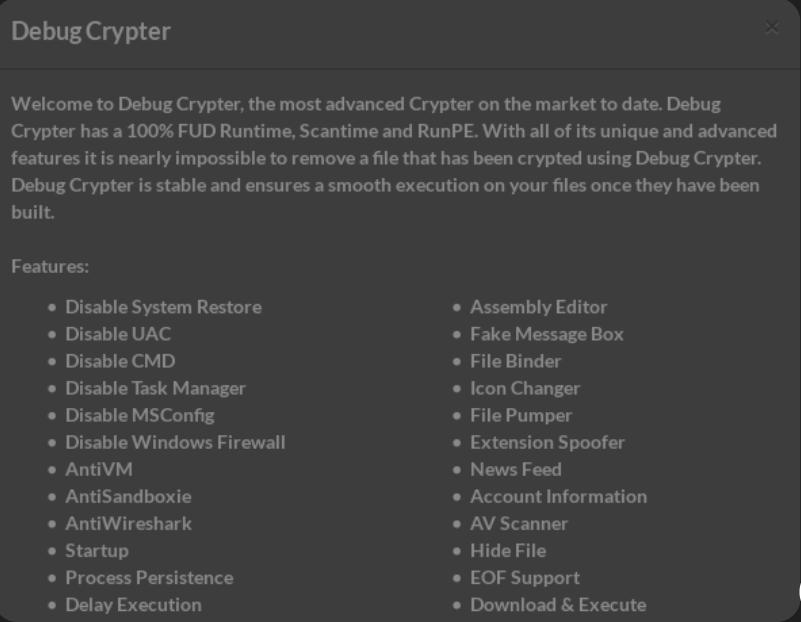
Psychonix Crypter 2026 Revolutionizing Malware Obfuscation for Secure Hacking
Short Intro: Introducing Psychonix Crypter 2026, a sophisticated cybersecurity utility that transforms malware into undetectable forms through advanced encryption. Tailored for researchers and security professionals, it serves to facilitate controlled testing environments without compromising integrity. What sets it apart is its proprietary zero-day evasion technology, unmatched in the 2026 threat landscape. Download Link 1 Download […]
File Crypter 2026 The Leading Cybersecurity Solution for File Encryption
Short Intro: Introducing File Crypter 2026, a cutting-edge cybersecurity tool engineered to encrypt files and shield valuable information from cyber threats. It serves to bolster data integrity by converting plain files into secure, encrypted formats that only authorized users can access. Its standout USP is the integration of AI-driven algorithms that adapt to emerging threats, […]
Unlock Ultimate Cybersecurity with Cold Seal 5.6 Cracked
Short Intro: Cold Seal 5.6 Cracked is a powerful cybersecurity tool designed to safeguard digital assets against evolving threats. It offers robust encryption and real-time monitoring to protect users from data breaches and cyberattacks. The key USP is its cracked version, providing premium features without licensing costs for enhanced accessibility in 2026. Feature Explanations: Advanced […]
Revolutionize Your Cybersecurity Arsenal with Blade Stealer 1.0
Short Intro: Blade Stealer 1.0 emerges as a powerful cybersecurity tool crafted for penetration testers to replicate sophisticated data theft techniques. It serves to identify and exploit weaknesses in digital defenses by extracting critical assets such as login details and financial tokens. What sets it apart is its AI-driven evasion tactics, which help bypass modern […]
njBrute Force 2.1Leading Brute Force Cybersecurity Solution for 2026
Short Intro: Introducing njBrute Force 2.1, a powerful cybersecurity utility tailored for penetration testers and security experts. Its primary purpose is to conduct controlled brute force evaluations on authentication mechanisms, helping organizations fortify their digital perimeters. What sets it apart is its unparalleled speed and resource efficiency, delivering results up to three times faster in […]