BAS Stealer 7 Cracked
The cybercrime landscape continues to evolve with increasingly sophisticated data theft tools, and BAS Stealer 7 Cracked has emerged as a particularly dangerous threat in modern credential harvesting campaigns. This advanced information-stealing malware demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful attack tools at minimal cost. BAS Stealer 7 Cracked […]
novobot 2024
Novobot 2024, a sophisticated malware strain, emerged as a significant threat in modern cyberattacks, leveraging advanced evasion techniques to bypass traditional security measures. Dubbed Novobot 2024 by researchers, this malware has been linked to high-profile breaches, particularly in phishing campaigns and ransomware deployments. Its modular architecture and ability to dynamically adapt to different environments make […]
888 Rat v1.2.4 Cracked
The proliferation of cracked remote access tools has significantly lowered the barrier to entry for cybercriminals, enabling even novice attackers to launch sophisticated intrusions. These illicitly modified versions of commercial surveillance software bypass licensing restrictions and often include additional malicious payloads, making them particularly dangerous in the hands of threat actors. The availability of such […]
Apolon Loader Telegram WEB panel 2023
In recent years, cybercriminals have increasingly relied on sophisticated malware-as-a-service (MaaS) tools to distribute malicious payloads efficiently. One such tool, a Telegram-based web panel Apolon Loader Telegram, has gained notoriety for its ability to bypass security measures and deliver various types of malware. This loader is particularly dangerous due to its user-friendly interface, modular design, […]
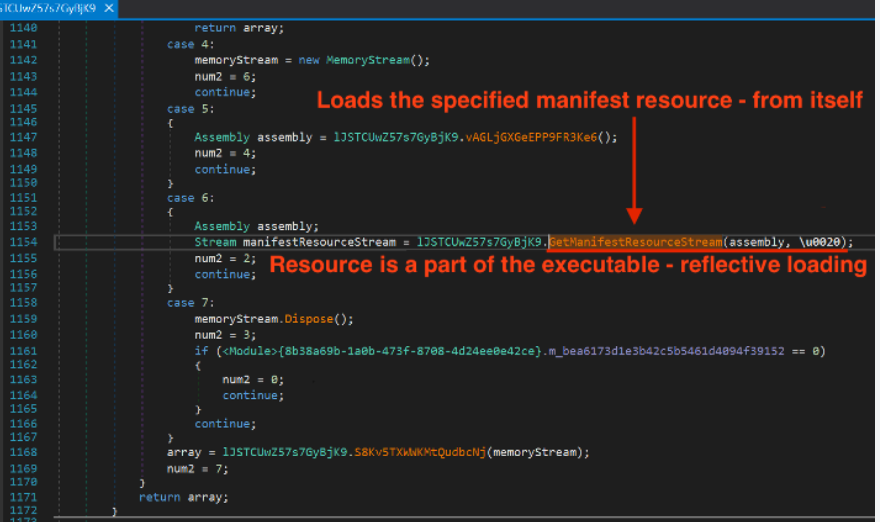
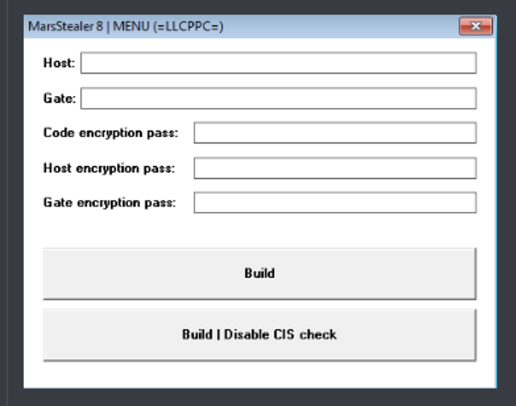
Mars Stealer v8
In the ever-evolving landscape of cybercrime, information-stealing malware has become increasingly sophisticated, with modern variants posing significant threats to individuals and organizations alike. These advanced threats specialize in covert data collection, credential harvesting, and financial fraud, often operating undetected for extended periods. The latest generation of these malicious tools demonstrates concerning improvements in evasion techniques, […]
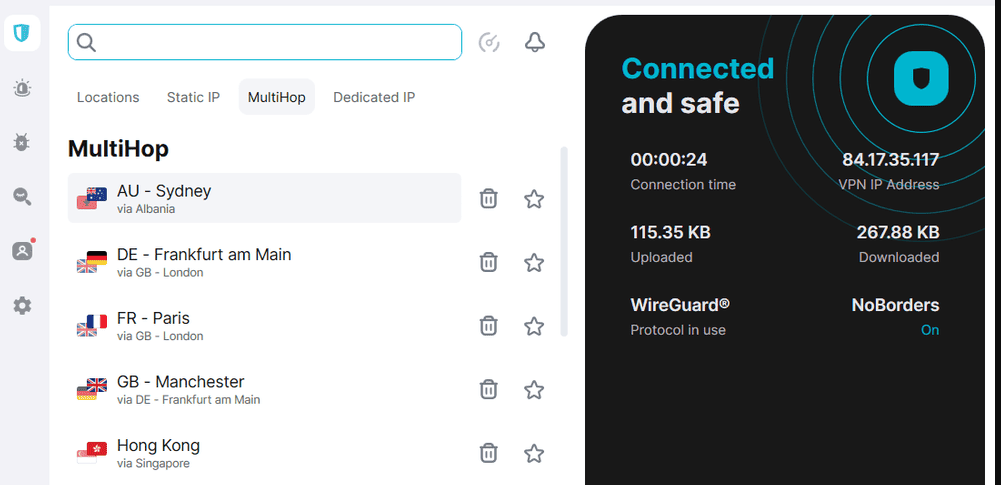
Multi VPN Checker 2025
In 2025, multi-VPN checkers have become a double-edged sword in cybersecurity. While legitimate users rely on them to verify VPN functionality and privacy, threat actors increasingly exploit these tools to conduct sophisticated cyberattacks. By testing multiple VPN connections, attackers can identify weak points, evade geo-restrictions, and mask their malicious activities. Multi VPN Checker 2025 makes […]
Beaver SMS Bomber 2025
In the evolving landscape of cyber threats, tools designed to disrupt communication systems have become a growing concern. Among these, SMS bombing software has gained notoriety for its ability to overwhelm targets with a flood of text messages, causing service disruptions, psychological distress, and even financial losses. Beaver SMS Bomber 2025 is often exploited in harassment […]
Netflix Ultimate Cracking Pack 2025
In 2025, credential-cracking tools designed for streaming platforms have evolved into a significant cybersecurity threat. Netflix Ultimate Cracking Pack 2025 tools, often marketed as a means to bypass paid subscriptions, are increasingly weaponized for large-scale credential-stuffing attacks, identity theft, and financial fraud. By exploiting weak authentication mechanisms and leaked credential databases, attackers can hijack accounts, […]
Crypto Stealer 2025 Cracked
The cryptocurrency ecosystem faces growing threats from increasingly sophisticated malware, with Crypto Stealer 2025 Cracked emerging as one of the most dangerous tools for digital asset theft. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful, low-cost attack tools. Crypto Stealer 2025 Cracked has been actively used […]
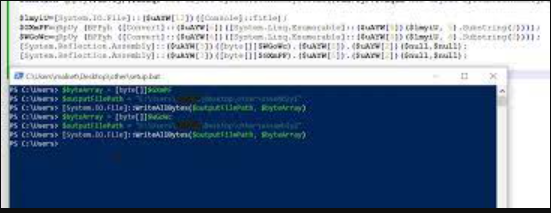
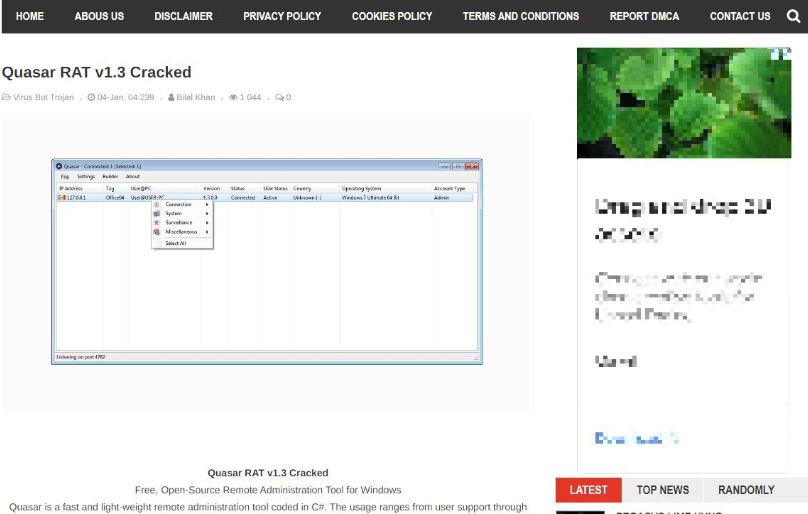
Quasar RAT v1.3 Cracked
Cyber threats continue to evolve, with remote access trojans (RATs) playing a significant role in modern attacks. One such tool, a cracked version of a well-known RAT, has spread widely across underground forums, enabling malicious actors to gain unauthorized access to systems. Quasar RAT v1.3 Cracked empowers attackers to conduct espionage, steal data, and deliver […]