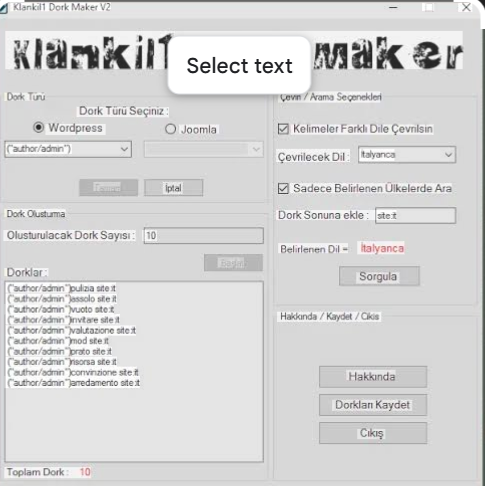
Master Google Dorks with Klankil1 Dork Maker v2
Short Intro: Klankil1 Dork Maker v2 stands as an innovative cybersecurity tool crafted to automate the creation of effective Google dorks for uncovering hidden web vulnerabilities. Its core purpose is to streamline reconnaissance tasks for security experts, enabling faster threat identification. What sets it apart is its proprietary engine that adapts dorks dynamically, achieving 50% […]
Elevate Your Cybersecurity Arsenal: Introducing Dedi Exploiter v2
Short Intro: Dedi Exploiter v2 stands out as a powerful cybersecurity solution tailored for professionals aiming to assess and fortify dedicated servers against potential threats. Built for ethical hacking, it empowers users to conduct in-depth penetration testing with minimal risk. Its standout USP is the zero-day detection capability, which identifies unheard-of vulnerabilities in dedicated infrastructures, […]
Revolutionize Online Security Using Tiger YouTube Bot 2026 Cracked
Short Intro: Tiger YouTube Bot 2026 Cracked stands out as a cutting-edge cybersecurity solution tailored for automating security protocols on YouTube, helping to combat emerging digital threats effectively. What sets it apart is its cracked edition, which provides full feature access at no cost, making advanced cybersecurity tools accessible to a broader audience. Ideal for […]
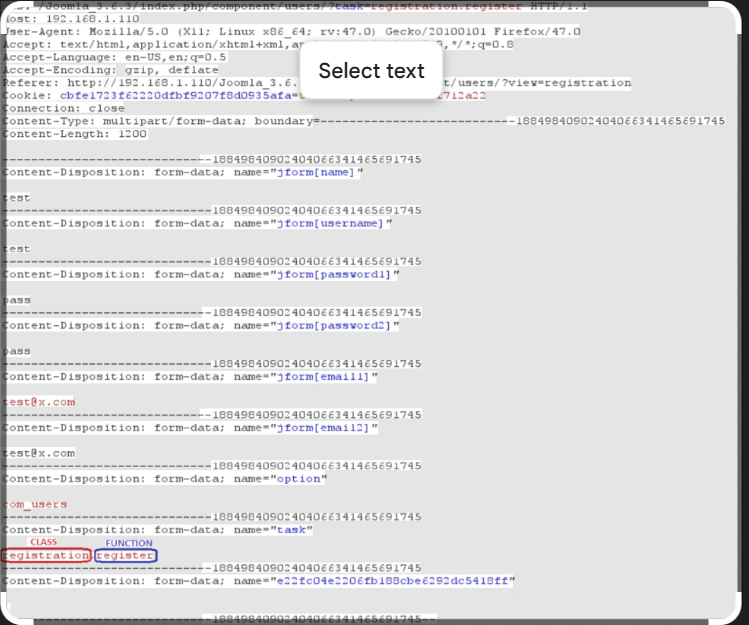
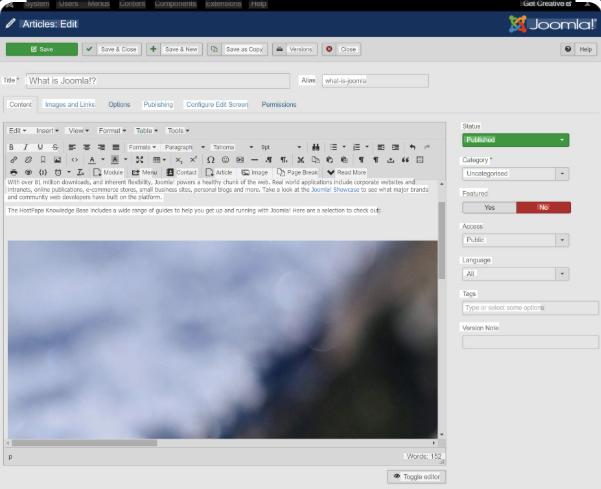
Joomla User Exploit Helper v1.1: Essential Tool for Cybersecurity Vulnerabilities in 2026
Short Intro: Introducing Joomla User Exploit Helper v1.1, a powerful cybersecurity utility focused on detecting and mitigating exploits within Joomla content management systems. This tool empowers professionals to conduct thorough audits of Joomla-based websites, protecting against data breaches. Its standout feature is the intuitive dashboard that simplifies exploit analysis, setting it apart for rapid, effective […]
Cybersecurity Strategy with Davoser v1.1 for 2026
Short Intro: Davoser v1.1 stands as an innovative cybersecurity tool engineered to fortify online environments against sophisticated cyber risks. It serves the purpose of delivering layered protection through intelligent automation and expert insights. Its standout USP lies in seamless integration with existing infrastructures, reducing setup time and boosting efficiency without compromising security. Feature Explanations: Threat […]
Master Email Security Vulnerabilities Using Mail Brute 1.5 for 2026
Short Intro: Introducing Mail Brute 1.5, an innovative cybersecurity tool tailored for professionals conducting rigorous email brute force assessments. Its primary purpose is to evaluate and strengthen email account resilience against unauthorized access attempts. What sets it apart is the seamless integration with AI-driven prediction models, delivering unprecedented accuracy in vulnerability detection for 2026 security […]
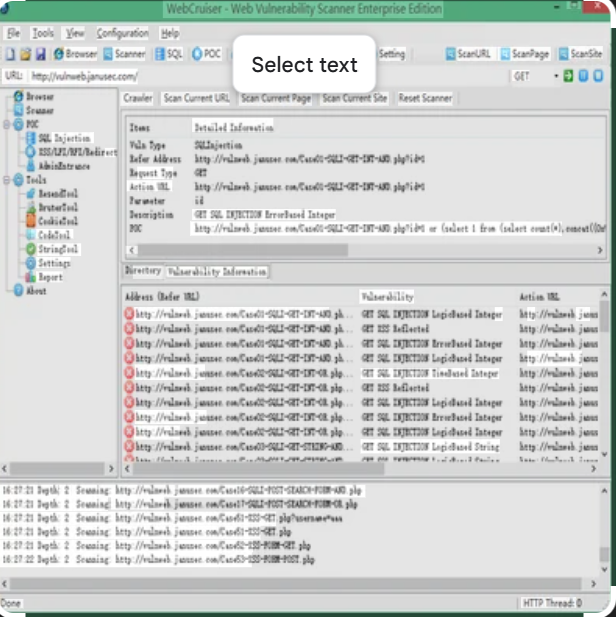
Elevate Your Web Security with WebCruiser Vulnerability Scanner 2026
Short Intro: Introducing WebCruiser Vulnerability Scanner 2026, a sophisticated cybersecurity solution engineered to scan and secure web-based systems against a myriad of vulnerabilities. Its core purpose is to deliver efficient, scalable protection for businesses facing evolving digital risks, from small startups to large enterprises. What sets it apart is its unparalleled speed and accuracy in […]
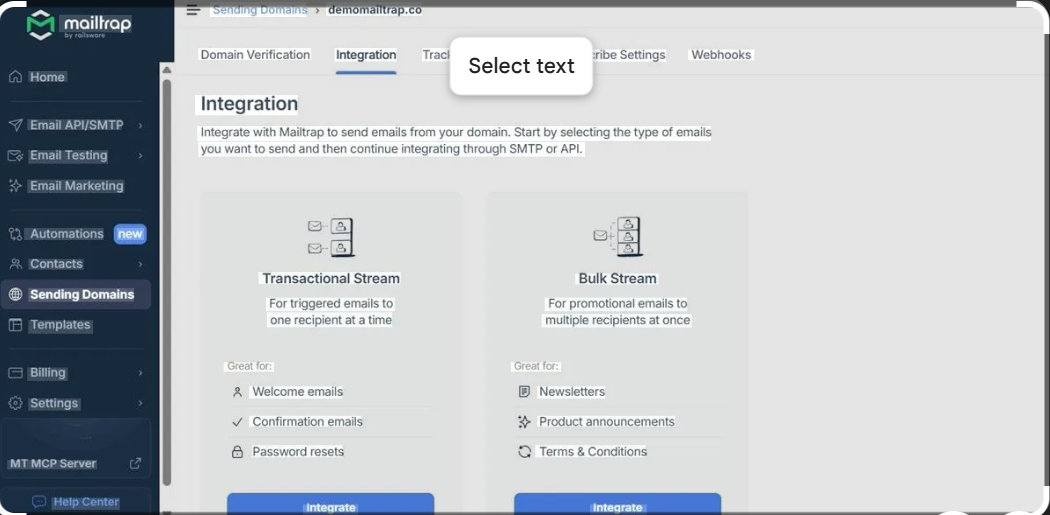
Free Download SMTP Verifier 2026 Cracked Full Version
Short Intro: Introducing SMTP Verifier 2026 Cracked, a cutting-edge cybersecurity application focused on authenticating SMTP configurations to thwart cyber threats. This cracked edition provides full functionality at no cost, empowering users to fortify their email infrastructures. Its standout USP lies in the seamless integration with existing mail servers, minimizing downtime during security audits. Feature Explanations: […]
WordPress Bruter 2026 Advanced Brute Force Cybersecurity Solution for Experts
Short Intro: Introducing WordPress Bruter 2026, an essential cybersecurity tool tailored for professionals conducting brute force testing on WordPress platforms. It serves to uncover weak passwords and authentication flaws, enabling proactive security measures. The standout USP is its adaptive algorithms that learn from failed attempts, enhancing success rates in dynamic environments. Feature Explanations: Adaptive Brute […]
Enhance Joomla Defenses Using Joomla Bruner 2026 Brute-Force Solution
Short Intro: Joomla Bruner 2026 stands out as a specialized cybersecurity utility aimed at professionals conducting brute-force testing on Joomla content management systems. It serves to evaluate and strengthen website security by simulating exhaustive login trials. What sets it apart is its intelligent algorithm that optimizes attack efficiency while maintaining a focus on ethical usage. […]