Prynt Stealer Cracked 2024
Cybercriminals increasingly rely on stealthy and efficient malware to carry out data theft, financial fraud, and espionage. Among these threats, information stealers have become a preferred tool due to their ability to harvest sensitive data with minimal detection. Prynt Stealer 2024 further lowers the barrier to entry, enabling even less skilled attackers to deploy sophisticated […]
XWORM V2.1 CRACKED
The proliferation of cracked malware variants has become a significant concern in the cybersecurity landscape, with threat actors increasingly leveraging pirated versions of sophisticated attack tools to lower operational costs while maintaining high effectiveness. Among these, a particularly dangerous cracked specimen has emerged as a favorite among cybercriminals due to its modular design and robust […]
Remote Hacker Probe Pro v2
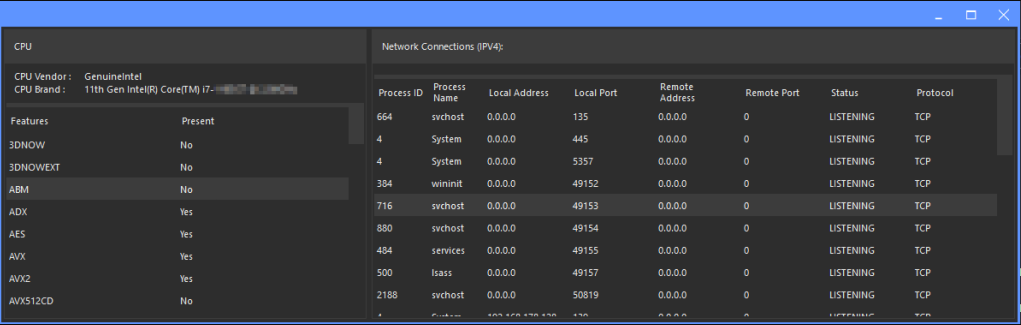
The cybersecurity landscape faces growing threats from sophisticated penetration tools, with Remote Hacker Probe Pro V.2 emerging as a particularly dangerous weapon in modern cyberattacks. This advanced remote access toolkit demonstrates how cybercriminals are professionalizing their operations with feature-rich, commercially inspired hacking software. Remote Hacker Probe Pro V.2 has been actively used in targeted attacks […]
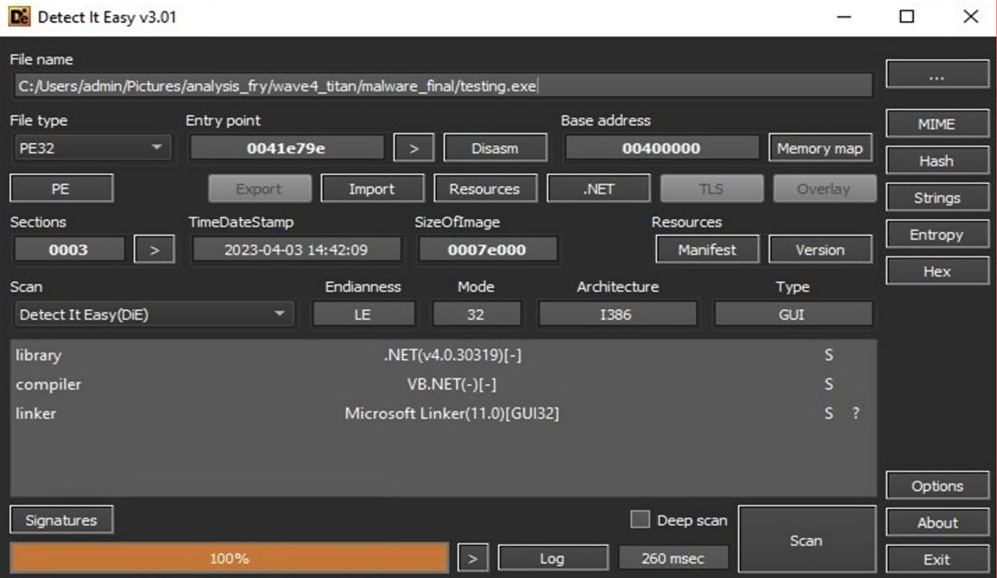
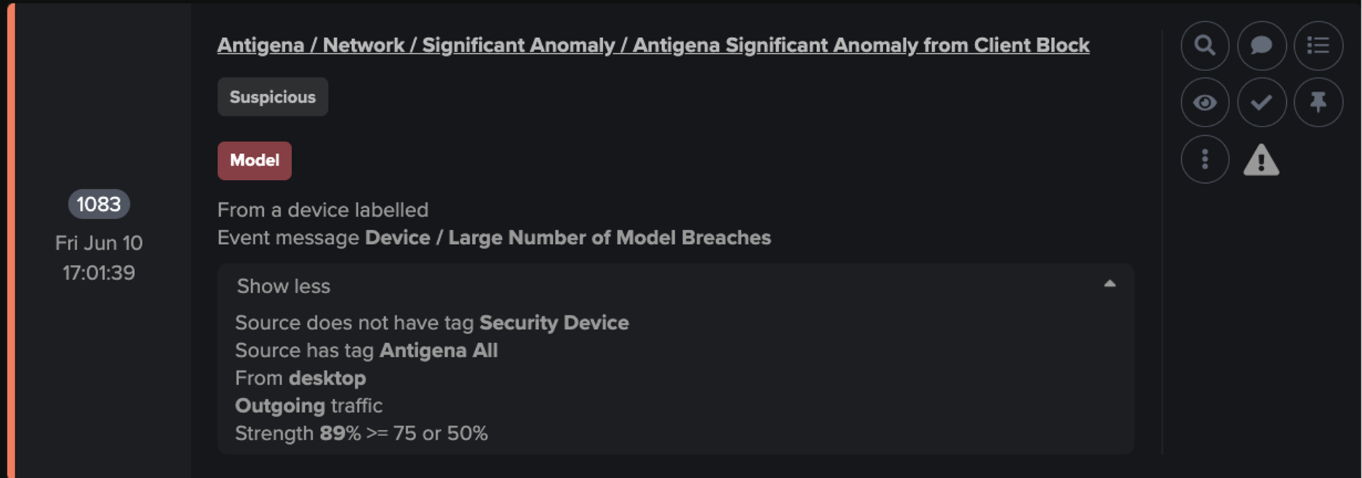
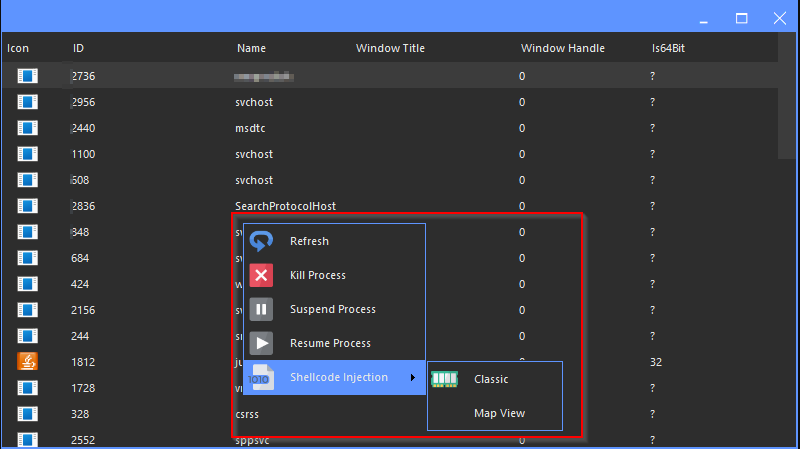
ICARUS RAT 2025 Cracked
The underground market for cracked remote access trojans (RATs) continues to thrive, providing cybercriminals with powerful surveillance tools at minimal cost. Among these offerings, a particularly dangerous cracked variant has emerged in 2025, combining professional-grade remote administration features with malicious capabilities optimized for covert operations. ICARUS RAT 2025 demonstrates how threat actors are leveraging pirated […]
EAGLE MONITOR RAT REBORN 3.2.1.0
The remote administration tool (RAT) landscape has evolved significantly, with modern variants blending legitimate remote access capabilities with sophisticated surveillance features. Among these, a particularly advanced strain has emerged that combines comprehensive system control with military-grade stealth techniques. EAGLE MONITOR RAT REBORN exemplifies the growing trend of dual-use surveillance tools that blur the line between […]
DCRat v1.0.7 Auto Build
The cybersecurity threat landscape continues to evolve with increasingly accessible malware tools, and DcRat v1.0.7 Auto Build has emerged as a particularly concerning example of democratized cyberattack capabilities. This automated remote access tool demonstrates how cybercriminals are lowering the technical barriers to sophisticated attacks through user-friendly malware builders. DcRat v1.0.7 Auto Build has been widely […]
KRIPTO CLIPPER 2025
Cybercriminals continually evolve their tactics to exploit vulnerabilities and steal sensitive data. One such tool that has gained notoriety in recent attacks is the “KRIPTO CLIPPER 2025,” a type of malware designed to hijack cryptocurrency transactions by manipulating clipboard data. This malware exemplifies the growing sophistication of cyber threats, particularly those targeting financial assets. Operating […]
ROGUE V6.2 ANDROID BOTNET PREMIUM
In the evolving landscape of cyber threats, Android botnets have become a significant tool for malicious actors. One such example is a sophisticated piece of malware designed to infiltrate Android devices, enabling remote control, data theft, and large-scale attacks. ROGUE V6.2 ANDROID botnets are often employed in distributed denial-of-service (DDoS) attacks, credential harvesting, and spam distribution, […]
Anubis 8.0
The mobile malware landscape has become increasingly dangerous with the emergence of sophisticated banking trojans that target financial applications across multiple platforms. Among these threats, a particularly advanced strain has evolved through multiple iterations to become one of the most pervasive mobile banking malware families in circulation. Anubis 8.0 exemplifies the growing trend of cross-platform […]
Eagle Monitor RAT 2025 Cracked
The cybersecurity landscape continues to evolve with increasingly sophisticated remote access threats, and Eagle Monitor RAT 2025 has emerged as one of the most dangerous surveillance tools in modern cyberattacks. This advanced remote administration tool demonstrates how cybercriminals are developing more stealthy and feature-rich malware for persistent system access. Eagle Monitor RAT 2025 has been […]