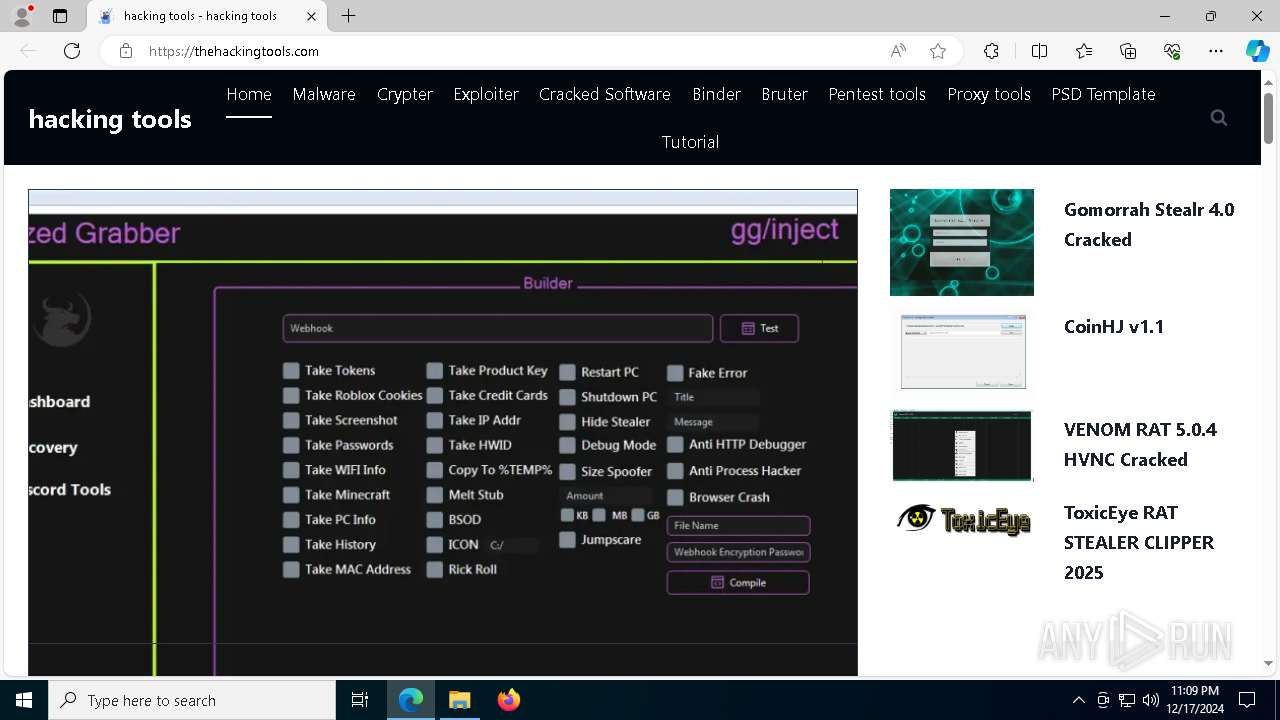
Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
PEGASUS RAT 2024 FULL VERSION SOURCE
Cyberattacks have grown increasingly sophisticated, with advanced remote access trojans (RATs) becoming a favored tool for threat actors. These malware strains enable attackers to infiltrate systems, exfiltrate sensitive data, and maintain long-term access without detection. Among these threats, highly customizable RATs—often distributed through exploit kits, phishing, or zero-day vulnerabilities—pose significant risks to governments, corporations, and […]
X-FILES STEALER CRACKED 2024
The rise of information-stealing malware has significantly impacted modern cyberattacks, with tools like “X-FILES STEALER CRACKED” becoming a notable threat. These malicious programs are designed to exfiltrate sensitive data from compromised systems, often targeting credentials, financial information, and personal documents. Cracked or pirated versions of such software are particularly dangerous, as they are distributed freely […]
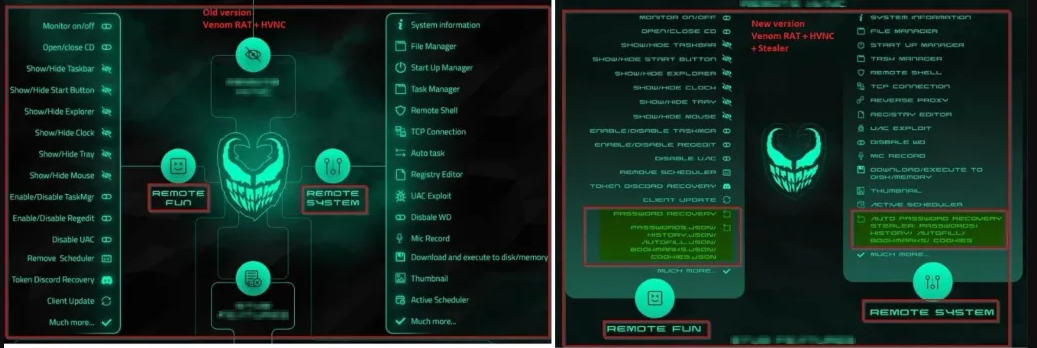
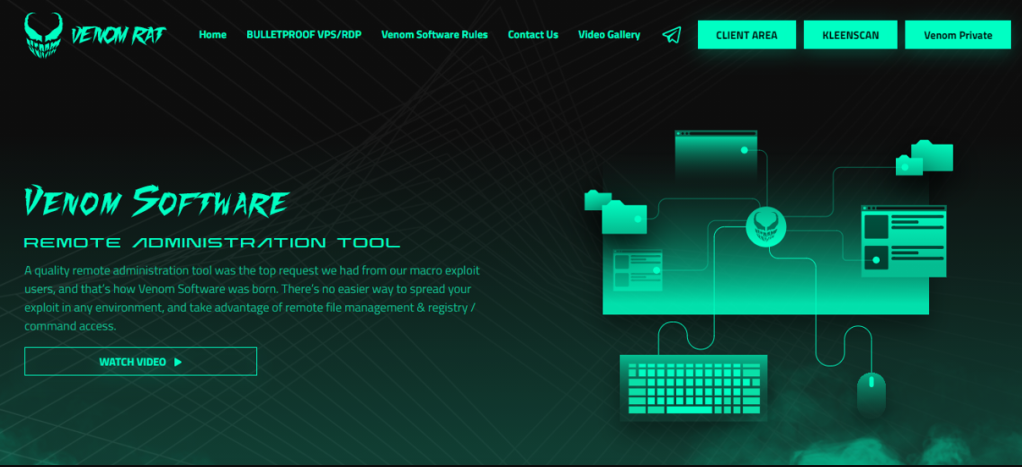
VENOM RAT 2.8 FINAL HRDP LOCKER HVNC RAT
Cyber threats continue to evolve, with remote access trojans (RATs) playing a significant role in modern cyberattacks. These malicious tools provide attackers with unauthorized control over compromised systems, enabling data theft, surveillance, and further network infiltration. Among these threats, advanced RATS stand out due to their stealth, persistence, and ability to bypass security measures. VENOM […]
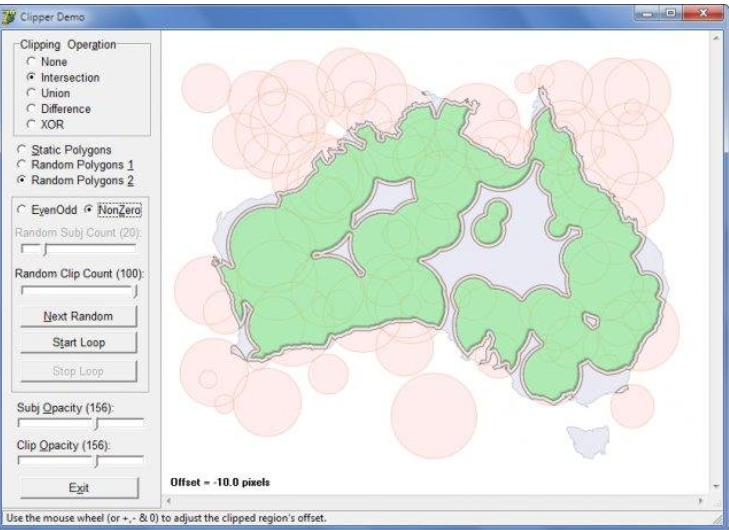
Redline Clipper Cracked 2024
Cybercriminals continuously evolve their tools to bypass security measures, and one such tool gaining attention is the “Redline Clipper Cracked 2024.” This malicious software has been increasingly observed in modern cyberattacks, particularly in credential theft and financial fraud. By manipulating clipboard contents in real time, attackers can redirect cryptocurrency transactions or steal sensitive data without […]
BTC Grabber Builder 2.0
The cryptocurrency ecosystem faces growing threats from sophisticated malware tools, with BTC Grabber Builder 2.0 emerging as a particularly dangerous weapon in modern cyberattacks targeting digital assets. This advanced malware creation kit demonstrates how cybercriminals are developing specialized tools to exploit cryptocurrency transactions and storage methods. BTC Grabber Builder 2.0 has been actively used in […]
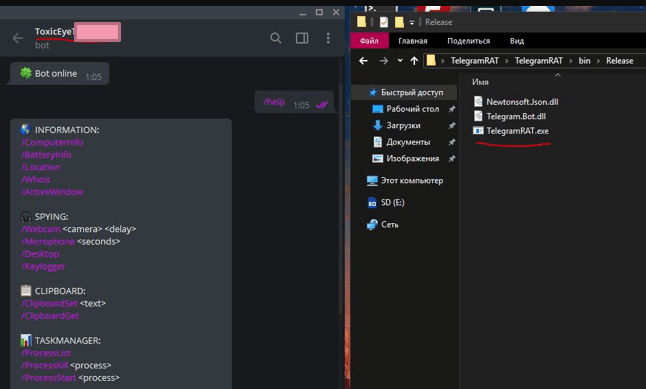
ToxicEye RAT STEALER CLIPPER 2025
Modern cyberattacks increasingly leverage multi-functional malware that combines multiple malicious capabilities into a single, potent threat. Among these, hybrid malware that blends remote access functionality with data theft and financial fraud features has become particularly dangerous. The 2025 version of ToxicEye RAT STEALER CLIPPER demonstrates how cybercriminals are evolving their tools to maximize impact, combining […]
Prosto Clipper 2024
Cybercriminals are constantly refining their tools to exploit financial transactions, and one such threat, often referred to as Prosto Clipper 2024, has become a significant concern in modern cyberattacks. This malware specializes in intercepting and altering cryptocurrency transactions by silently modifying clipboard contents, redirecting funds to attacker-controlled wallets. Unlike ransomware or traditional stealers, this type of […]
VENOM RAT 5.0.4 HVNC Cracked
Remote Access Trojans (RATs) continue to evolve as one of the most dangerous tools in a cybercriminal’s arsenal, enabling complete takeover of compromised systems. The emergence of cracked, commercially available RATs has lowered the barrier to entry for attackers, allowing even low-skilled threat actors to conduct sophisticated intrusions. The latest versions of these tools incorporate […]
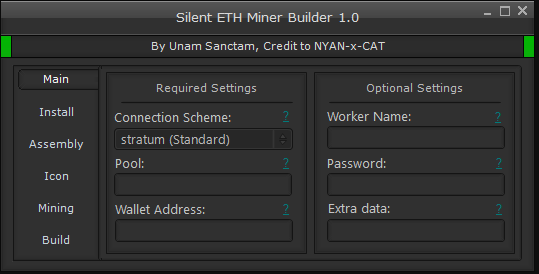
Silent ETH Miner v1.6.0
The cryptocurrency mining landscape has seen a surge in malicious cryptojacking attacks, with Silent ETH Miner v1.6.0 emerging as a particularly stealthy and efficient threat in modern cyberattacks. This sophisticated mining malware demonstrates how cybercriminals are exploiting system resources for unauthorized cryptocurrency mining without user consent. Silent ETH Miner v1.6.0 has been actively used in […]
CoinHJ v1.1 – Crypto Coin Clipboard Hijacker
Cryptocurrency-related malware has become increasingly prevalent as digital currencies gain mainstream adoption. Among these threats, clipboard hijackers have emerged as a particularly insidious tool for cybercriminals. CoinHJ v1.1 operates silently in the background, monitoring and manipulating clipboard activity to redirect cryptocurrency transactions. The latest versions of such malware demonstrate improved stealth capabilities and broader targeting […]