Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Silent Crypto Miner Builder 2025
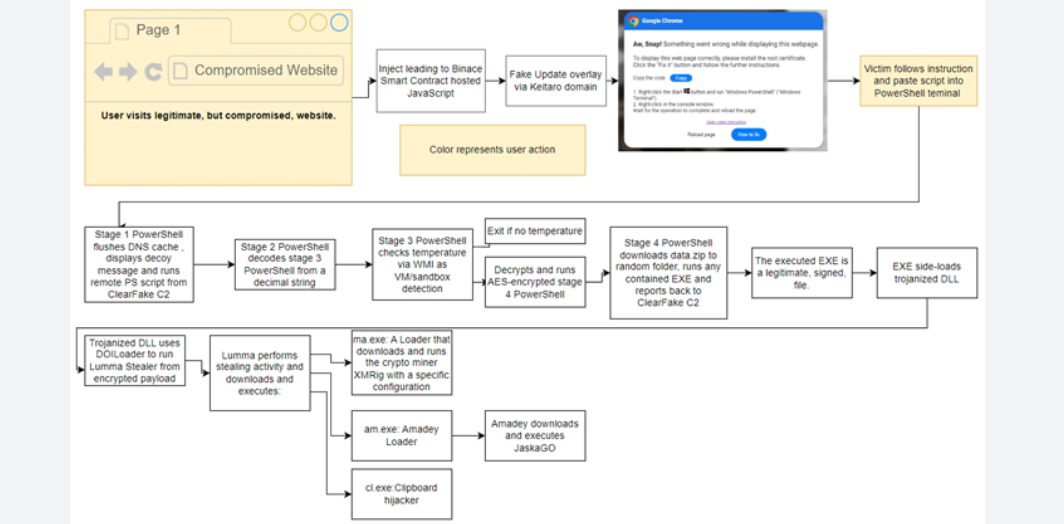
Cryptojacking has become a lucrative and stealthy cyberattack method, where attackers hijack a victim’s computing resources to mine cryptocurrency without their knowledge. Tools like Silent Crypto Miner Builder 2025 enable malicious actors to create and distribute customized mining malware with ease. These miners often evade detection by mimicking legitimate processes, consuming CPU/GPU power silently, and […]
Verci Spy System RAT Cracked 2024
Verci Spy System RAT Cracked 2024 has emerged as a significant threat in the cybercrime landscape, representing a cracked version of a commercial surveillance tool now weaponized for malicious purposes. This sophisticated remote access trojan has been observed in targeted attacks against businesses, government agencies, and high-net-worth individuals, demonstrating alarming capabilities in stealth and persistence. […]
Nimrod Stealer 2025
Cyber threats continue to evolve, with information-stealing malware playing a significant role in modern attacks. One such example is a sophisticated stealer that emerged in recent years, capable of extracting sensitive data from infected systems while evading detection. Nimrod Stealer 2025 of malware is often distributed through phishing campaigns, malicious downloads, or exploit kits, targeting […]
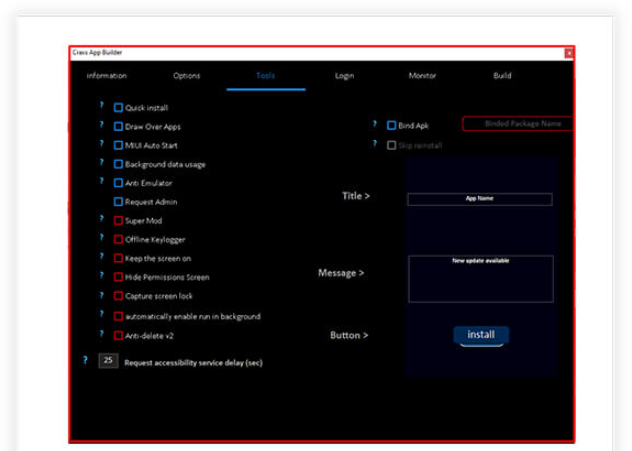
HACK PACK Crypters, Binders, Keyloggers and more
Cybercriminals increasingly rely on specialized tools to evade detection and deliver malicious payloads effectively. Among these tools, crypters, binders, and keyloggers play a critical role in modern cyberattacks. Crypters obfuscate malware to bypass antivirus detection, while binders merge malicious files with legitimate ones to deceive users into executing them. Keyloggers stealthily capture sensitive input, such […]
Lucifer v.1.2 HTTP Botnet
Lucifer v.1.2 HTTP Botnet has emerged as a sophisticated hybrid malware strain combining cryptocurrency mining and DDoS capabilities, representing a significant evolution in modern botnet technology. This malicious software has been actively deployed in attacks against corporate networks and individual users worldwide, demonstrating particular effectiveness due to its dual-purpose design and resilient infrastructure. Security researchers […]
VenomRAT 6.0.3 CRACKED
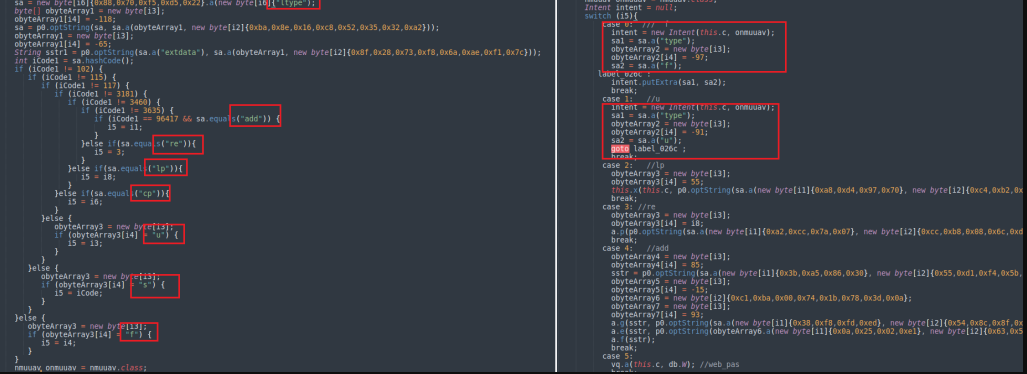
In the evolving landscape of cyber threats, remote access trojans (RATs) continue to be a persistent tool for malicious actors. One such example is VenomRAT 6.0.3 CRACKED, a well-known remote access tool (RAT) that has been increasingly leveraged in targeted attacks. This malware enables attackers to gain unauthorized control over infected systems, exfiltrate sensitive data, and […]
BRATA RAT 2025
BRATA RAT 2025 represents a dangerous evolution in financial malware, combining sophisticated remote access capabilities with advanced banking fraud techniques. This latest iteration of the notorious Trojan has been observed in targeted attacks against financial institutions and their customers across multiple continents. Security analysts have documented its improved evasion techniques and modular architecture, allowing attackers […]
Rafel Rat 2025
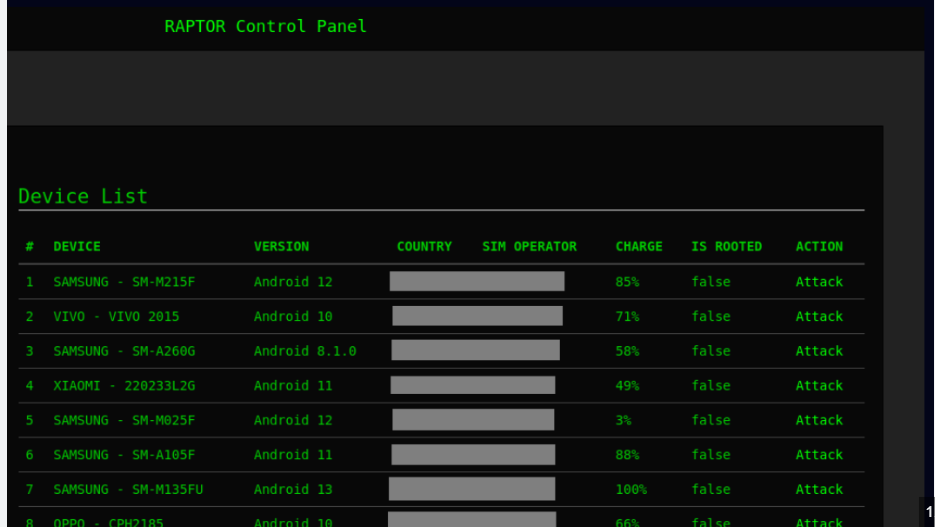
In recent years, cybercriminals have increasingly relied on sophisticated tools to carry out attacks, with one notable example being a particular remote access trojan (RAT) that has gained notoriety in underground forums. Rafel Rat 2025 malware, often distributed through cracked or pirated software, enables attackers to gain complete control over compromised systems. Its modular design […]
Doge Rat 2025
The “Doge Rat 2025” is a sophisticated remote access trojan (RAT) that has emerged as a significant threat in modern cyberattacks. Unlike traditional malware, this tool grants attackers complete control over compromised systems, allowing for data theft, surveillance, and further network infiltration. Its modular design and evasion techniques make it particularly dangerous, as it can […]
Cypher RAT v3 Full Version
Cypher RAT v3 Full Version—Lifetime has become a concerning presence in modern cyberattacks, representing a sophisticated remote access trojan (RAT) that offers attackers long-term control over compromised systems. This commercial-grade surveillance tool, now widely distributed in underground markets, provides cybercriminals with enterprise-level capabilities at an affordable price point. Security analysts have observed its increasing use […]