Orcus 1.9 Official Stable Release – AntiTakedown (Multilingual)
Orcus RAT (Remote Access Trojan) has long been a controversial tool in cybersecurity circles. The 1.9 Official Stable Release – AntiTakedown (Multilingual) version introduces enhanced evasion techniques, multilingual support, and improved remote control capabilities. While ethical hackers may use such tools for penetration testing and security research, unauthorized deployment is illegal and poses serious risks to privacy […]
Keylogger Pack 2024
Keyloggers remain one of the most potent tools for capturing user input, recording keystrokes, and monitoring system activity. While often associated with unauthorized surveillance, ethical hackers and IT professionals use keyloggers for employee monitoring, parental control, penetration testing, and forensic investigations. This article explores the most advanced Keylogger Packs of 2024, their features, and their legitimate cybersecurity […]
AZORULT 3.3 PANEL + BUILDER COOKIES / PASSWORD STEALER
AZORULT 3.3 is a notorious information-stealing malware widely used by hackers to harvest sensitive data, including browser cookies, saved passwords, cryptocurrency wallets, and system information. The latest version includes a user-friendly builder and control panel, making it easier for attackers to customize and distribute the malware. Known for its stealthy operation and evasion techniques, AZORULT remains a […]
Anubis android banking bot
Anubis is a notorious Android banking trojan designed to steal sensitive financial data, including banking credentials, credit card details, and cryptocurrency wallets. First identified in 2017, it has evolved into a modular malware-as-a-service (MaaS) platform, offering hackers a powerful tool for financial fraud and identity theft. Distributed via malicious apps, phishing, and fake updates, Anubis remains a persistent threat to mobile […]
THs Batch Virus Maker V2.0
THs Batch Virus Maker V2.0 is a notorious tool designed to create malicious batch file (.bat) viruses with minimal technical knowledge. Often distributed in underground hacking forums, this software allows attackers to generate destructive scripts that can corrupt files, disable system functions, or spread across networks. While marketed as an “educational tool,” it is primarily used for cyber vandalism, ransomware attacks, and […]
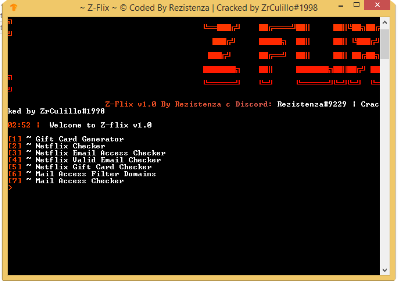
Z-Flix
Z-Flix is a cutting-edge streaming service designed to deliver high-quality video content with enhanced user customization and seamless performance. Combining advanced technology with an intuitive interface, Z-Flix offers a premium entertainment experience for modern viewers. The platform prioritizes speed, accessibility, and content diversity while maintaining robust security measures. What Is Z-Flix? Z-Flix is a subscription-based […]
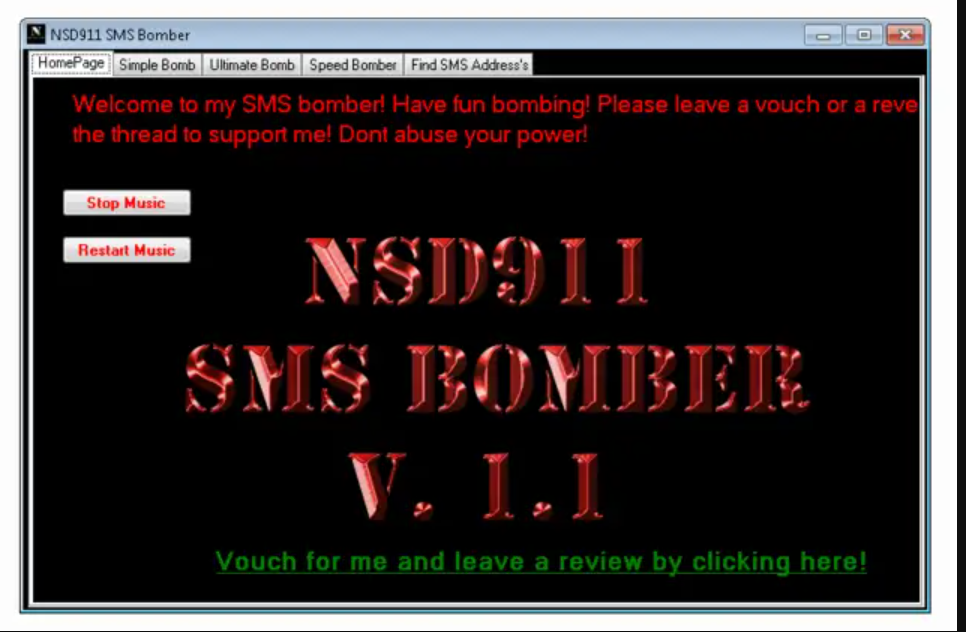
NSD SMS Bomber 2024
In the ever-evolving digital landscape, tools like NSD SMS Bomber 2024 have garnered attention for their ability to send bulk SMS messages rapidly. While such tools can serve legitimate purposes like testing communication systems, they are often controversial due to potential misuse. This article delves into what NSD SMS Bomber is, its features, and its applications. […]
Arcom v1.5 Cracked
Arcom v1.5 Cracked is a modified version of the original Arcom information-stealing malware, widely used by hackers to harvest sensitive data from infected systems. This cracked variant bypasses licensing restrictions, making it accessible on underground hacking forums. It specializes in stealing browser credentials, cryptocurrency wallets, and system information, posing a severe threat to both individuals and organizations. […]
Arctic Miner Cracked 2024
Arctic Miner Cracked 2024 is an unauthorized, modified version of legitimate cryptocurrency mining software, repackaged to bypass licensing and enable malicious cryptojacking. This cracked variant is commonly distributed through pirated software sites, malicious ads, and phishing campaigns, secretly hijacking victims’ computing power to mine cryptocurrencies like Monero (XMR) or Bitcoin (BTC). Unlike ethical mining tools, it operates stealthily without user […]
Rat Collections 2024
Remote Access Trojans (RATs) are powerful tools that allow hackers to control systems remotely. While often associated with malicious activities, ethical hackers and security professionals use RATs for penetration testing, incident response, and system administration. This article explores the most advanced RAT Collections of 2024, their functionalities, and their legitimate applications in cybersecurity. Download Link 1 […]