Cracked Software
Here you can find all cracked software for hacking like emails, SMS, Whatsapp related as well as all cracking tools for you
Master Hack Pack Carding and Hacking Tools 2026
In the silent corners of 2026, the Master Hack Pack moves like smoke between hidden hands. This shadowy collection holds keys to carding empires and quiet hacking victories that never make headlines. Netflix Method and Amazon Prime Method open premium doors. PayPal flows through Double PayPal Method, Good PayPal Method, Greatest PayPal Method, and Best […]
94 Hack Pack of Crypters, Binders, Keyloggers 2026
As cybersecurity landscapes evolve rapidly in 2026, awareness of tools circulating in underground communities becomes essential for defense and education. The 94 HACK+PACK represents one such compilation that aggregates a wide variety of utilities commonly associated with unauthorized remote access, data capture, and payload protection. This article presents an objective overview and a complete listing […]
Armageddon Stealer 1.0 with Intelligent Stealing Simulations for 2026
Short Intro: Armageddon Stealer 1.0 stands out as a premier cybersecurity tool engineered to replicate and study information-stealing malware in maintained settings. It aims to equip IT teams with proactive tools to uncover weaknesses in data protection strategies. Distinguished by its unparalleled stealth simulation capabilities, it ensures ethical testing without compromising actual systems. Download Link […]
Death Stealer 2026
Short Intro: Death Stealer 2026 is an indispensable cybersecurity tool tailored for thwarting sophisticated data-stealing operations and insider threats. It aims to empower organizations by delivering comprehensive visibility into network activities and automating defense strategies. Its standout feature is the intelligent alerting system, which prioritizes risks based on severity, allowing for swift and effective interventions […]
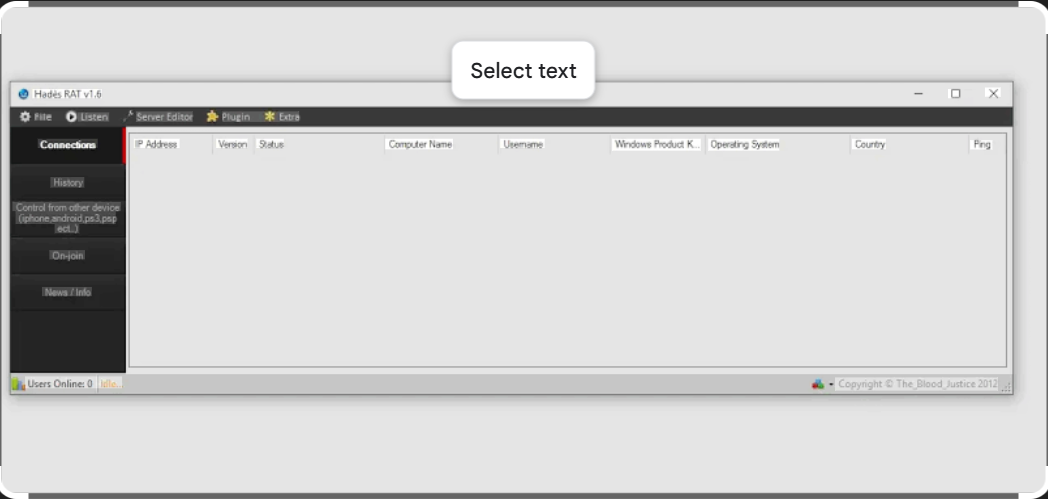
Powerful Remote Access Control with Hades RAT v1.6
Short Intro: is a cutting-edge remote access tool designed for advanced cybersecurity professionals and penetration testers. Its primary purpose is to enable secure, real-time monitoring and control of systems, making it indispensable for ethical hacking and vulnerability assessments. The key USP lies in its stealthy architecture, which evades detection while providing unparalleled efficiency in threat […]
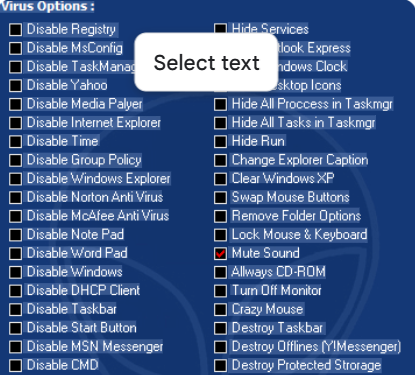
Powerful Virus Simulations Using JPS Virus Maker 2026 for Cyber Experts
Short Intro: empowers cybersecurity experts to craft and deploy simulated viruses for rigorous testing protocols. It serves the critical purpose of identifying weaknesses in systems before actual attacks occur. Its standout USP lies in automated obfuscation techniques that make the created viruses indistinguishable from real ones. Feature Explanations: Modular Virus Building: Assemble viruses using pre-built […]
Anonymous Attacker Package 2026
Short Intro: Introducing the Anonymous Attacker Package 2026, a specialized cybersecurity tool tailored for red team exercises and security audits. It empowers users to launch simulated attacks anonymously, pinpointing weak spots in digital infrastructures with precision. What sets it apart is its zero-log policy, guaranteeing that all activities remain completely untraceable during authorized use. Download […]
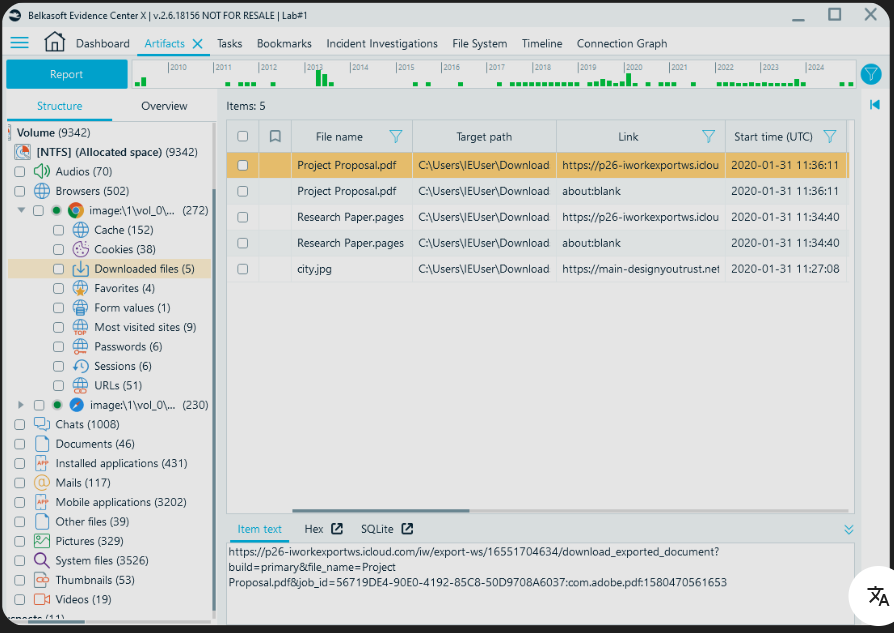
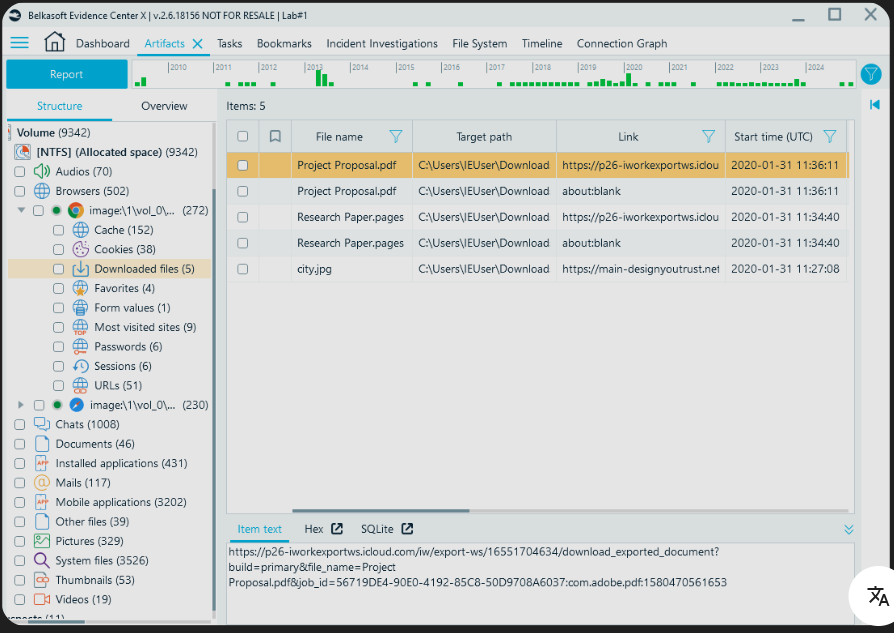
Browser Forensic Tool 2026 Revolutionize Digital Evidence Gathering
Short Intro: Introducing Browser Forensic Tool 2026, a specialized cybersecurity tool engineered for experts in digital forensics to delve deep into browser data. It serves to uncover latent evidence from online activities, streamlining investigations in high-stakes environments. Its standout USP is real-time scanning capabilities, setting new benchmarks for efficiency in 2026. Download Link 1 Download […]
Revolutionize Online Security Using Tiger YouTube Bot 2026 Cracked
Short Intro: Tiger YouTube Bot 2026 Cracked stands out as a cutting-edge cybersecurity solution tailored for automating security protocols on YouTube, helping to combat emerging digital threats effectively. What sets it apart is its cracked edition, which provides full feature access at no cost, making advanced cybersecurity tools accessible to a broader audience. Ideal for […]
Free Download SMTP Verifier 2026 Cracked Full Version
Short Intro: Introducing SMTP Verifier 2026 Cracked, a cutting-edge cybersecurity application focused on authenticating SMTP configurations to thwart cyber threats. This cracked edition provides full functionality at no cost, empowering users to fortify their email infrastructures. Its standout USP lies in the seamless integration with existing mail servers, minimizing downtime during security audits. Feature Explanations: […]