Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
ARES RAT v1.2.1 Cracked
ARES RAT (Remote Access Trojan) is a powerful surveillance and control malware used for remote system administration—often exploited for unauthorized access. The cracked v1.2.1 version circulates in underground forums, allowing hackers to bypass licensing restrictions. While originally marketed as a legitimate remote tool, its misuse poses severe cybersecurity threats, making it essential for security professionals to understand […]
DaRKDDoSeR 5.6c Cracked
DaRKDDoSeR 5.6c Cracked is a modified version of a network stress-testing tool that simulates DDoS (Distributed Denial of Service) attacks. While the original software was designed for legitimate penetration testing, cracked versions often circulate in underground forums, posing significant risks. This article examines its technical aspects, ethical concerns, and defensive applications for cybersecurity professionals. Download Link 1 Download Link 2 […]
Top Powerfull DDOs attack tools 2024
Distributed Denial-of-Service (DDoS) attacks remain one of the most disruptive threats to online services, overwhelming networks with malicious traffic. While ethical hackers and cybersecurity professionals use these tools for stress testing and defense simulations, malicious hackers exploit them to take down websites and services. This article explores the most powerful DDoS tools in 2024, their […]
Orion Keylogger 2.1 Cracked
Orion Keylogger 2.1 Cracked is an illicitly modified version of the original Orion Keylogger, a stealthy surveillance tool designed to record keystrokes, capture screenshots, and steal sensitive data. While the legitimate version may be used for parental control or employee monitoring, the cracked variant is often distributed through malware forums and phishing scams, posing severe risks to cybersecurity and […]
Athena HTTP Botnet Builder 2024
The Athena HTTP Botnet Builder 2024 is a powerful and sophisticated toolkit designed to create, manage, and deploy botnets for large-scale cyberattacks. Unlike traditional botnets, Athena leverages HTTP-based communication for stealthier operations, making it harder to detect and block. It is widely used in DDoS attacks, credential stuffing, and data exfiltration, posing a significant threat to enterprises and individuals alike. […]
Cooked Grabber 2024
Cooked Grabber 2024 is a sophisticated information-stealing malware designed to extract sensitive data from compromised systems. Often distributed through phishing attacks or malicious downloads, it targets credentials, cookies, cryptocurrency wallets, and other valuable information. Cybersecurity experts categorize it as a significant threat due to its stealthy operation and advanced evasion techniques. Download Link 1 Download […]
SEO Content Machine v4.17 Cracked
SEO Content Machine v4.17 Cracked is a robust content generation and automation tool tailored for digital marketers, SEO professionals, and content creators looking to produce high-volume, SEO-optimized content efficiently. This cracked release unlocks full premium access, allowing users to generate, spin, and post content across various platforms without license restrictions. What is SEO Content Machine […]
Venom RAT v5.6 Cracked
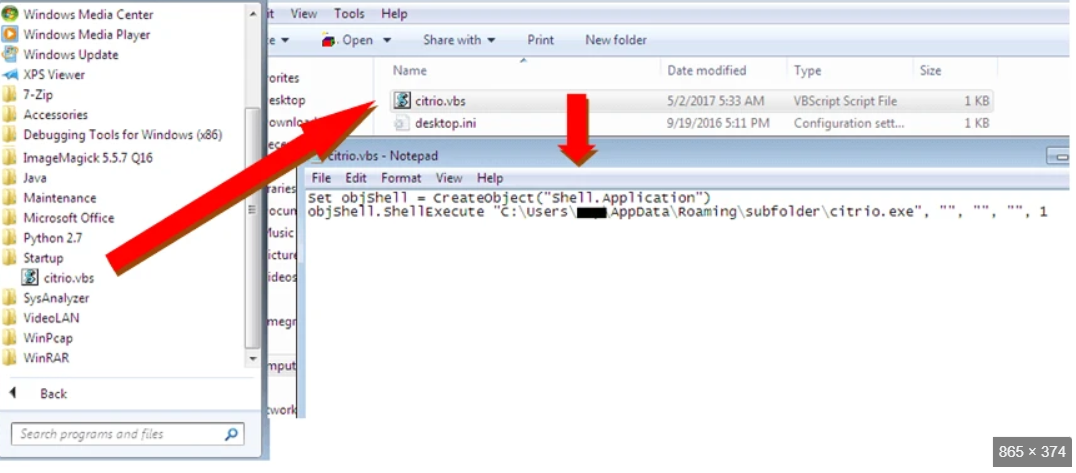
Venom RAT V5.6 Cracked has emerged as a formidable threat in the cybercrime landscape, representing a cracked version of a commercial remote administration tool now weaponized for malicious purposes. This sophisticated malware has been actively deployed in attacks against businesses, government agencies, and individual users, demonstrating alarming capabilities in stealth and persistence. Security analysts have […]
HIDDENZ HVNC TOOLS 2025
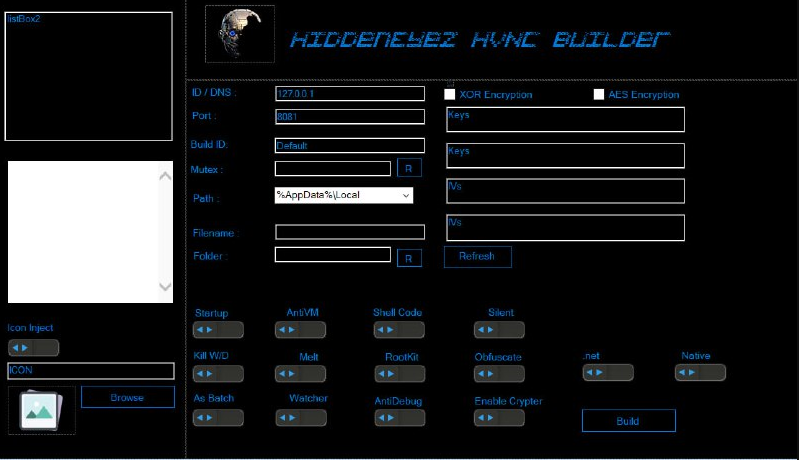
The cybersecurity landscape faces an escalating threat from advanced remote access tools designed to operate undetected on compromised systems. Among these, HIDDENZ HVNC TOOLS 2025 represents a sophisticated evolution in stealth malware technology, enabling attackers to maintain persistent, invisible access to victim machines. This toolkit leverages Hidden Virtual Network Computing (HVNC) technology to bypass traditional […]
Loki Stealer V5 Final Release
Cyber threats continue to evolve, with malicious actors leveraging advanced tools to bypass security measures and compromise systems. One such tool, often distributed through underground forums, is designed to steal sensitive information while evading detection. Loki Stealer V5 Final Software exemplifies the growing sophistication of modern cyberattacks, where stealth and functionality combine to target sensitive information, […]