Free Download Enhance Database Security with SQL Poison v1.0
Short Intro: SQL Poison v1.0 stands out as a robust cybersecurity solution designed to combat SQL injection exploits that threaten enterprise databases. Its core purpose is to empower developers and IT professionals with proactive threat identification and resolution tools. What sets it apart is its proprietary algorithm, which adapts to emerging attack vectors, offering superior […]
Discover HackBase Steam Phisher 1.2 Beta
Short Intro: HackBase Steam Phisher 1.2 Beta stands out as a premier tool for simulating phishing exploits targeting Steam platforms. Its purpose is to empower cybersecurity researchers and teams to conduct thorough vulnerability assessments. The standout USP is its AI-driven adaptability, which predicts and counters emerging phishing tactics for proactive security measures. Feature Explanations: Customizable […]
Introducing Unlimited PW Stealer 2026 – Advanced Cybersecurity Software
Short Intro: Unlimited PW Stealer 2026 stands out as a premier cybersecurity solution tailored for professionals aiming to test and fortify password-related defenses. Its core purpose revolves around replicating sophisticated theft techniques to reveal systemic weaknesses in authentication protocols. A standout USP is its AI-driven detection evasion, which adapts to modern security measures for unparalleled […]
Armageddon Stealer 1.0 with Intelligent Stealing Simulations for 2026
Short Intro: Armageddon Stealer 1.0 stands out as a premier cybersecurity tool engineered to replicate and study information-stealing malware in maintained settings. It aims to equip IT teams with proactive tools to uncover weaknesses in data protection strategies. Distinguished by its unparalleled stealth simulation capabilities, it ensures ethical testing without compromising actual systems. Feature Explanations: […]
Revolutionize Your Cybersecurity Arsenal with Blade Stealer 1.0
Short Intro: Blade Stealer 1.0 emerges as a powerful cybersecurity tool crafted for penetration testers to replicate sophisticated data theft techniques. It serves to identify and exploit weaknesses in digital defenses by extracting critical assets such as login details and financial tokens. What sets it apart is its AI-driven evasion tactics, which help bypass modern […]
Fortify Networks Against Cyber Threats Using Death Stealer 2026
Short Intro: Death Stealer 2026 is an indispensable cybersecurity tool tailored for thwarting sophisticated data-stealing operations and insider threats. It aims to empower organizations by delivering comprehensive visibility into network activities and automating defense strategies. Its standout feature is the intelligent alerting system, which prioritizes risks based on severity, allowing for swift and effective interventions […]
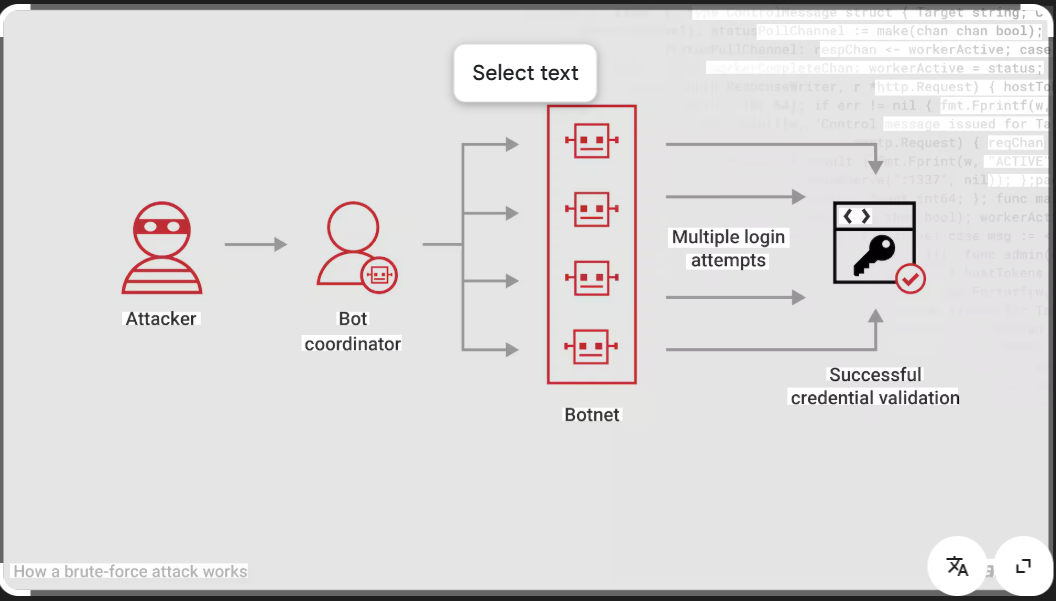
njBrute Force 2.1Leading Brute Force Cybersecurity Solution for 2026
Short Intro: Introducing njBrute Force 2.1, a powerful cybersecurity utility tailored for penetration testers and security experts. Its primary purpose is to conduct controlled brute force evaluations on authentication mechanisms, helping organizations fortify their digital perimeters. What sets it apart is its unparalleled speed and resource efficiency, delivering results up to three times faster in […]
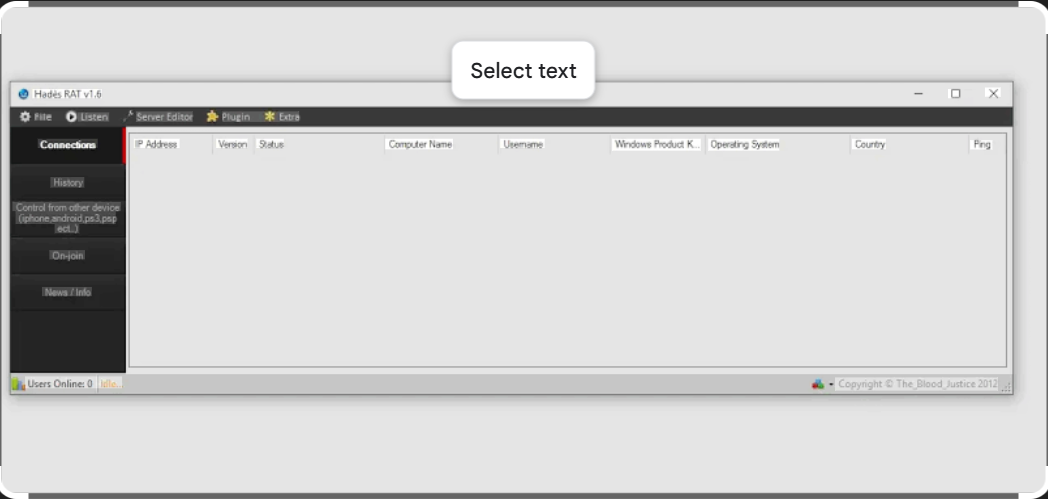
Powerful Remote Access Control with Hades RAT v1.6
Short Intro: is a cutting-edge remote access tool designed for advanced cybersecurity professionals and penetration testers. Its primary purpose is to enable secure, real-time monitoring and control of systems, making it indispensable for ethical hacking and vulnerability assessments. The key USP lies in its stealthy architecture, which evades detection while providing unparalleled efficiency in threat […]
Master Cybersecurity Defense Using EZCrack v1.7: Premier Tool for 2026
Short Intro: EZCrack v1.7 stands out as an innovative cybersecurity tool focused on strengthening defenses through simulated attacks and recovery strategies. It serves to educate and equip IT teams with insights into potential breaches. Its standout USP is the blend of simplicity and power, enabling rapid deployment without sacrificing depth in security evaluations. Feature Explanations: […]
Enhance Your Cybersecurity Arsenal with Cybernetic v1.62
Short Intro: Cybernetic v1.62 is an advanced cybersecurity tool designed to safeguard digital infrastructures against evolving threats. Its primary purpose is to provide real-time monitoring and automated defense mechanisms, ensuring businesses stay ahead of cyber risks. The key unique selling point is its AI-driven predictive analytics, which anticipates vulnerabilities before they can be exploited. Feature […]